private IP address
What is a private IP address?
A private IP address is a range of non-internet facing IP addresses used in an internal network. Private IP addresses are provided by network devices, such as routers, using network address translation.
Internet Protocol (IP) addresses identify a device on either the internet or a local network. IP addresses also enable information to be sent between devices on a network.
Private IP addresses are commonly used for local area networks in residential, office and enterprise areas. Every device that connects to an internet network -- such as computers, smartphones, tablets or printers -- will have a private IP address. Routers need a way to identify these devices, and the devices may also need to identify each other, which is where private IP addresses come in. Private IP addresses are generated by a router for identification.
Private IP addresses were originally designated to delay the exhaustion of IPv4 addresses -- one of the main types of IP addresses. Originally it was thought that IPv4's 32-bit IP addressing system -- with 4,294,967,296 theoretical IP addresses -- would be adequate for all purposes. But as more internet-connected devices were produced, it became apparent that something had to fill the gap between IPv4 and a future system. Private IP addressing and network address translation began filling that initial gap with a range of private IP addresses. Later, a new addressing system, Internet Protocol Version 6 (IPv6), was introduced. IPv6 increases IP address lengths from 32 bits to 128 bits and is 1,028 times larger than the number of IPv4 addresses.
Private addresses can be assigned by the router using the Dynamic Host Configuration Protocol or be manually set, after which the addresses can communicate with one another through the router.
What is a private IP address used for?
Private IP addresses are commonly used for residential and corporate networks, as the addresses cannot be seen outside the private network. Internet service providers (ISPs) may also allocate a single routable IPv4 address to residential customers. To translate that one address to multiple addresses, so multiple devices can have the assigned address, a network address translator/port address translator gateway is used. This method can connect multiple hosts.
Corporate networks use private IP addresses for security, since they make it difficult for an external host to connect to a system. Organizations also use private IP addresses to restrict internet access to internal users, which helps increase security.
How can you check your private IP address?
Most individuals do not need to know their IP address, but in some scenarios the knowledge comes in handy, such as when connecting a computer to another device on the network.
The steps for finding a device's IP address differ by platform.
- Windows. Search for cmd in the Windows search bar, then in the command line prompt, type ipconfig to view the private IP address.
- Mac. Select system preferences, then click on network to view the private IP address.
- iPhone. Select settings. Go to Wi-Fi, tap the i that appears next to the network it is connected on, and the IP address will display under the DHCP tab.
- Android. Select Settings, go to About, tap on Status and the IP address should be visible.
Other devices can be checked from the connected router. The steps to do this will differ by router, however.
What are the different private IP address ranges?
Private IP addressing uses both IPv4 and IPv6 addresses.
Private IPv4 addresses have the following class configurations:
- Class A IP addresses. Configurations range from 10.0.0.0 to 10.255.255.255. This class is for large networks and has 8 bits for the network and 24 bits for hosts.
- Class B IP addresses. Configurations range from 172.16.0.0 to 172.31.255.255. This class is for medium networks and has 16 bits for the network and 16 bits for hosts.
- Class C IP addresses. Configurations range from 192.168.0.0 to 192.168.255.255. This class is for smaller networks and has 24 bits for the network and 8 bits for hosts.
The range of private IP addresses seems relatively small because they can be reused on different private networks without consequence. This differs from public IP addresses, which all need to be uniquely identifiable.
IPv6 private address ranges include the following:
- fc00::/7 address block. These are reserved IP addresses from the Internet Assigned Numbers Authority for unique local addresses.
- fec0::/10 address block. These are for deprecating site local addresses.
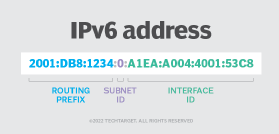
IPv6 addresses are written in hexadecimal, which uses four bits, meaning an IPv6 address is made up of 32 hexadecimal digits. The numbers are grouped in fours, with a total of eight blocks, or groups.
What are the differences between a private and public IP address?
Both public and private IP addresses have attributes indicative of their roles. For example, differences between public and private IP addresses include how private IP addresses are used for communicating within a private network, or with other devices in a home network or office. They cannot be directly contacted over the internet. Meanwhile, public IP addresses are used to communicate over the public internet, outside a private network. Public IP addresses are unique and cannot be reused unlike private IP addresses, which can be reused. Private IP addresses are assigned to a device by a router within the network, while an ISP assigns public IP addresses. In addition, public IP addresses can be any combination of numbers that do not fall within private IP address ranges.
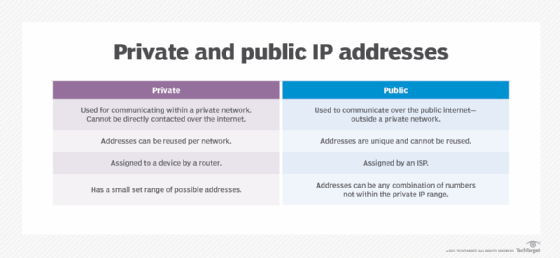
Private IP addresses also have an extra layer of security because they are only located within private networks, and not to the internet as a public IP address would be.
Learn the differences between IPv4 and IPv6, and how many addresses IPv6 supports.