polarity
What is polarity?
Polarity is when an entity contains two distinct and opposite poles that can either attract or repel each other. The term is commonly used in electricity, magnetism, chemistry and electronic signaling to describe the flow of electrons.
When there is a constant voltage -- also called an electric potential or electromotive force -- between two objects or poles, one of the objects or poles may have more electrons than the other. The pole with relatively more electrons is said to have negative polarity; the other is assigned positive polarity.
If the two poles are connected by a conductive path, such as a wire, electrons flow from the negative pole to the positive pole. This flow of charge constitutes an electric current. In physics, the theoretical direction of current flow is from a positive charge to a negative charge by convention, opposite to the flow of electrons.
Polarity in electromagnetic fields
The movement of particles that carry electric charge -- also known as charge carriers -- produces a magnetic field. In the case of an electromagnet, the charge carriers are electrons. When a direct current (DC) voltage is run through an electromagnet, it flows from the positive end to the negative end of the DC circuit. Electrons flow in the opposite direction of the current. This creates a magnetic field and magnetic polarity that has north and south poles.
A simple way to create an electromagnet is to wrap a single coil of wire around a core, such as an iron nail. The two ends of the wire are connected to the negative and positive terminals of a battery. Electrical current flows from the positive end of the battery through the wire toward the negative end. The electrons flow through the wire in the opposite direction, from negative terminal to the positive. However, it's the direction of the current that determines the polarity of the electromagnetic field. The charge travels toward the negative terminal, which is the north pole of the magnet.
Other examples of polarity
The term polarity can be used in a variety of contexts. The following are some examples of polarity:
- Digital communications. Here, polarity refers to the nature of digital signals.
- Audio engineering. In this context, it describes the direction of an audio signal.
- Chemistry. Molecular polarity refers to the movement of electrons in covalent bonds toward or away from atoms in a molecule, which affects how the molecule behaves.
- Biology. In biology, polarity refers to cell polarity, or the differences in shape, function and structure of cells.
- International relations. Here, it refers to the distribution of power in an international system.
- Opinion mining. When looking at polarity in people's behavior, it refers to sentiment analysis, which determines the level of negativity and positivity in people's online comments and discussions. For example, businesses can use machine learning to gauge opinions from social media posts.
Polarity in communications
In digital communications, data is composed of short-duration pulses called bits, or binary digits, which are the smallest units of data a computer can store and process. There are two possible states for each bit: logic 0, also called low, and logic 1, also called high. In a closed circuit, these logic elements are represented by DC voltages. A high-speed data signal varies rapidly between the low and high states. Common values are approximately +0.5 volts for low and +5 volts for high.
In some cases, different values are used, for example, -3 volts for low and +3 volts for high, or -5 volts for low and -0.5 volts for high. If both voltages have the same polarity, the signal is called unipolar; if the voltages have opposite polarity, the signal is called bipolar. Bipolar transistors are semiconductor devices that can be used for amplification.
Qubits, or quantum bits, defy the binary logic or polarity of normal bits. Qubits can exist in a state of superposition or the ability to be in multiple states at the same time.
Polarity in biology
In biology, polarity describes asymmetry. Living organisms often develop with different front, or anterior, and back, or posterior, characteristics. For instance, in human anatomy, the anterior is the chest and posterior is the back. Even simpler creatures like sponges have a distinct front and hind parts. This pattern could be extended to plants too, which have leaves and roots.
Even neurons are polarized; they have a cell body at one end and a synapse at the other. Electrical pulses only flow in one direction along the neuron's axon. In genomics and virology, RNA viruses are classified in part by the genome polarity of the molecules of which they are made.
Polarity in chemistry
The polarity of the atoms is often a primary factor in how different atoms combine to create various substances and form molecules. Examples of polar molecules include ethanol (C2H6O), hydrogen sulfide (H2S), sulfur dioxide (SO2), ammonia (NH3) and hydrochloric acid (HCl).
By contrast, nonpolar molecules do not have a positive or negative charge because their electrons are finely dispersed. Additional examples of nonpolar molecules include carbon dioxide (CO2), fluorine (F2) and hydrogen (H2).
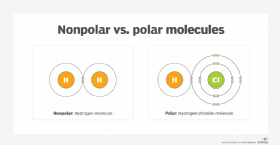
Nonpolar and polar molecules don't combine. For example, oil is a nonpolar chemical substance and water is polar. These properties are why oil and water don't mix.
Polarity plays a role in other physical properties, such as surface tension, solubility, and melting and boiling points. A liquid boils when it is heated and kinetic energy between the molecules increases to the point where the intermolecular bonds break. When water molecules are boiled it takes on a gaseous state as water vapor or steam because the hydrogen bonds between the molecules break.
The polarity of molecules determines the force of attraction between them in their liquid state. The greater the polarity, the higher a molecule's boiling point is in its liquid state. Dipole moment is a term used to describe the overall polarity of a molecule. Hydrogen chemical bonds have abnormally strong polar bonds, which explains why water boils at 100 degrees Celsius, whereas similar molecules boil at lower temperatures.
Water's large dipole moment makes it a polar solvent. In polar solvents, the bonded atoms have different electronegativity, which is the tendency of atoms to attract electrons.
Polarity can be used to describe the on or off states of bits in computing. Quantum bits subvert this paradigm. Learn about this and the basics of quantum computing to understand how this works.
