What is the risk-reward ratio?
The risk-reward ratio, also known as a risk-return ratio, is a mathematical calculation investors use to measure the expected gains of a given investment against the risk of loss.
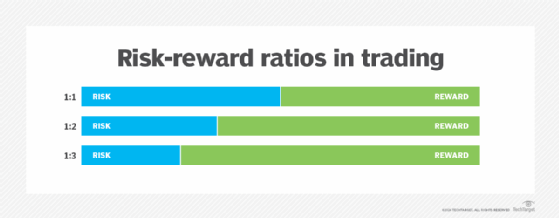
The risk-reward ratio is typically expressed as a figure for the assessed risk separated by a colon from the figure for the prospective reward. Usually, the ratio quantifies the relationship between the potential dollars lost should the investment or action fail versus the dollars realized if all goes as planned -- i.e., reward. For example, a risk-reward ratio of 1:3 would signify that for every $1 risked, there's a $3 potential profit or reward.
While the acceptable ratio can vary, trade advisers and other professionals often recommend a ratio between 1:2 and 1:3 to determine a worthy investment.
It's important to note that some traders use the ratio in reverse -- that is, depicting a reward-risk ratio. It similarly calculates the potential reward, or net profit, against the potential risk, or the amount that could be lost. This is presented as a mirror image of the risk-reward ratio: A reward-risk ratio of 3:1 indicates a $3 potential reward for every $1 risked.
Why is the risk-reward ratio important?
The risk-reward ratio helps investors and traders evaluate the potential return of an investment relative to the risk taken. The following key reasons show its significance:
- Informed decision-making. Investors use risk-reward ratios to help them determine which investments to make. Specifically, investors use the risk-reward ratio to determine the viability of a given investment. The risk-reward ratio can also help investors measure one potential investment against another, comparing the amount of risk they assume for each investment against each investment's expected returns.
- Profitability potential. A favorable risk-reward ratio can lead to profitability even if the win rate is low. For example, if a trader has a risk-reward ratio of 1:3, they can still be profitable by winning only 1 out of 4 trades, provided their average profit per trade exceeds their average loss.
- Strategic planning. By analyzing the risk-reward ratio, traders can develop strategies that align with their financial objectives. For instance, an investor seeking a 1:5 risk-reward ratio would adjust their successful trading strategy to achieve that balance, which can lead to more disciplined trading practices.
- Risk management. Understanding the risk-reward ratio is crucial for effective risk management. It enables traders to set appropriate stop-loss orders and take-profit levels, ensuring they can manage their exposure to losses while maximizing potential gains.
- Consistency. By focusing on risk-reward ratios, investors can maintain a disciplined approach to trading and investing, avoiding impulsive decisions based on emotions.
Who uses the risk-reward ratio?
The risk-reward ratio is most commonly used by stock traders, investors, foreign exchange (forex) traders, portfolio managers and others in financial services to evaluate financial investments such as stock purchases. They sometimes limit risk by issuing stop-loss orders, which trigger automatic sales of stock or other securities when they hit a specific value. Without such a mechanism in place, risk is potentially unlimited, which renders the risk-reward ratio incalculable.
The ratio is also used by project managers and others involved in project portfolio management (PPM). The risk-reward ratio is used in PPM to quantify the potential risks and benefits of a project. Project leaders use the ratio to assess the feasibility of the overall project as well as for assessing specific components of the project.
Project management leaders also use a risk-reward ratio to choose one investment over another. A project that has the same expected return as another project but has less risk is usually deemed the better choice.
Risk vs. reward
Nearly all investments come with some level of risk, as few, if any, can guarantee a return or reward. The same is true of projects, which require an investment of resources to complete a task or endeavor that offers a potential profit target or benefits upon completion.
In a risk-reward ratio, risk is the amount of money that could be lost in the investment. In a stock purchase, that amount is the actual capital value, or the actual dollar amount, that could be lost.
In a project scenario, risk represents the value of resources being put toward the project. The reward is the monetary value of the gains that could be reaped from completing the project.
Therefore, in a risk-reward tradeoff, investors should assess how much risk they're willing to take in exchange for potential rewards. This assessment often involves analyzing metrics such as volatility and beta, which help gauge the risk associated with specific investments.
How does the risk-reward ratio work?
As previously stated, the risk-reward ratio enables investors to evaluate the level of risk they must accept against the potential returns they could achieve. In this way, the risk-reward ratio gives investors a level of visibility into each investment's potential for loss against its potential for gains.
So, a risk-reward ratio of 1:1 indicates that the investor faces the possibility of losing the same amount of capital that they stand to gain through positive returns.
Each investor can set their threshold for acceptable risk. A more risk-tolerant investor might be willing to accept a ratio that indicates a higher risk for the same level of reward, while a risk-averse investor might consider a 1:3 ratio as high risk and not worth the investment.
Win rate and the risk-reward ratio
In the stock market, a win rate reflects how many of the total number of trades made during a prescribed period were profitable. For example, if you have 15 profitable trades out of a total of 20 trades a day, your daily win rate is 15 out of 20, or 75%. According to Investopedia, a win rate above 50% is usually considered good. A high win rate, however, doesn't necessarily indicate that you've made money, as the losses of the bad trades could exceed the profits from the winning trades. That is where the risk-reward ratio comes in: It calculates your trades' potential loss versus the potential profit.
How do you calculate risk and reward?
An investor can calculate a risk-reward ratio by dividing the amount they could profit, or the reward, by the amount they stand to lose, or the risk.
For example, if an investor bought a stock for $100 and plans to sell it when it hits $200, the net profit would be $100. If they're willing to risk the entire investment, then the value of their risk is $100. So, 100 divided by 100 is 100/100 or 1:1 -- meaning the risk and reward are equal.
Consider the same investment with a stop-loss at $50, but with the same expected profit of $100. In this case, the investor is willing to risk $50 to make double that. That's 50 for the risk and 100 for the reward, or 50/100, which is 0.5:1. However, risk is typically represented as 1 in the risk-reward ratio, so 0.5:1 is expressed as 1:2.
Examples of the risk-reward ratio in use
The following are real-world examples of risk-reward ratio scenarios:
- Real estate investment. An investor buys a property for $200,000, expecting to sell it for $300,000. They anticipate spending $20,000 on renovations. If the renovations don't add value, the investor risks losing that amount. The potential profit is $100,000, while the risk is $20,000, giving a risk-reward ratio of 5:1.
- Forex trading. In forex trading, a trader might enter a position with a risk of $100 and an expected profit of $300. This ratio suggests that the trader is willing to risk $1 to potentially earn $3, which is a common strategy among traders aiming for high returns.
- Cryptocurrency trading. A trader buys a unit of cryptocurrency at $100, setting a stop-loss at $90 -- a risk of $10 -- and a take-profit at $130 -- a reward of $30. This indicates a favorable scenario where the potential reward is three times the risk taken.
- Startups. An entrepreneur invests $100,000 into a startup, hoping it generates $1 million in returns. If the startup fails, they lose their entire investment. The potential reward is $900,000, while the risk is $100,000, resulting in a risk-reward ratio of 9:1.
The risk-reward ratio doesn't consider other factors that affect investment decisions and trade ideas. Most notably, the ratio doesn't consider the probability of an investment paying off. Take, for example, a $1,000 investment that could return a $1,000 gain, but the chances of that investment successfully delivering any returns are very low -- perhaps there's only a 10% chance. The risk-reward ratio at 1:1 might indicate a low risk, but the risk is much higher when considering the probability.
Similarly, some projects might have a lower ratio or probability of failing, but are coupled with a low potential return on investment. Projects with more unknown factors might have a higher probability of failure, but at the same time offer a significantly higher return if they're successful. Companies typically distribute their risk by investing in projects that fit into both categories. The ideal is a project with a lower risk-reward ratio -- little risk of failure and high potential for reward. However, that type of project tends to be rare.
Benefits and limitations of using a risk-reward ratio
The risk-reward ratio helps investors and project leaders with risk management by doing the following:
- Manages their risks by giving them a tool to evaluate and express the potential risk.
- Evaluates risks and rewards in an objective manner, as the risk-reward ratio -- a mathematical calculation -- removes subjective elements from the evaluation.
- Quickly recalculates risks against rewards if dynamics -- and values -- change.
The following are some drawbacks of the risk-reward calculation:
- It doesn't consider probability.
- It can oversimplify complex trading situations, as it overlooks important factors such as market conditions, volatility and the trader's experience.
- The ratio depends on the quality of the investor's research and ability to gauge risk.
- The risk-reward ratio doesn't incorporate other potential factors and calculations, including, for example, the possibility that the stock price doesn't fluctuate.
- In highly volatile markets, the risk-reward ratio can become less reliable. Rapid price movements can lead to slippage, affecting the actual risk and reward realized in a trade.
So, while the risk-reward ratio can help calculate and compare investment risks, the figure in and of itself isn't considered adequate for determining worthwhile investments.
Explore common types of business risks companies face, from strategic and operational to cybersecurity and reputational risks. Understand these risks for good risk management and organizational success.