Pomodoro Technique
What is the Pomodoro Technique?
The Pomodoro Technique is a time management method based on 25-minute stretches of focused work broken by five-minute breaks. Longer breaks, typically 15 to 30 minutes, are taken after four consecutive work intervals. Each work interval is called a pomodoro, the Italian word for tomato (plural: pomodori).
Developer and entrepreneur Francesco Cirillo created the Pomodoro Technique in the late 1980s, when he was a university student and used a tomato-shaped kitchen timer to organize his study schedule. At first, he experimented with different work intervals, starting with two minutes and extending them up to one hour; he quickly realized that these were getting too long to stay focused on a task. He settled on 25-minute pomodori as the optimal time for his needs.
From this experience, Cirillo recognized that time could be turned into an ally, rather than a source of anxiety. The Pomodoro Technique essentially trains people to focus on tasks better by limiting the length of time they attempt to maintain that focus and ensuring restorative breaks from the effort. The method also helps them overcome their tendencies to procrastinate or multitask, both of which are known to impair productivity.
What does the Pomodoro Technique entail?
The Pomodoro Technique can also help individuals develop more efficient work habits. Through effective time management, they can get more done in less time, while achieving a sense of accomplishment and reducing the potential for burnout. To this end, the Pomodoro Technique includes five incremental processes to help develop a conscious and productive relationship with time:
- Pomodoro Internal Process. Develop an effective relationship with time to improve productivity.
- Pomodoro Core Process. Bring focus to the tasks in order to reach goals with less effort.
- Pomodoro Daily Process. Set up a daily routine, improve the daily work process and complete multiple tasks more effectively.
- Pomodoro Weekly Process. Set up a weekly routine, organize time more efficiently and achieve multiple goals.
- Pomodoro Team Process. Learn to adapt the Pomodoro Technique to a team setting.
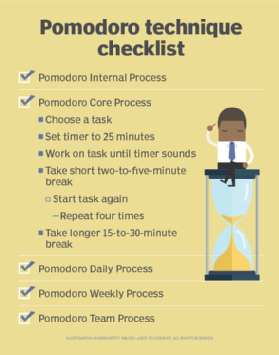
The Core Process serves as the foundation for achieving the Pomodoro Technique in a sustainable way. It defines the following five steps for staying focused on the tasks at hand throughout the day:
- Choose a task for the current pomodoro.
- Set the timer to 25 minutes.
- Work on the task until the timer sounds, then record completion of the pomodoro.
- Take a short break; start with five minutes but know that it can be as little as two minutes.
- After four pomodori, take a longer break; this is generally 15 to 30 minutes.
For each pomodoro, set aside time for recap and review to help move seamlessly from one pomodoro to the next. More importantly, take whatever steps necessary to stay focused on a task during the pomodoro and avoid interruption. Individuals need to protect their pomodoro from both internal and external distractions. Avoid checking email, social network accounts, weather reports, news outlets or any other diversions that can pull attention away from the task at hand.
Various implementations of the Pomodoro Technique use different time intervals for task and break segments. For the breaks, it is strongly advised that the individual selects an activity that contrasts with the task. Someone working at a computer, for example, should step away from the desk and do some kind of physical activity.
See also: virtual meeting fatigue, timeboxing, Inbox Zero, Hofstadter's law, Eisenhower Matrix.