retina scan
What is a retina scan?
Retina scanning is a biometric authentication technology that uses an image of an individual's retinal blood vessel pattern as a unique identifying trait for access to secure installations.
A retina scan requires the subject to focus on a single point for 15 seconds. Although it is difficult to fake the unique patterns of each person's blood vessels in their retina, it's not foolproof. This is because some sophisticated techniques can be used to bypass a retina scanner. For example, someone can potentially spoof the scanner by creating a fake retina. However, that is considered to be highly complex and resource-intensive.
What is a retina scanner?
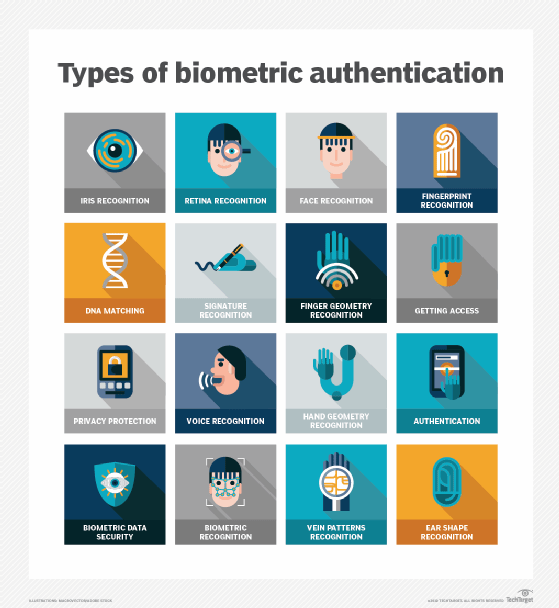
A retina scanner is a biometric verification tool. It captures the unique patterns of an individual's retinal blood vessels and identifies them through one or more distinguishing biological traits. Other unique identifiers used by different biometric verification technologies include fingerprints, hand geometry, earlobe geometry, retina and iris patterns, voice waves, DNA and signatures.
How does retinal scanning work?
Retina scanners use a low-powered infrared light beam that is directed into the eye. Compared to the surrounding tissue, the light is absorbed differently by the retinal blood vessels, creating a unique pattern that is then captured by a sensor and converted into a digital image.
This retinal image with unique blood vessel patterns is like a fingerprint and can be ideal for identification and verification purposes. Because the retina decays so quickly after death, retinal scans can only be performed on a living human.
What is retina scanning used for?
Retina scanners are commonly used in high-security access control for restricted areas, border security and immigration control, criminal investigations and suspect identification, military bases, and other high-security locations due to their strength as a security measure.
Retina scanning goes back as far as 1935 in conception by Doctors Carleton Simon and Isadore Goldstein. Commercialized use began in 1984 with the company Eyedentity, which pioneered the first devices that used retina scanning technology.

What is an iris scan?
Iris scanning or iris recognition is a form of biometric identification technology that focuses on the unique patterns of the iris of the eye for individual identification or verification. An iris scanner uses near-infrared cameras to capture detailed images of the iris or the colored ring around the pupil.
Since the iris comprises intricate and unique patterns such as striations, freckles and crypts, it can be used to identify and verify an individual. These patterns develop before birth and remain stable throughout one's lifetime. The iris image can be analyzed using specialized software that extracts mathematical representations of the patterns and creates a unique iris code for each individual.
Retina scan vs. iris scan
Both retina scanning and iris scanning are biometric technologies used for identification or verification. However, they are not the same. For example, retinal scanning focuses on the retina or the light-sensitive layer at the back of the eye. Iris scanning concentrates on the colored part of the eye or the iris.
Retinal scanning requires a person to position their eye close to an eyepiece. Once in position, a low-powered infrared light beam is directed into the eye to capture the retinal image. In contrast, iris scanning uses near-infrared cameras to capture a high-resolution image of the iris from a distance. The process is like taking a picture.
Although some smartphone apps claim to be based on retina scanning, they are usually based on iris scanning.
What is retinal imaging?
Unlike retinal scans and iris scans, retinal imaging is a diagnostic tool used by ophthalmologists or eye doctors to examine the back of the eye, the retina. Retinal image scanners provide a detailed view of the retina's blood vessels and also important structures like nerve fibers. Retinal imaging can help ophthalmologists detect and treat various eye conditions and diseases. Retinal imaging is not the same as retinal scans used in biometrics. It is a comprehensive eye exam. Instead, it's a valuable tool that can help eye doctors diagnose and monitor different eye conditions.
What can retinal imaging detect?
Retinal imaging helps doctors identify and treat a number of diseases. Some of the leading conditions detected by retinal imaging are discussed below.
Age-related macular degeneration (AMD) is one of the leading causes of vision loss in older adults. Retinal imaging can help detect AMD early by identifying common characteristics, such as drusen (yellow deposits) and changes in the macula (the central part of the retina responsible for central vision).
High blood pressure detection is possible with retinal imaging. We can do this by identifying narrowing or hardening blood vessels.
Diabetic retinopathy, a complication closely connected to diabetes, can damage the blood vessels in the retina. Retinal imaging helps detect early signs of diabetic retinopathy by identifying bleeding, leakage of fluid and new blood vessel growth.
A macular hole is a small hole that can develop in the macula, often detected with retinal imaging. It causes blurred vision and makes seeing fine details challenging.
Is retinal imaging necessary?
A medical professional decides whether retinal imaging is necessary based on several factors. These include age, medical history and current eye health. As retinal imaging isn't a comprehensive eye exam, a doctor will have to perform other tests to assess overall eye health.
Whenever recommended, retinal imaging can provide many benefits. For example, the early detection of eye diseases. This can lead to timely treatment and better outcomes. Furthermore, it can also help monitor existing eye diseases and track their progress.
Learn about biometric payments, which are real-world applications of biometric authentication technology for financial transactions. See why biometric interfaces unlock new capabilities and risks with IoT sensors and how a major facial recognition supplier built a system to identify masked faces.
