SEO poisoning (search poisoning)
What is SEO poisoning (search poisoning)?
SEO poisoning, also known as search poisoning, is a type of malicious advertising (malvertising) in which cybercriminals create malicious websites and then use search engine optimization (SEO) techniques to cause the sites' links to show up prominently in search results, often as ads at the top. Because of their prominence in the results, users often assume that the links connect to websites that are legitimate and safe.
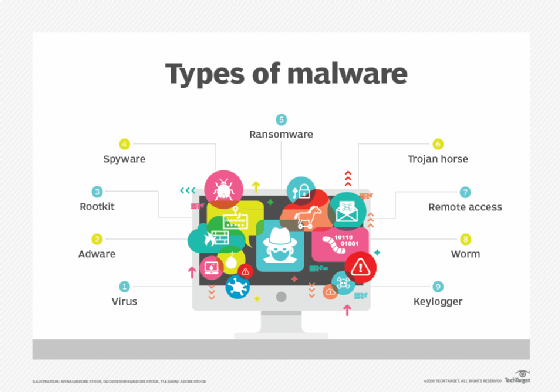
One of the main reasons that threat actors use SEO poisoning is to get site visitors to inadvertently download malware onto their systems. For example, users might click a link to a malicious website that looks like a webpage for downloading a familiar app. When they go to the site, they're prompted to download a malicious file, thinking it's the application they're after. Once the malware is installed on their systems, it might record keystrokes, take over their computers or spread to other devices on the network, leaving a company vulnerable to ransomware, compromised data or other threats.
Threat actors might also use SEO poisoning to get users to reveal sensitive information, such as credit card numbers, login credentials or personally identifiable information (PII). A user might, for example, click a link to what appears to be an online store, intending to make a purchase. The link instead takes the user to a malicious website that looks nearly identical to the real store or at least looks credible enough to appear trustworthy. There the user is prompted for a name, address and credit card number, information that is quickly sold to the highest bidder.
Not all malicious websites try to duplicate credible sites. They might be created only to host content filled with terms that large numbers of people are likely to include in their searches, such as phrases related to news items or viral videos.
Threat actors might also create websites with names and descriptions associated with popular or trending topics. For example, in the weeks leading up to Halloween, cybercriminals might launch sites offering free templates for Halloween costumes. Or in the month before Christmas, they might launch holiday recipe sites. The websites might be devoid of relevant content or might feature content stolen from valid sites. Their only purpose is to infect visitors with malware or fraudulently access sensitive information.
An example of SEO poisoning is when the SolarMarker malware was being distributed as malicious PDF files through fake SEO-focused topics in Google Groups. Discovered in late 2020, the malware would be embedded in a site that would appear near the top of Google search results due to the threat actors' SEO poisoning. It aimed to get victims to click a link to download a fake Windows installer running a PowerShell script.

The rising tide of SEO poisoning
In January 2023, cybersecurity firm SentinelOne published a blog post by Tom Hegel, warning of an increase in SEO poisoning attacks. The company found that, in most attacks, the threat actors were trying to infect user systems with commodity malware. According to the post, the criminals were most successful when they used SEO poisoning to impact the search results for "popular downloads associated with organizations that do not have extensive internal brand protection resources."
To illustrate this concept, Hegel pointed to the ongoing SEO poisoning campaign associated with the Blender 3D graphics app. He included several examples of rogue ads at the top of the Google search results that linked to malicious websites. Hegel also noted that the malicious ads quickly shifted between searches, suggesting that the cybercriminals were automating their attacks at scale. The automation appeared to apply to both the SEO poisoning itself as well as to the malicious domains being created.
In February 2023, Cybereason published an alert about the GootLoader malware. The alert outlined how SEO poisoning was being used to spread the malware through fraudulent websites. GootLoader typically relies on JavaScript to infect the systems of unsuspecting users who were directed to the malicious sites through search engine ad links. Such ads might also be used to link users directly to the infected malware.
In April 2023, BlackBerry published its "Global Threat Intelligence Report," which covered the period from December 2022 through February 2023. According to the report, SEO poisoning increased during the reporting period, especially in the healthcare industry. The report also concluded that SEO poisoning is becoming more widespread and is expected to grow.
In June 2023, the Health Sector Cybersecurity Coordination Center (HC3) of the U.S. Department of Health and Human Services (HHS) published an analyst note that warned about the rising use of SEO poisoning against the healthcare and public health sector. According to the report, cybercriminals carry out their attacks by leveraging hacker SEO techniques, which are unethical tactics used by website owners to boost their search engine rankings. For example, they might use tactics such as cloaking, keyword stuffing, search ranking manipulation or private link networks to boost their search engine ranks.
The HHS analyst note also warns that hacker SEO techniques are being used along with typosquatting, another method for misdirecting users to malicious websites. Threat actors use typosquatting to target those who misspell URLs when entering them into their browsers. The threat actors set up domains with names that match the misspellings and then wait for users to come to their sites. When typosquatting is combined with SEO poisoning, however, links to the malicious websites often appear near the top of the search results, making it more likely that users will click them because the addresses are so close to the real thing.
Security experts offer several recommendations to users who want to protect themselves against SEO poisoning attacks. Users should keep their browsers and antivirus software up to date, avoid clicking suspicious-looking links, and never provide personal information online unless they're certain the site is valid and the transaction is secure.
Learn more about search engine poisoning and how poisoned results are detected.
