Guide to building and executing an MSP business model
This managed service guide provides an overview of how to get started in the MSP business, covering the basics of building a service provider and the challenges in doing so.
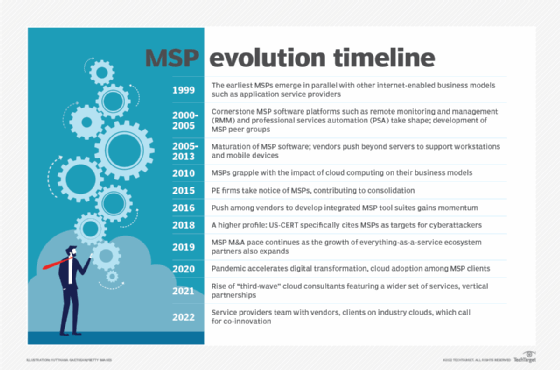
The MSP business model emerged in the late 1990s, a product of the internet's meteoric rise, and has matured into a widely recognized mechanism for delivering IT services.
Awareness of managed service providers has grown among customers, from SMBs to enterprises. MSPs are called on to provide services such as remote monitoring and management, cloud consulting and migration and cybersecurity. The increased visibility of MSPs, and their recurring revenue streams, have made them an attractive target for investors.
Prospects for future growth are strong, especially now that more customers rely on IT to provide products and services in a rapidly digitalizing world.
Benefits and Challenges
Entrepreneurs considering the launch of an MSP business, or investors eyeing MSPs as an investment opportunity, should consider the pros and cons of managed IT services.
First, we'll take a look at the main benefits.
Predictable, recurring revenue. Managed services are sold as a subscription, with customers paying a monthly fee. This approach provides a consistent flow of monthly recurring revenue (MRR) for the MSP, in contrast to the unpredictability of generating revenue from one-off projects. The stability of MRR is part of what has attracted investors to the MSP sector. So, although the entrepreneur might be far from needing an exit strategy, it's good to know that one exists.
Opportunity for higher margins. Many companies that transitioned into the MSP business model were originally resellers. Those companies sought higher profitability in services as hardware margins eroded over the years. MSP business management software and various automated tools offer service providers the ability to support multiple customers with a relatively small number of employees, opening opportunities to boost profits.
Opportunity for expanded services. MSPs that successfully launch an initial service line are poised to provide additional offerings, from IT strategy consulting to backup and recovery. Those additional services help a provider avoid customer churn because clients can meet more of their needs through the MSP without having to turn to other suppliers. Add-on services also increase the amount of revenue generated per month, per customer.
Ability to tap mature technology. Early MSPs built their own tools or used commercially available, but non-MSP-specific, data center management software to run their operations. Today, MSPs have a wide range of purpose-built software products to manage their businesses. Remote monitoring and management (RMM) and professional services automation (PSA) products are among the offerings that can serve as an MSP's technology foundation.
Service provider startups interested in seizing those MSP advantages will encounter challenges along the way.
Developing the initial offer. An early task for the MSP is developing and pricing the offer. There are numerous pricing models -- see section below -- from which to choose.
Obtaining talent. MSPs face the same technology talent shortage as any other technology business. The problem becomes more acute as the MSP ventures into high-demand areas, such as cybersecurity and cloud engineering.
Marketing services. Most MSPs rely on with word-of-mouth promotion and customer referrals to get off the ground. At some point, however, MSPs tend to reach a plateau in which new sales just keep up with the natural rate of customer attrition. MSPs must develop a marketing plan to promote their value proposition, maintain a healthy sales pipeline and keep the company growing.
Gearing up for vertical markets. As MSPs expand, they might choose to focus on one or a handful of vertical markets. To pursue such a strategy, a service provider might need to acquire specialized industry knowledge or develop expertise in technologies endemic to particular industries.
Adjusting to changing market conditions. MSPs operate in a dynamic, rapidly changing market. Service providers must constantly refine their business plans to remain relevant. The arrival of cloud computing, for example, compelled many MSPs to reinvent their services. They must also adapt to macroeconomic patterns and unpredictable events, such as the COVID-19 pandemic. The latter has presented MSPs with several challenges, including the need to develop business strategies that take uncertainty into account. The pandemic's financial lessons favored service providers with broader portfolios that provide a mix of security, collaboration and cloud offerings.
How to Build an MSP Business Model
Entering the managed services market requires several steps. Here's a summary.
1. Define the business strategy
Where, what and how are the first questions to answer when devising the core MSP strategy. What geographical area or areas will the company pursue? What services will the MSP provide? How will the MSP deliver the services offered? MSP veteran Dave Sobel advised entrepreneurs starting a service to consider focusing on a line-of-business technology, which lets the MSP deliver business value with an offering specific to a vertical market. The MSP business strategy can extend to how the MSP plans to work with customers' internal IT teams. The co-managed IT services approach, for example, aims to create a cooperative relationship between the MSP and the IT department as opposed to an adversarial one.
2. Determine the pricing model
Pricing is an element of business strategy that deserves special attention. An MSP's pricing model provides the basis for recurring revenue. In addition, proper pricing will make it easier for customers to assess and consume a provider's offerings. An MSP can choose from at least six popular pricing models, which run the gamut from simple plans to all-encompassing packages. Which model works for an individual company will depend on the scope of the services it plans to sell and the intended customer base.
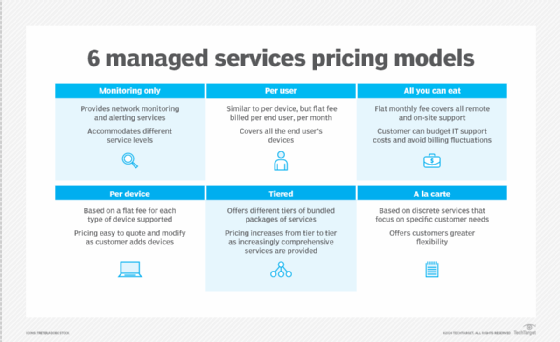
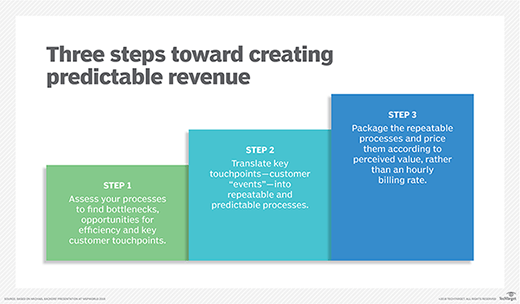
MSPs starting from scratch have a clearer path when adopting a pricing model. Companies transitioning to the MSP business model from a different approach will likely need to revamp their pricing to obtain a predictable revenue flow. Once a pricing approach has been established, MSPs must learn how to stay competitive without slashing prices. Techniques include paying close attention to labor costs and focusing on a vertical market or technical specialization that reinforces the company's value in the eyes of customers.
3. Create and offer an SLA
An MSP must offer a service-level agreement (SLA) to govern its relationships with clients. The SLA documents the services the MSP will provide, defines the standards for delivery and establishes the means for redressing issues. Service provides might also create a master service agreement, which sets forth the general terms and conditions for client work. The service agreement might incorporate the SLA by reference. SLAs help manage customer expectations and provide customers with a tool for comparing offers from different MSPs.
4. Create a sales and marketing strategy
Sales and marketing are often not the strongest parts of an MSP's business. Engineers and technicians often launch such companies, which initially gain new customers through referrals rather than active selling. MSPs built as lifestyle business might not need to grow past a certain point. But service providers that seek continued business expansion will probably need to create a proactive sales and marketing effort.
Creating an MSP sales process starts with finding an experienced MSP salesperson. People with that experience are difficult to find, so an MSP might need to hire salespeople and train them on the fundamentals of the technology and the MSP business. Another option is to have an MSP technician, in a sales engineering role, partner with a salesperson on customer calls. The sales process should be standardized, from the initial contact with a prospect to order processing.
A sales and marketing strategy rests on two essentials: knowledge of self and knowledge of customer. An MSP needs to know its strengths to craft a go-to-market message. Based on that insight, a service provider can also develop a profile of the ideal customer and then focus its sales and marketing activities in that direction. Consultative selling, which zeros in on a client's pain points, is another approach that MSPs can adopt when targeting SMB customers. MSP marketing considerations include making sure website copy speaks to targeted customers, building a brand around core services and appointing one person in-house to take on marketing duties.
5. Develop a recruiting strategy
An MSP that launches with a core group of employees will eventually need to recruit talent in order to serve customers as it grows. An IT recruitment strategy should ideally strike a balance between looking for required skill sets and looking for personality traits that fit the organization's culture. Technical expertise, while important, isn't the whole employee picture. Service providers seeking new employees should consider an applicant's ability to cope with pressure, learn as they go and adapt to unexpected situations.
6. Think about the type of MSP you want to become
A startup MSP might initially concentrate of basic services, such as network monitoring and management. But it's never too early to think about a growth trajectory. A service provider should assess customer needs to determine next steps, such as offering backup and disaster recovery or cybersecurity. Eventually, an MSP can choose to specialize in one or more areas. Here are some possibilities:
- Vertically focused MSP. Here, the MSP would acquire expertise in one or more verticals and go to market as an industry-specific service provider.
- Platform-oriented MSP. An MSP can choose to focus on a particular technology stack, public cloud infrastructure platform or SaaS offering.
- Consultative MSP. Early-stage service providers tend to focus on the technical aspects of supporting customers. Providing consulting services, however, puts MSPs in a position to address business concerns. MSPs can evolve to the point of offering a virtual CIO service.
- Managed security services provider. An MSSP offers a range of services to help customers address security, privacy and compliance issues. While MSSPs specialize in security, MSPs increasingly offer at least some security features.
- White-label service provider. An MSP, at some point in its development, might decide to offer its infrastructure to smaller MSPs. This MSP business model variation can provide a range of offerings, including network operations center services, staff augmentation and cybersecurity.
7. Embrace change
The IT services market is subject to constant change. Channel companies have continuously evolved over the years, from resellers to solution providers to MSPs to cloud-driven MSPs. A service provider can expect to transform its business model every few years and must tweak its service mix on an ongoing basis. Transformation can prove expensive and disruptive to employees, vendor partners and customers. MSPs will need to periodically evaluate the feasibility of launching new lines of business and explore how a new business model would affect its web of relationships.
Executing the MSP business model
The task for service providers shifts from planning to execution once the MSP business model is in place.
The client onboarding process is a key aspect of bringing a business model to life. The customer relationship depends on this early step. MSPs should document and standardize the process to make it consistent. Client onboarding typically involves several actions, including assessing the client's IT infrastructure and tools and identifying specialized requirements with respect to specific technologies or vertical markets. The process also aims to provide a smooth transition for the customer along the relationship continuum, from presales and sales to ongoing operations. MSP employees involved in the process can include an onboarding manager and customer advocates.
Realizing the benefits of the MSP model -- namely, the opportunities for recurring revenue and higher margins -- will depend on a service provider's operational efficiency. An MSP that fails to deliver quality services or struggles with keeping labor costs in check will have a hard time retaining customers or turning a profit.
Specialized software for managing and automating an MSP's operations plays a crucial role in sustaining the business. RMM software, the technology cornerstone for most MSPs, lets service providers remotely manage their customers' IT infrastructure. In addition to keeping tabs on a range of customer gear, from servers to mobile devices, RMM also manages patching and software updates. PSA software tools, meanwhile, automate an MSP's core business functions, playing a role like that of ERP in other types of businesses. PSA functionality varies from one software vendor to another, but typical functions include time and billing, project management, ticketing and reporting.
Although RMM and PSA serve as the technology underpinning for many MSPs, those products aren't the only approaches service providers employ. Other companies use a combination of network performance monitoring, IT service management and CRM products, for example.
Flexibility should be built into an MSP's operations, given the pace of technology change and the potential for unforeseen events. The COVID-19 pandemic, for instance, disrupted many types of businesses, but perhaps had less severe effects on the MSP model. Many industries, amid work-from-home directives, needed to develop remote workforce management strategies. MSPs, however, founded on the concept of remote management, have long maintained distributed workforces. Service providers might have expanded the population of remote workers and relied more heavily on collaboration tools, but rarely needed to devise an entirely new strategy for managing remote employees.
Other MSP trends managers should prepare to accommodate include the increasingly complex nature of managing multi-cloud environments, the evolution of cybersecurity needs and rising demand for automation.





