What is a script?
In computer programming, a script is a program or sequence of instructions that another program interprets or carries rather than the computer processor doing it (as with a compiled program).
Scripting is an essential concept in modern programming because scripts allow users to automate many computing processes that would otherwise be time-consuming when performed manually by humans. Automation saves time and helps accelerate the software development lifecycle (SDLC). Scripting-led automations also minimize the potential for errors, resulting in higher-quality software output.
What is a script in programming?
A script is a mini program that contains a specific set of instructions for a precise purpose. A programmer needs to code it using programming language syntax and rules. In this sense, scripting is a type of coding. In addition to providing instructions to a computer, scripts are used to automate tasks so programmers and users can focus on tasks that cannot be automated.
Scripts can be created for a variety of tasks, both simple and complex, including:
- Displaying the current date and/or time;
- Displaying personalized greetings to a user;
- Entering repetitive data strings;
- Building interactive web pages;
- Developing games;
- Developing mobile apps;
- Manipulating large data sets;
- Building and training machine learning models;
- Automating IoT devices;
- Automating operating system tasks;
- Testing and debugging software programs; and
- Developing server-side software.
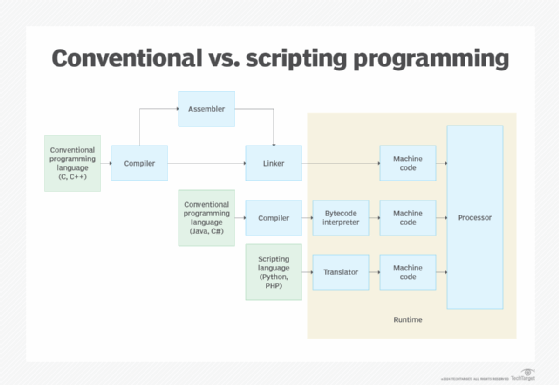
In all languages, scripts are executed in a runtime environment. Also, most scripts do not have to be compiled before they are run. Instead, the language interpreter translates them line-by-line from the source code (or byte code) and executes them in real time. Unlike scripts, programs are compiled before execution and then delivered to the client (computer or browser) in compiled form.
Another common feature of scripts is that they are short and fast. This facilitates quick interpretation and execution so the desired action can be performed swiftly to produce the desired output.
What does a script look like?
Scripts look different in depending on the programming language and purpose. The script's look and feel as well as features depend on the scripting language syntax and structure.
For example, a script in Python could include the following features:
- The file extension .py;
- Comment blocks that describe the script's purpose, placed within open and closed apostrophes or quotation marks;
- Define functions;
- Import functions from another module; and
- Import variables or classes defined in another script.
Here's what a script named current_time.py may look like in Python:
“””
This script will show the current time in Los Angeles.
“””
# import the required modules
import datetime
def gettime() :
“””
This function returns the current time.
“””
now = datetime.datetime.now()
return now.hour, now.minute, now.second + 1e-6 * now.microsecond
print(f"The current time in Los Angeles is {hour}:{minute}:{seconds}")
This script can be run in a terminal using a simple 1-line code:
python current_time.pyA script in Ruby may use either puts or print methods. So, to create a script that outputs "TechTarget is the best!" the Ruby script may be:
=begin
This is a Ruby program to print TechTarget is the best!
=end
puts " TechTarget is the best!"
print " TechTarget is the best!"
puts " TechTarget is the best!"Benefits of scripts
Numerous scripting languages are available to create scripts. These scripts can automate numerous repetitive tasks, thus minimizing the human effort needed to execute those tasks. With scripts, developers can save hours of manual labor and increase their productivity by focusing on other higher-value tasks.
The small size, simple syntax and compact nature of scripts make them easy to learn and write. They are also easier to work with than full-fledged programs because they are often written in scripting languages. These languages are easier to learn than programming languages, so they are more accessible, even for beginner-level users.
Because scripts contain specific instructions, they always execute in the same way and produce consistent, error-free output. This makes them suitable for many types of tasks, which may run on a server or a client device.
One drawback of scripts is that they can take longer to run than a compiled program. Another program handles each script instruction first (requiring additional instructions) instead of the basic instruction processor handling them directly.
Programming languages designed for scripting
Some languages have been conceived expressly as script languages. Among the most popular are Perl, Rexx (on IBM mainframes), JavaScript and Tcl/Tk. In the context of the World Wide Web, Perl, VBScript and similar script languages are often used to write scripts that handle forms input or other services for a website and are processed on the web server. A JavaScript script in a web page runs "client-side" on the web browser.
Other popular scripting languages include:
- Python
- PHP
- Ruby
- CSS
- Visual Basic
- R
- Bash
Some of these languages are general purpose, meaning they can be used to create scripts for a variety of tasks across different application domains. Examples of these language types include Python, PHP, Ruby and JavaScript. Domain-specific languages (DSLs) are used to create scripts for specific applications in specific domains such as web design, numerical computation and behavioral testing. DSL examples include CSS, MATLAB and Gherkin.
Scripting languages may be client-side or server-side languages. Server-side languages run off a web server, while client-side languages run off a client device or browser. Python and PHP are server-side scripting languages, whereas CSS and JavaScript are client-side languages.
Some languages are not strictly scripting languages but do support script creation. For example, Go (Golang), an open source programming language used to build scalable applications, can also be used to write clean, readable, easily maintainable scripts.
In general, script languages are easier and faster to code than the more structured and compiled languages such as C and C++. That said, it's important to choose a scripting language that applies to the task that's being automated. For example, Ruby may be a better choice for creating a script to automate some DevOps tasks, while Perl may be more suitable for extracting data from log files. Similarly, Python is a good language for writing scripts for back-end web development, while JavaScript is great for client-side scripting.
What is a script in other scenarios?
Apart from programming, the word "script" is commonly used in many other scenarios.
For example, it can mean a list of stored OS commands the operating system's command interpreter performs sequentially whenever the list name is entered as a single command.
Multimedia development programs also use the term. In this context, "script" means the instruction sequence a user enters to indicate how a multimedia sequence of files will be presented (the sequence of images and sounds, their timing and the possible results of user interaction).
Choosing a programming language is often dictated by the problem the programmer wants to solve and the compute goal that a language is designed to achieve. Explore the differences between scripting and programming languages.
