
recommendation engine
What is a recommendation engine?
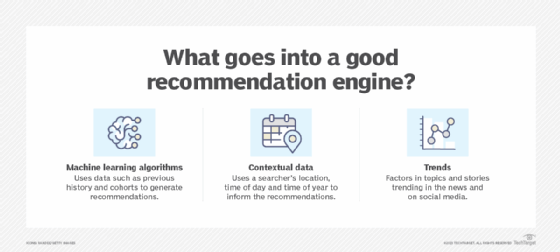
A recommendation engine is a system that gives customers recommendations based upon their behavior patterns and similarities to people who might have shared preferences. These systems, also known as recommenders, use statistical modeling, machine learning, and behavioral and predictive analytics algorithms to personalize the web experience.
E-commerce companies, social media platforms and content-based websites frequently use recommendation engines to generate product recommendations and relevant content that matches the characteristics of a particular web visitor. They are also used to suggest products that complement what a shopper has ordered. Search engines are a popular type of recommender, using a searcher's query and personal data, such as their location and browsing history, to generate relevant results.
A strong recommendation engine can improve a user's experience, increase conversions by turning browsers into buyers, boost revenue per order and build customer loyalty. The global recommendation engine market is expected to grow to $54 billion by 2030 from $3 billion in 2021 with a compound annual growth rate of 37%, according to Straits Research.
How do recommendation engines work?
Recommendation engines are software systems that apply algorithms and data analysis to make sense of data gathered about web visitors, customers and prospects. Recommenders use this understanding to suggest products these people are likely to buy or content they might be interested in.
This article is part of
A guide to artificial intelligence in the enterprise
These engines typically have four recommendation stages:
- Data collection. Organizations collect relevant data about a visitor. Data collection involves two types of data: implicit and explicit. Implicit data includes page view and time-on-page information. Explicit data is unstructured data, such as user comments, ratings, reviews, and likes and dislikes.
- Storage. Data is held in a database, data warehouse or customer data platform before being analyzed. The type of storage platform option used depends on the data type used and the amount of data. Picking the right type of storage enhances a recommendation engine's performance and scalability.
- Analysis. A recommendation algorithm analyzes customer data. There are various analytic techniques, such as similar user analysis where a person is defined by their characteristics and made part of a cohort with shared preferences.
- Filtering. Irrelevant information is filtered out of the data to improve the accuracy and relevancy of the recommendations.
What are recommendation engines used for?
Companies and organizations using recommendation engines do so for different purposes.
E-commerce companies use recommendation engines to anticipate and guide customers to better product choices for their needs, to make more purchases and to do repeat business. Companies such as Netflix and Amazon use recommendation engines to customize home screens with relevant product and content suggestions. For example, after a customer buys a book on Amazon, the company recommends books on similar topics, written by the same author or that other customers have subsequently purchased. Netflix uses a viewer's history, cohorts and emotional analytics to recommend content they are likely to enjoy.
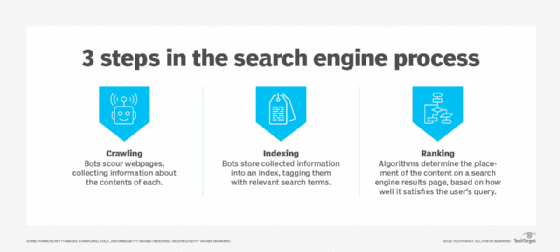
Search engines use recommendation engines to return relevant content based on a user's search query. For example, Google uses a person's location, browsing history and other types of metadata to generate real-time results. Google and other search engines also use their recommendation engines to collect valuable data about a particular user, packaging a user's searches and selling this information to advertisers in what's referred to as surveillance capitalism.
Social media platforms such as Facebook, Instagram, TikTok and Twitter use recommendation engines to suggest new content and people to follow.
Artificial intelligence for IT operations (AIOps) uses recommendation engines to analyze data from distributed networks and recommend solutions. AIOps automates problem detection in IT infrastructure.
What are the different types of recommendation engines?
Different types of recommendation engines use various metrics. The most common types of recommendation engines include the following:
- Collaborative filtering. Streaming services commonly use this filtering method. Collaborative filtering collects data on user activities and behaviors, and uses it to define preferences and predict future behavior. Recommendations are made based on the user's similarity to other people and the assumption they might like related items or actions. E-commerce sites use this type of recommender to suggest products within certain categories. It requires a lot of maintenance to update and keep accurate, making it difficult for high-volume businesses.
- Content-based filtering. This analytical approach compares a person's preferences to descriptions of products or items. Item descriptions include keywords that are used to track and define user behavior. This method assumes that if a person likes an item, they are likely to want a similar one that the content-based recommender suggests.
- Hybrid recommendation systems. These systems combine elements of collaborative and content-based filtering. The hybrid approach is considered the most accurate recommendation engine.
Recommendation engine benefits and drawbacks
The benefits of recommendation engines include the following:
- Increases the number of items a customer buys or a visitor looks at, driving revenue growth and traffic volume.
- Increases customer conversion.
- Improves customer experience.
- Encourages cross selling, repeat business and customer retention.
- Builds customer loyalty.
Recommendation engines come with several challenges:
- They depend on the quality of data, meaning incomplete or linguistically ambiguous data can affect the relevancy of recommendations.
- They struggle with certain types of unstructured data such as images.
- They have difficulty incorporating time into their models, such as seasonal preferences.
- They have difficulty assessing new users where there's history to draw from. This is known as the cold start problem.
- Customer reactions to suboptimal recommendations can be difficult to identify and track.
- Biases in artificial intelligence (AI) and machine learning algorithms can lead to inaccurate recommendations.
- Compliance rules can make it difficult for organizations to gather and store data.
- Some users may choose not to opt into an organization's data collection efforts out of privacy concerns.
- Companies with large product and service portfolios can end up with larger data sets than their database and storage architectures can accommodate.

The future of recommendation engines
Recommendation engines depend on technology that is relatively new and evolving, such as machine learning, deep learning, AI and big data. The development of deep learning and neural networks aims to improve the ability of recommendation engines to incorporate seasonal preferences and record users' reactions to suboptimal recommendations. This will enable these engines to generate more detailed and accurate user profiles.
Applications and techniques such as AI-driven natural language processing (NLP) are also affecting the future of recommenders. Improvements in NLP's ability to understand unstructured text and data is improving the accuracy of the recommendations these engines provide.
Search engines like Bing and Google are starting to incorporate generative AI capabilities. These programs can generate original, real-time answers to search queries instead of returning pages of relevant results by different authors. This user-based technology is a significant development for recommenders, but it comes with its own rewards and challenges.
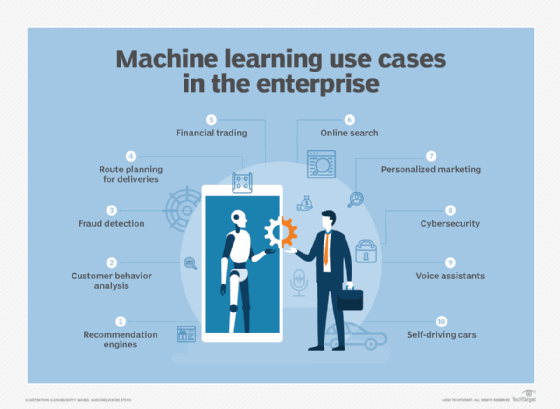
Recommendation engines are an important application of machine learning systems. Learn more about the use of machine learning in the enterprise.
