round robin
What is round robin?
A round robin is an arrangement of choosing all elements in a group equally in some rational order, usually from the top to the bottom of a list and then starting again at the top of the list and so on.
A simple way to think of round robin is that it is about "taking turns."
Round robin applications
While this definition is general, there are some specific applications for a round robin. We examine a few of these below.
Computer operations
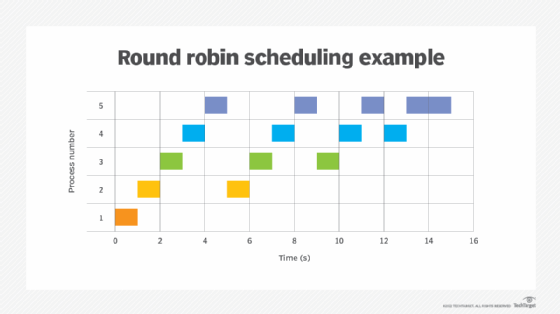
In computer operations, round robin is used in a scheduling algorithm that distributes work evenly among all available resources. This ensures that no single resource is overworked, which can lead to errors and other issues down the line.
This is often described as round robin process scheduling.
Another example of round robin in computer operations is round robin DNS (or RRDNS), a method that allows multiple DNS records to be created for the same IP address.
This ensures that no matter how many users are accessing the same domain name, each user has equal access to information and services through round robin.
Sports
In sports teams like those found in the NFL, NBA, MLB or NHL, a round robin is a method of scheduling where each participant plays against all other participants in the event. This is also referred to as a round robin tournament.
This is commonly used in tennis tournaments, where round robin play determines who advances to the next round and who ends up being eliminated.
Gambling
In gambling and sports betting, a round robin is used as a betting strategy. This means that instead of betting on one game or event, the bettors take stakes on multiple games or events. This is also referred to as parlay betting.
A round robin bet can be done in different ways with many possible combinations, but the most common is to make round robin wagers on each game or event in a group.
For example, during sports playoffs, a round robin parlay may occur for multiple teams playing. If one team loses, the bettor still has a chance to win with the other teams.
The advantage of this is that it increases the betting odds of winning because there are more possible outcomes and more potential payouts.
Stories
A round robin story is one that is started by one person and then continued successively by others in turn.
Whether an author can get additional turns, how many lines each person can contribute, and how the story can be ended depend on the rules.
Some websites have been created for the telling of round robin stories by each person posting the next part of the story as part of an online conference thread.
Business meetings and events
When planning business meetings and events, round robin scheduling can be used to have all attendees take turns presenting their ideas or products.
This ensures that all attendees have an equal opportunity to share their views and be heard, while also minimizing time wasted in the back-and-forth between speakers.
Overall, round robin arrangements allow for a fair and balanced distribution of tasks, resources, or other opportunities among different individuals or groups within a business context.
See also: machine learning algorithm, sorting algorithm, consensus algorithm, job scheduler
