provisioning
What is provisioning?
In the context of IT and computing, provisioning refers to the process of setting up IT infrastructure and providing access to authorized users to the various resources that are part of the infrastructure. The term is used in a variety of contexts in IT, including grid computing, servers, storage, applications and network components.
Generally speaking, provisioning simply means providing or making something available to something or someone. In enterprise IT settings, the someone represents authorized users who need to access one or more hardware or software resources, such as servers, applications, storage devices, edge devices and so forth. Before these resources can be deployed and used, they must first be provisioned, which is why provisioning is one of the first steps in the IT deployment process.
Once a system or device has been provisioned, it is configured per a user's or organization's requirements. It is important to note that provisioning and configuration are not the same thing and both steps are required to deploy an IT resource to make it accessible and usable. Post-provisioning and post-deployment, resources are maintained over their lifetime to ensure they remain useful, functional and perform as expected by the organization.
5 main types of provisioning
Modern enterprise IT environments might be extensive and complex with scores of components, many of which are interconnected. To ensure the environment is properly set up, numerous elements must be properly provisioned, requiring the following types of provisioning.
1. Server provisioning
Server provisioning is the process setting up different types of servers, both physical and virtual. The process might involve file servers, web servers, application servers, mail servers and other specialized servers. In addition to setting up the hardware, server provisioning installs the software required by each server, including operating systems, applications and middleware. The provisioning team also collects information about the server's intended use, defines its desired state per business requirements, and connects each server to the required network and storage components to make it operational and business-ready.
2. Network provisioning
Network provisioning sets up the various components that will be part of the enterprise network. Typically, these include routers, switches, firewalls and access points, among others. The provisioning staff will also allocate IP addresses, set up access to devices and servers for authorized users, and set up security systems for access control and to protect the network. As part of the provisioning process, they might also perform operational health checks.
3. User provisioning
User or account provisioning is required to set up, modify or delete user accounts within the IT infrastructure. These accounts might be for email, applications, databases and other IT resources. Identity management is an important aspect of user provisioning, and it involves setting up authorization and authentication checks. Role-based access control (RBAC) is often used during user provisioning. With this approach, a user is given access rights to specific resources based on their role within the organization and their specific work requirements.
When a user is provisioned, their access rights, levels and privileges are set up in the network. The exact opposite happens when they are deprovisioned, meaning their access rights are revoked. Provisioning usually comes into play when a user such as an employee joins the organization -- known as onboarding -- or changes their role or responsibilities. Deprovisioning is typically done when a user is leaving or has left an organization. Both processes are essential to ensure that authorized users can access the resources they need to do their work and to then protect the organization from the security risks inherent in granting access to IT resources to human users -- especially if those users are no longer authorized.
4. Application and service provisioning
Application provisioning sets up the enterprise applications and services users might need in their day-to-day work. In addition to provisioning the apps, the IT team also monitors the apps, manages app-related data and looks for ways to optimize their performance. Furthermore, they will set up user accounts and credentials and deploy custom configurations as required by users and the business.
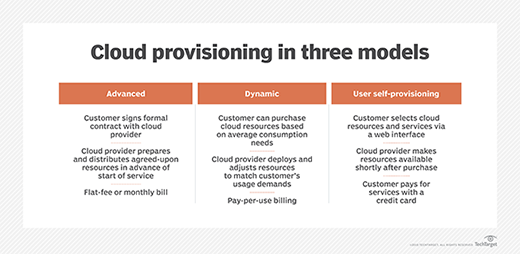
5. Cloud provisioning
Organizations that migrate either partially or completely to cloud computing must properly provision cloud resources and data to ensure that cloud-based resources are accessible and usable for the right users. During provisioning, the cloud infrastructure is set up, along with the various resources, services and applications users will need to access.
What is automated provisioning?
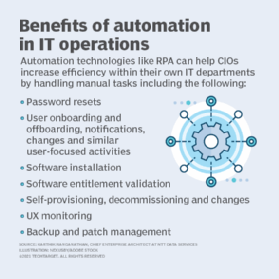
As IT environments expand and resource needs change, manual provisioning can be a cumbersome and time-consuming endeavor for IT teams, especially because many steps must be repeated. Automation provides a more efficient and faster way to provision infrastructure using predefined templates and procedures. Little or no human intervention is required.
Infrastructure as code (IaC) is one way to leverage the benefits of automated provisioning. With IaC, all infrastructure provisioning requirements and specifications are stored in configuration files. Codifying these requirements means the required environment can be easily provisioned by running a script. Moreover, the same environment will be provisioned every time, since the configuration files will function as a reusable template. Codifying infrastructure makes the provisioning process faster and more efficient. It also prevents anyone from provisioning resources in an ad-hoc or non-transparent manner -- a situation that can create policy issues or serious security vulnerabilities in the IT environment.
Benefits of automated provisioning
Automated provisioning can save time and money, and also reduce the errors common with manual processes. It can speed up the time-to-market of new IT resources and services, and let the IT team focus on more strategic activities instead of repetitive tasks.
Some of the other benefits of automated provisioning include the following:
- Makes it easier to set up more consistent and scalable IT environments.
- Authorized users can access the resources they need faster and without interruptions.
- Fewer errors, so less time is spent on troubleshooting and root cause analyses.
- Fewer chances of misconfigurations and potential business disruptions.
- A more secure environment that is less vulnerable to cyber attacks and data breaches.
- Easy to control who has access to which resources; this prevents unauthorized or malicious users from accessing business-critical or sensitive resources.
- Lower operational effort and cost during provisioning and deprovisioning.
Provisioning in telecommunications
In telecommunications, provisioning refers to providing telecommunications service to a user by setting up the service and supplying the required equipment, wiring and transmission facilities. It is the fourth step of the telecommunications sequence called OAM&P for operations, administration, maintenance and provisioning. The term provisioning is often used as a synonym for configuring, as in "telecommunications lines must be correctly provisioned to work with the customer's equipment and enabled for various options the customer has chosen."
In a traditional telecommunications environment, there are three types of provisioning: circuit provisioning, service provisioning and switch provisioning. In a wireless environment, provisioning refers to service activation and involves programming various network databases with a customer's information.
Check out network capacity planning and provisioning tips, and learn more about cloud provisioning and bare-metal provisioning.
