service chaining
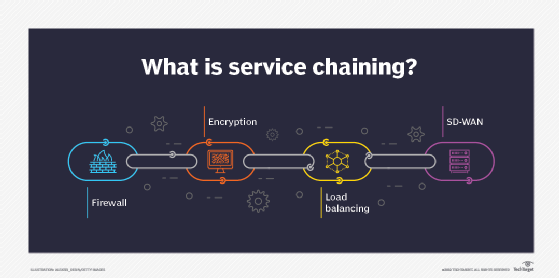
Service chaining, in an information technology (IT) context, is the addition of software-defined networking (SDN) capabilities in a specific sequence. Service chaining helps to automate traffic flow between services in a virtual network. It also optimizes the use of network resources to improve application performance by using the best available routing path. Common use cases for service chaining include network functions virtualization (NFV) deployments, data centers, carrier networks and virtual customer premises equipment (VCPE). Types of network services that can be included within the chain include firewalls, network address translation (NAT), WAN optimization, intrusion protection and load balancing. In this context, service chaining can also be referred to as service function chaining.
How service chaining works
A service chain is made up of the following elements:
- A service template- This lays the foundation of code that will be used in the service chain.
- A virtual network- This serves as an abstract connection between physical points within a network.
- A service instance- This is the actual implementation of a service within a node.
- A service policy- This is the set of rules dictating how data traffic moves between a virtual network and specific service instances.
Once the chain is set up, network operators can create subsets of connected services to allow the use of one network connection for various applications.There is no limit to the number of services that can be connected between virtual machines in this way. An SDN controller or script can use the chain in different ways depending on the source, destination or traffic type. This way, a packet only receives services that are required. For example, packet A may be forwarded through services 2, 3 and 4 while packet B is forwarded through 1 and 4. Additionally, since service chaining is done in software using virtual circuits, services can be inserted and removed as needed.
