program counter
What is a program counter?
A program counter is a special register in a computer processor that contains the memory address (location) of the next program instruction to be executed. Before the CPU fetches an instruction from memory, it references the program counter for the correct memory address. After the CPU fetches the instruction, it increases the program counter by 1 so it points to the next instruction in the program's sequence.
A program counter is sometimes referred to as an instruction pointer or instruction address register. The program counter makes it possible for the CPU to process a program's operations in an orderly fashion. A program is made up of a set of instructions that tell the CPU which steps to take and in what order. Each instruction is stored at a specific address in memory. The CPU fetches each instruction from memory one at a time, using the program counter as its guide.
What is the purpose of the program counter and instruction register?
The program counter and instruction register, both different types of registers, play a vital role in a processor's instruction cycle. A register is a small data holding place that the processor can access quickly.
The CPU knows which instruction to fetch from memory by referencing its address in the program counter. The instruction register holds the instruction after it is fetched from memory. Once the instruction is in the instruction register, the CPU can decode and execute it. In this sense, the instruction register is dependent on the program counter to ensure that the instruction register contains the correct instruction at any given time.
During a normal instruction cycle, the CPU fetches, decodes and executes one of the program's instructions. Before fetching the instruction from memory, the CPU retrieve's the instruction's address from the program counter. In this way, the CPU knows which instruction to retrieve. For example, if the program counter shows an address of 0851, the CPU knows that it should retrieve the program instruction located at the 0851 memory address.
After determining the correct address, the CPU fetches the instruction, places it into the instruction register, and increments the program counter by 1. The CPU then decodes the instruction in the instruction register. If the instruction is complete, the CPU executes the instruction and continues with the next instruction cycle.
The following image provides a simple overview of the roles that the program counter and instruction register play in the instruction cycle. Here, the program counter shows a memory address of 0005. This causes the CPU to fetch Instruction 6 from memory and load it into the instruction register. The CPU then updates the program counter, decodes Instruction 6, and executes the instruction. The program counter should now read 0006, which points to the next instruction.
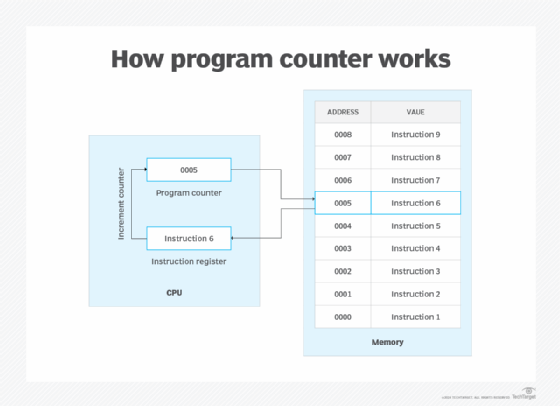
The figure shows the CPU and memory at their most basic. It does not include components such as the CPU's accumulator or arithmetic logic unit (ALU). The figure also indicates that each instruction fits neatly into a single memory space. In many cases, however, instructions are too large for a single memory location and must be split across multiple addresses.
Today's processors easily accommodate instructions that span multiple memory addresses. When the CPU decodes an instruction in the instruction register, it determines whether the instruction is complete. If it's not, it will fetch the next part of the instruction, again referring to the program counter. After all the instruction's parts are fetched into the instruction register, the CPU will execute the instruction in its entirety and then continue to the next instruction cycle.
Another situation that a CPU routinely encounters is a program's control flow logic. Such logic typically requires the processor to pull its instructions from memory in a nonsequential order. For example, the program might include a function call or conditional loop that requires access to specific instructions that are not next in line, because they're stored in memory.
When the CPU encounters this issue, it updates the program counter to the location specified by the current instruction. Then, when the CPU is ready to launch the next instruction cycle, it can fetch the address from the program counter because it now points to the correct location in memory.
If a computer is restarted or reset, the program counter normally reverts to 0.
Learn the differences between the CPU (central processing unit), GPU (graphics processing unit) and DPU (data processing unit), their use cases and how they help accelerate data center workloads. Explore how improvements in CPU features can help shape server hardware selection.
