plane (in networking)
What is a plane (in networking)?
A plane is an integral component of telecommunications architecture and networks. This architecture consists of three planes, or logical entities: the data plane, the control plane and the management plane. Each plane represents a different area of network operations and carries different types of network traffic.
Networks can be represented two-dimensionally as a set of flat lines connecting various nodes. But in real networking environments, a network has three dimensions, or planes, which together determine how data moves in the network.
Networking planes -- also known as traffic planes -- represent logical separations to classify traffic based on its function in the network. Such separation enables network administrators to develop and consistently apply security policies. It also allows them to design network control functions based on the policies and implement them on the various elements in the network.
The data plane, control plane and management plane each have different characteristics, functions and security requirements in the network. They also operate at different speeds. It is especially important to understand how these planes work in a software-defined network (SDN) because it helps network administrators to use a software application to configure the network and optimize its speed in an agile manner.
Networking planes in SDN
In conventional networking, all three planes are implemented in the firmware of routers and switches. SDN decouples the data and control planes. It also removes the control plane from network hardware and implements it in software. Since there is no need to change the configuration of physical equipment, SDN enables programmatic access and consequently makes network administration much more flexible.
Moving the control plane to software also allows dynamic access and administration of the network. Network admins can shape traffic from a centralized control console without having to touch individual switches. They can also change the rules of any switch when necessary to prioritize, de-prioritize or even block specific types of data packets while maintaining a granular level of control.

What is the data plane?
In a network, the data plane is sometimes known as the user plane, forwarding plane, carrier plane, data path or bearer plane. It refers to all the processes that are responsible for forwarding packets from one interface to another -- source to destination -- based on the control plane's logic. Thus, the data plane depends on the control plane to function.
The primary function of the data plane is to carry the network's user traffic, or data packets, and transit the packets while applying some action to them. These actions are always applied on the basis of rules that are programmed into routing tables.
The data plane takes packets from one port of a switch and sends them to another port through the router. These actions happen at line speed and require inputs from the control plane to determine which ports to send packets to.
Usually, data plane traffic does not have destination Internet Protocol (IP) addresses belonging to networking devices such as routers or switches. Rather, the plane sources the traffic and then sends it on to other network-supported devices, such as PCs or servers. It is the router's job to forward these packets downstream as quickly as possible. All data plane traffic must be controlled to protect the router and network against threats that might arise from both legitimate and malicious traffic.
What is the control plane?
The control plane controls how data packets are forwarded in the network. It makes forwarding decisions and also implements other network functions, such as quality of service (QoS) and virtual local area network (VLAN).
The main function of the control plane is to create logic and to program actions for the data plane. Thus, while the data plane actually forwards the packets, the control plane determines, or controls, how the packets should be forwarded. Unlike the data plane, where packets go through a router, the packets of the control plane are locally originated by the router itself, which then processes the packets to update the routing table.
In any network, routers use multiple protocols to identify network paths. These paths are stored in the routing tables. The process of creating these tables is part of the control plane. Routers typically use these protocols to create routing tables:
- Border Gateway Protocol, or BGP
- Open Shortest Path First, or OSPF
- Enhanced Interior Gateway Routing Protocol, or EIGRP
- Intermediate System to Intermediate System, or IS-IS
The control plane includes both receive packets and transit packets. The receive packets are generated and consumed by the control processes running on the router, while the transit packets are required to maintain the network's overall performance even if they are not destined for processes running on the intermediate routers.
The control plane does not operate at wire speed, which means it operates at a lower speed than the data plane. Despite its lower speed, it plays an important role in the network because without it, the other traffic planes would not function. Router and network operations would also be disrupted. To protect the state of the network, it's crucial to secure the control plane and prevent its compromise.
What is the management plane?
The management plane, which carries administrative traffic, is considered a subset of the control plane. It is a logical entity where network devices such as switches, routers, web interfaces, command-line interfaces (CLI) and shells are configured and monitored. In this plane, the traffic used to access, manage and monitor the network elements is defined, along with all the network's provisioning, maintenance and monitoring functions.
The management plane runs on the same processor as the control plane. It always includes receive packets that are generated and consumed by the management processes running on the router.
It is just as important to secure the management plane as it is to secure the control plane to help ensure proper router and network operations. This also avoids unauthorized access and prevents attackers from compromising the IP traffic planes by taking advantage of weak passwords or unencrypted management access or by modifying traffic flows.
What is the services plane?
A services plane is considered part of the network when there are different services running over a common IP network core. This logical entity consists of the following:
- customer traffic receiving dedicated network-based services;
- private-to-public interfacing;
- firewalls;
- intrusion detection and prevention systems, or IDS/IPS; and
- QoS for voice and video.
Unlike data plane traffic that receives only native IP delivery support, the services plane includes traffic with specialized network-based functions and consistent end-to-end handling. Also, services plane traffic is generally transit traffic, so it is processed differently from data plane traffic. Administrators usually create and enforce different policies with the plane because it represents different kinds of services. Securing the plane helps to ensure stable and reliable flows of specialized traffic.
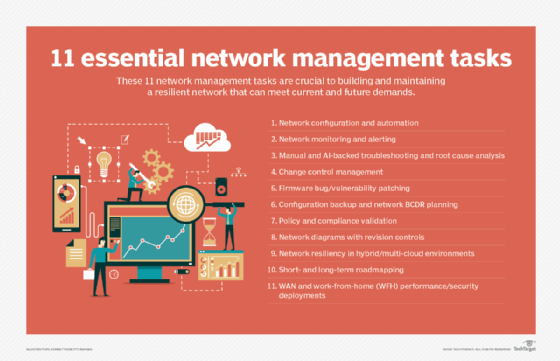
Learn about the five different types of network management and network management tasks and best practices. Explore the importance of unified, end-to-end network management and how to plan a network management strategy for multiple tools.
