Lean software development
What is Lean software development?
Lean software development is a concept that emphasizes optimizing efficiency and minimizing waste in the software development process. This approach has its roots in the Lean manufacturing movement of the 1980s. However, it is now considered an integral part of the Agile software development methodology.
Lean thinking can also be applied in other disciplines. Lean management is one example of this.
What are the 7 principles of Lean software development?
The main concept behind the Lean development methodology is that efficiencies can be applied, and waste can be managed at all levels of the process. These include at the individual level, as well as in departments, in interdepartmental operations, in the overall organization, and between the organization and its customers and suppliers.
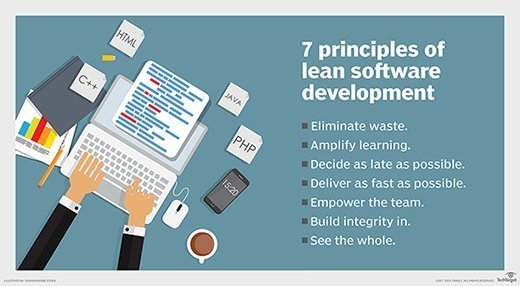
The Lean software development process includes the following seven principles:
- Eliminate waste. After each development iteration, project managers discuss bottlenecks, identify waste and develop a plan to eliminate it. The Lean philosophy has a broad definition of waste that includes anything that doesn't add value to the product. Some examples are the following:
- unnecessary code or software features;
- more tasks than can be completed in the task log;
- bureaucratic processes; and
- quality issues.
- Build in quality. Various tactics are used to ensure quality is built into the Lean process, such as pair programming and test-driven development.
- Amplify learning. Knowledge one software engineer gains must be shared with every engineer on the software development team. This occurs through code review and sharing at meetings. Also, engineers learn as they go and question assumptions.
- Delay commitment as long as possible. The goal is to experiment and learn as much as possible before committing to irreversible decisions. Developers incorporate features and functionality as late as possible in the process to prevent having to redo work as the market changes.
- Deliver fast. Developers launch a product quickly, receive customer feedback fast and use that feedback to create a strategy for improvement. The idea behind this approach is to fail fast and learn from the results. This strategy contrasts with other methodologies used to design complex products. They often take a lot of time and still end up failing.
- Respect people. Respect is the basis for a productive, collaborative atmosphere. Lean encourages healthy conflict, proactive communication and constant feedback.
- Optimize the whole. The team examines the process from start to finish to make the Lean value stream as efficient as possible. It contrasts with the concept of suboptimization, where subpar code is generated faster than it can be tested for the sake of speed and software testers are overloaded.
What is the difference between Lean development and Agile?
Lean and Agile principles have much in common. When comparing Lean and Agile, experts often point to the similarities rather than the differences. Lean and Agile work together so seamlessly that it's difficult to tell them apart. They are sometimes referred to in tandem as Lean-Agile.
The last three Lean principles highlight some of what the Lean methodology has in common with Agile. In both cases, the product development team sets the pace and is responsible for delivering the product. Agile teams do this using the sprint methodology. And Lean's "optimizing the whole" principle is similar to the Agile retrospective, where team members gather after a project's completion to discuss successes and challenges.
There are some subtle differences between the two processes. Lean focuses on building better processes, while Agile's focus is to build better products. Agile practices seek to create products that meet consumer needs and expectations, and Lean is one way to achieve that goal.
Lean is often counted as one of several Agile frameworks -- Scrum and Kanban are two others. The Agile methodology is detailed in the Agile Manifesto, which contains a set of values and principles that guide the Agile frameworks.
What are the benefits of Lean software development?
Some of the advantages of Lean are the following:
- Collaboration. Lean principles amplify learning and respect to encourage collaboration and knowledge sharing and avoid bottlenecks. Teams are empowered to make their own decisions and work together in the decision-making process.
- Continuous improvement. Lean includes what many call the modern software development process. The workflow incorporates constant communication with customers and steady feedback. This enables continuous improvement, or Kaizen, in all parts of the operation.
- Efficiency. Demand for software is exploding, and companies cannot deliver apps fast enough. The Lean approach eliminates waste and delivers software fast, making development organizations more efficient and cutting cost.
- Flexibility. The Lean methodology incorporates flexibility, while still prioritizing speed in the software development lifecycle. It leaves room for change and lets developers alter products based on continuous feedback.
- Quality. Lean's efficiency, continuous improvement, flexibility and collaboration results in an overall improvement in product quality and an increase in customer satisfaction.
What are the challenges of Lean development?
These are some of the challenges of Lean software development practices:
- Team training requirements. If a team is unable to work together and communicate, development efforts suffer. Teams and team members must be trained so they can take on each other's work and adapt to changing initiatives. They must also be able to organize work and trade duties as priorities change.
- Missing metrics. A common pitfall of Lean is measuring the wrong software metrics or not measuring at all. Since one of the main goals of Lean software engineering is to eliminate waste, teams must be able to identify waste and measure it.
- No boundaries. Software requirements specifications evolve in Lean as customers provide feedback. Too many requirements and too much change create complexity and make it difficult to release a cohesive piece of software.
- Suboptimization. Suboptimization is when only part of the production system's value stream is optimized. This happens when a problem is broken into parts that are solved in isolation without considering the effect one part will have on other parts or the entire system.
The history of Lean development
The Lean manufacturing concept emerged in the mid-20th century out of a production process Toyota developed as part of its Toyota Way philosophy. Lean manufacturing aimed to reduce product defects, cut out waste, increase productivity, and encourage accountability and innovation. The approach eventually spread to other industries.
Mary and Tom Poppendieck used the term Lean software development in the book they published by the same name in 2003. It applied the seven Lean principles to software engineering and the development process.
Learn about the secrets to succeeding with Lean software testing.







