smart TV
What is smart TV?
A smart TV is a television that includes an internal processor and onboard storage and enables internet connectivity, similar to a smartphone or personal computer. The TV uses either an Ethernet or Wi-Fi connection to connect to the internet. Some TVs support both. A smart TV also hosts individual apps that can stream audio and video content, making it possible to support a wide range of services. It also supports the use of peripheral devices for interacting with the TV and apps.
Like a traditional or dumb TV, a smart TV can display content from cable or satellite signals, as well as receive over-the-air transmissions. Unlike a dumb TV, however, a smart TV also comes with a preloaded operating system (OS) and provides a graphical user interface (GUI) for interacting with the environment and working with the apps.
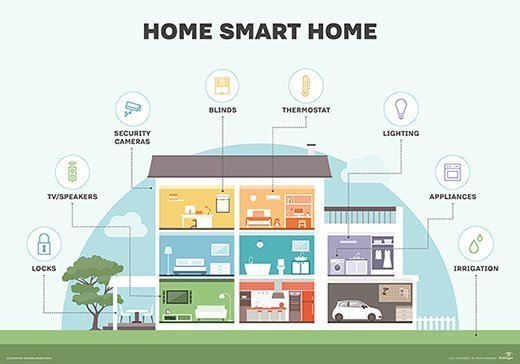
Smart TVs are an example of smart home technology, where internet-connected devices and appliances can be seamlessly integrated into a holistic system to enable automation, improve security, enhance entertainment and more in the daily lives of residents.
How do smart TVs work?
Manufacturers use a variety of OSes for their smart TVs. For example, Sony uses Google TV, Samsung relies on Tizen Smart TV, LG TVs come with webOS, and Vizio uses Vizio SmartCast. Some manufacturers offer a choice of platforms, such as Hisense, whose TVs can come with Android TV, Fire TV, Google TV, Roku TV, VIDAA or Xumo TV.
In addition to Ethernet and Wi-Fi, a smart TV supports other types of connections that enable viewers to access and control features related to streaming content from the internet and connected devices. For example, smart TVs often provide Bluetooth for connecting wireless devices such as keyboards, mice or headsets, as well as USB ports for attaching peripheral devices such as external thumb drives. In addition, the TVs include HDMI ports and other audio-video connections, just like traditional TVs, although a smart TV often includes more of them.
Most of a viewer's interaction with a smart TV is through the apps, which are either preinstalled on the system or can be downloaded from an app store. Viewers have a wide range of apps from which to choose, although not all apps are available to all OS platforms. In addition, the apps might work differently from one platform to the next.
Viewers can use these apps to stream videos, listen to music, play games, watch live newscasts, or browse the internet. For example, apps are available from services such as Netflix, HBO Max, Hulu, ESPN, CNN, YouTube, Zillow, Grubhub and a wide range of others. Although any supported app can be downloaded for free, many require a paid subscription to use the streaming services.

Viewers can also access pictures, music or videos through connected storage devices. In addition, they can mirror content from their smartphones and tablets. Some smart TVs also include built-in microphones and cameras to enable further interaction with the TV, and many of them support voice control capabilities that let viewers issue voice commands. Some TVs might even provide integration with smart home platforms such as Apple Home or Google Home.
Although smart TVs, like other smart devices, offer more intelligent functionality than traditional TVs, there is some concern that smart TVs pose a threat to personal privacy and security. At the 2013 Black Hat convention, for example, security researcher SeungJin "Beist" Lee showed attendees how cameras and microphones on smart TVs can be turned into state-of-the-art snooping devices by malicious hackers.
Even if a TV does not include a camera or microphone, a viewer's usage can still be tracked and personal information stolen. In 2019, the FBI issued a warning about the risks associated with smart TVs. Because they can connect to the internet, the TVs can make it possible for manufacturers, streaming services, and even hackers to access the viewer's personal information.
See how hackers use subtitle files to control endpoint devices, including smart TVs.
