soap opera effect (motion interpolation)
What is the soap opera effect?
The soap opera effect is the colloquial name for a visual effect caused by motion interpolation on television sets that some people find undesirable. Motion interpolation is a process done by high refresh displays where generated frames are inserted between the original frames of a video.
Motion interpolation was added to modern LCD televisions to reduce motion blur and make the picture appear smoother and sharper. It is needed because televisions update the image on the screen more times per second than the source video can provide. When the screen wants to put up a new image, but one isn't available, motion interpolation can use the previous frame and the next frame and calculate a guess in between frames to display.
Motion interpolation can go by many different names and trademarks, such as the following:
- Frame interpolation
- Video interpolation
- Motion smoothing
- Motion plus
- Smooth motion
- Enhanced motion
- TruMotion (LG)
- Auto Motion Plus (Samsung)
- Motionflow (Sony)
As an example of motion interpolation, a modern high-refresh television will update 120 times per second, or120 hertz (Hz). Most high definition videos will only go up to 60 frames per second (FPS). So, half the time the TV has no new frame to display. Without motion interpolation, the TV would show the same frame twice. With motion interpolation it can instead show a generated frame.
Motion interpolation takes advantage of the high refresh rate. With it the image appears smoother as there are more frames. The picture also appears sharper. Motion interpolation works best with fast smooth videos, such as sports.
The soap opera effect is an undesirable side-effect of motion interpolation experienced by some. From years of watching movies and television filmed at lower frame rates, our eye expects a certain amount of motion blur and time between frames. The addition of interpolated frames can remove this. This can cause the image to appear to be too sharp, too smooth or unnatural looking to some viewers.
The soap opera effect becomes more pronounced the lower the FPS of the original image. Old broadcast television was filmed at 30 FPS and movies for cinema are filmed at 24 FPS. When using these as a source and generating frames to bring it up to 120 Hz, users may wind up with more interpolated frames than original ones.
Because people are now watching more movies at home instead of at theaters, and because the soap opera effect alters how a movie may be perceived by the public, many movie directors have started speaking out against motion interpolation. Some TVs have a Filmmaker Mode to disable motion interpolation and preserve the director's original intent. It is possible that some TVs may be able to automatically detect when a movie is being played and then switch to Filmmaker Mode.
Why is it called the soap opera effect?
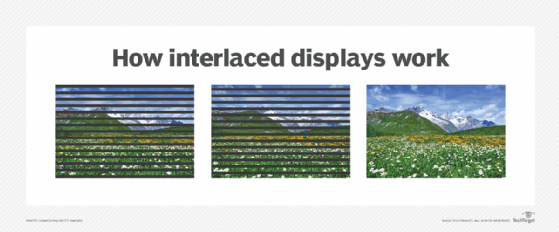
The term soap opera effect comes from cheaply made drama television shows, called soap operas. The term soap opera itself refers to the type of show designed to advertise products to American women during the day, or as some television executives put it, to "sell soap to housewives." As these shows did not have much money and needed to be made quickly, they would be filmed and edited on video tape (VHS), all of which happened at 30 FPS (60 interlaced frames). Big budget Hollywood movies on the other hand would be recorded, edited and shown in theaters on much more expensive chemical film stock at 24 FPS. Higher budget television shows would also use film as the original recording medium.
Even viewed on television sets, the difference between something originally recorded on film and on video tape was noticeable to some. So, the derogatory term soap opera effect was used to refer to a cheaply made movie or show that was originally recorded on VHS instead of on film.
Today, almost all movies and TV shows are recorded or edited digitally, so the distinction on what type of media was used to record it is mostly academic. But since the visual effect of high FPS video and motion interpolation is the same as seen between film and VHS, the term soap opera effect is still used.
How to remove the soap opera effect (disable motion interpolation)
The soap opera effect can be removed by disabling motion interpolation. The exact details and name may vary by manufacturer. In general, it can be accessed via the TV's on-screen display menu under picture or image settings.
Picture modes may also change motion interpolation. It will often be turned on for Sports mode but turned off for Cinema mode.
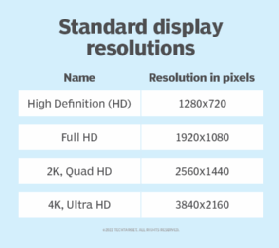
See also: interlaced scan, non-interlaced display, raster graphics, raster image processor, Quad HD, 4K, HDTV, UHDTV and SDTV.
