predictive text
What is predictive text?
Predictive text is an input technology that facilitates typing on a device by suggesting words the user may wish to insert in a text field. Predictions are based on the context of other words in the message and the first letters typed. The user simply taps on a word instead of typing it out on a computer keyboard or mobile device's soft keyboard. Predictive text can significantly speed up the input process.
Predictive text uses machine learning to curate a glossary of words and phrases that a user often types. The predictive text feature then ranks these commonly used words and phrases to guess when they will be used again.
One of the earliest applications for predictive text was T9 (text on 9 keys). T9 was invented in 1995 and made typing on mobile phones and other small devices easier. Prior to T9, typing on a mobile device required multitapping, where the user had to tap numbers up to four times to register letter characters.
T9 improved the mobile user experience by associating groups of letters on each phone key with words in a dictionary. Software in the device correlated sequences of key presses with words in the dictionary and prioritized predictions by frequency of use.
Although predictive text technologies are becoming increasingly sophisticated, the software is still notoriously error-prone. Erroneous predictive text input on Apple devices is sometimes referred to as the Cupertino effect. The name was inspired by the way early spell checkers would change the word cooperation to Cupertino, which just happens to be the city in California where Apple has its corporate headquarters.
Types of predictive text systems
Some examples of predictive text systems for mobile devices are the following:
- Apple QuickType. Apple's predictive text feature has a machine learning component that enables the software to build custom dictionaries. This allows the software to remember things such as whether the user uses slang when communicating with specific people and adjust its text predictions accordingly.
- Google Gboard. Google's keyboard application comes preinstalled on most Android devices. Gboard is sometimes also called the predictive text suggestion strip, word suggestion or auto-suggest. Gboard uses federated learning to train its prediction model on user behavior. Android first included a predictive text bar with Android 4.1 Jelly Bean in 2012.
- Typewise. This predictive text application is compatible with both the Apple iOS and Android operating systems (OSes). Typewise also offers an AI writing assistant.
There are also many applications of predictive text outside of mobile messaging apps. Some examples include:
- Word processing. Microsoft Word and other word processing applications make suggestions as a person types in a document.
- Search engines. Google and other search engines use predictive text to guess a search query as the user types it in. The search engine will guess commonly searched phrases and then autocomplete the search query with either a previously searched phrase or suggestions based on commonly searched queries.
- Email. Gmail Smart Compose helps users quickly respond to emails and inserts stock phrases, like greetings and sign offs into emails. Microsoft Outlook has a similar text suggestion feature.
- Operating systems. Windows comes with a built-in predictive text function. When enabled, it is applied to applications running on the OS. The feature is disabled by default on Windows computers.
How predictive text uses machine learning
Predictive text uses machine learning to guess a writer's next word based on their writing style. As the user types, the machine learning algorithm notes commonly used words and creates a personalized dictionary.
The algorithm makes repeated observations and becomes attuned to the user's style. It also notes of the last few words the user wrote and narrows its suggestion based on those words. This is known as context-sensitive text prediction.
Predictive text uses language models to understand written input and make recommendations. Language models, such as Open AI's GPT-3, are used by search engines, behavioral marketers for sentiment analysis, content generation tools and chatbots.
How to use predictive text
Predictive text makes messaging or writing more efficient. It can also act as a spell check device in text messaging. The first step in using predictive text is to enable it on the user's mobile device.
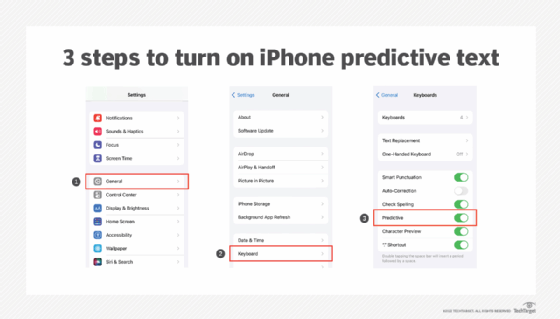
Predictive text on an Apple iPhone
On iPhones, predictive text is enabled by default. If it is off, do the following to enable it:
- Launch the Settings
- Tap General > Keyboard.
- Toggle on the switch next to Predictive.
When predictive text is turned on and a user starts to type, a bar above the keyboard will display suggested words and phrases. The user can click a suggested word as it appears in the suggestion bar to add it to the message.
For example, a user types the word happy and the strip displays the words birthday, bday and holidays as suggestions for the next word. If a user is in the process of typing happy and has typed the letters hap, the suggestions might be happy, happened and happiness to complete the word.
In some cases, predictive text will suggest emojis when a word is typed. For example, if the user types fire, a fire emoji is suggested alongside text suggestions. If the user types happy, a happy face emoji will be suggested.
Predictive text on an Android device
On Android devices, Gboard predictive text is usually enabled by default. If it isn't turned on, Android users can follow these steps:
- Launch the Settings
- Tap System > Languages and input > On-screen keyboard > Gboard.
- Tap Text correction.
- Toggle on Show suggestion strip.
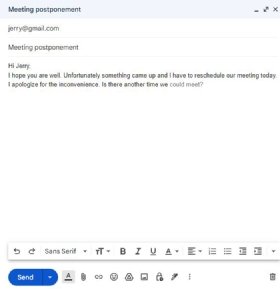
Predictive text in Gmail
Gmail's Smart Compose predictive text feature is slightly different on a laptop or desktop computer from predictive text on mobile devices. The user begins to type a word in the body of an email, and Smart Compose finishes the word it thinks is being typed in a lighter font. Smart Compose and its accompanying personalization option are enabled by default in Gmail.
To turn Smart Compose on or off follow these steps:
- Open Gmail.
- Click Settings > See all settings.
- Under General, scroll to Smart Compose.
- Select either Writing suggestions on or Writing suggestions off.
Smart Compose also learns from a user's writing style with personalized suggestions. The following four steps will turn personalized suggestions off:
- Open Gmail.
- Click Settings > See all settings.
- Under General, scroll to Smart Compose
- Select Personalization on or Personalization off.
Predictive text in Microsoft Word
To enable predictive text on Microsoft Word follow these steps:
- Open Word.
- Click File > Options.
- Click
- Check the box next to Show text predictions while typing.
Similar to Gmail, users will see suggested text in a lighter font displayed as they type.
How to turn off predictive text
Turning off predictive text is usually the same steps as turning the function on, but with the opposite final action. The following steps will turn off predictive text in various devices:
IPhone
- Launch the Settings
- Tap General > Keyboard.
- Toggle the switch next to Predictive
To turn off the predictive text feature while typing, iPhone users can:
- Hold the emoji icon to the left of the spacebar on the QWERTY keyboard.
- Tap Keyboard Settings.
- Toggle the switch next to Predictive
Android
- Launch the Settings
- Tap System > Languages and input > On screen keyboard > Gboard.
- Tap Text correction.
- Toggle off Show suggestion strip.
Other ways to use predictive text
Predictive text can be used to provide shortcuts to insert longer phrases or sentences in text. On iOS, the following steps enable this capability:
- Launch the Settings
- Tap General > Keyboard.
- Tap Text Replacement.
- Tap + in top right corner.
- Enter text that is desired in the Phrase
- Enter the misspelled trigger word or shortcut phrase in the Shortcut text input
- Click Save.
For example, if the user enters On my way! in the Phrase field, and omw in the Shortcut field, On my way! will appear in the suggestion bar when a user types omw.
This approach can be useful for commonly misspelled words as well. For example, a user who is apt to misspell perceived would enter the correct spelling of that word in the Phrase field and the common misspelling percieved in the Shortcut field. When they type percieved, predictive text will suggest perceived.
Android's Gboard also has a "Block Offensive Words" feature. When enabled, it prevents the predictive text features from suggesting profanity to the user.
To remove words from Gboard predictive text, users can:
- Launch the keyboard by clicking a text field.
- Begin typing.
- Tap and hold the undesired suggestion.
- Drag the word to the trash can icon that appears.
Predictive text is often used in customer service applications to help agents quickly craft responses to customers. Learn how this and other AI technologies are used in customer service to improve customer experience and expedite workflow.