stack pointer
What is stack pointer?
A stack pointer is a small register that stores the memory address of the last data element added to the stack or, in some cases, the first available address in the stack. A stack is a specialized buffer that is used by a program's functions to store data such as parameters, local variables and other function-related information. The stack pointer -- also referred to as the extended stack pointer (ESP) -- ensures that the program always adds data to the right location in the stack.
The stack stores data from the top down, following a last in, first out (LIFO) data structure. This means that the program adds data to the top of the stack and removes data from the top of the stack. In this way, the top of the stack always contains the most recently stored data that has not yet been removed.
A program uses push operations to add data to the stack and pop operations to remove data from the stack. Because the stack is a LIFO data structure, the operations work similar to a pile of dinner plates at a buffet line. A plate can be added only to the top of the stack and removed only from the top of the stack. In the same way, data can only be added to or removed from the top of the stack.
As a program runs, calling one function after another, it continuously pushes data onto the stack and pops data off the stack. As a result, the address stored in the stack pointer register is constantly changing. When a new data element is pushed onto the top of a stack, the stack pointer is updated to the next physical memory address on the stack. When a data element is popped from the top of a stack, the stack pointer is again updated to the next address, but this time the address changes in the opposite direction.
The way in which memory addressing works in a stack can seem counterintuitive. The addresses decrease as they move toward the top of the stack and increase as they move toward the bottom, so when a data element is pushed onto the stack, the stack pointer decrements to the next address below the current one, and when an element is removed, the pointer increments to the address of the next saved element on the stack, which has an address higher than the current one.
How does the stack pointer work?
There is no one layout design that all stacks follow. A stack's design will depend on the programming language and the processor architecture, although different systems tend to follow similar patterns. In most cases, when a function call is made within a program, a stack frame is created on the stack to support that function's data. Each function generates its own stack frame, regardless of the function hierarchy within the program. The stack frame provides a logical structure for storing the function's parameters, local variables and other related data.
The following diagram shows a conceptual overview of how many stack frames are designed. The top of the stack contains data from the current stack frame, which is associated with the most recently called function. Beneath the current stack frame is a second stack frame, which is the function that called the current function. It was the last active stack frame before it made the function call.
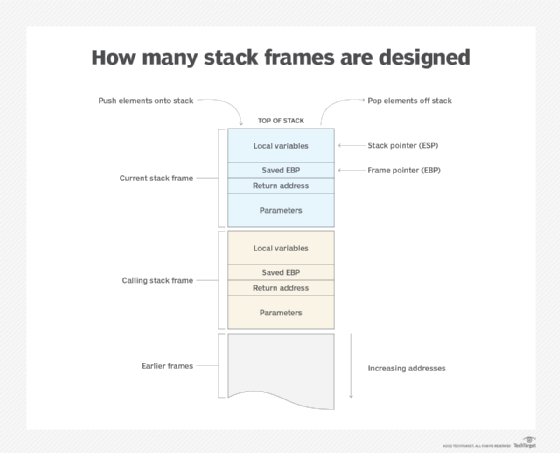
Parameters are the first data elements added to the stack frame, followed by the return address, which tells the program where to return after the function exits. The return address is then followed by an extended base pointer (EBP) address, which is saved to the stack frame for reference purposes.
The EBP, also known as the frame pointer, is a small register that points to a fixed location within the current stack frame. The frame pointer offers a reliable reference point for accessing elements in the stack, unlike the stack pointer, which can reference different memory addresses. When a function is called and the stack frame created, the program saves the existing EDP to the stack to provide a reference back to the calling stack frame.
After adding the saved EDP, the program pushes the local variables onto the stack, sometimes along with other types of data. The exact approach depends on the specific stack design.
No matter what type of function data is being stored, the stack pointer will always provide the program with the information it needs to locate the top of the stack. The ESP register might point to the address of the last added data element (that has not been removed) or to the address of the first available memory slot. It will depend on the compute environment and how function calls are carried out. Regardless of the approach, the stack pointer is always located at the top of the stack, providing a reliable starting point for accessing stack memory.
See also: accumulator, integrated circuit, buffer overflow, garbage collection, first-in, first-out, full-stack developer
