surge suppressor (surge protector)
What is a surge suppressor (surge protector)?
A surge suppressor, sometimes optimistically called a surge protector, is a device inserted in the alternating current (AC) utility line and/or telephone line to prevent damage to electronic equipment from voltage spikes, or transients.
A more accurate term for this type of device is transient suppressor. A typical surge suppressor is a small box with several utility outlets, a power switch and a three-wire cord for plugging into a wall outlet.
In most countries where the effective AC utility voltage for electronic equipment is 110 to 120 volts, the peak voltage is on the order of plus or minus 160 to 170 V at a frequency of 60 hertz (Hz). But transients, which arise from various causes, commonly reach peak levels of several hundred volts.
These pulses are of short duration, measured in microseconds -- units of 10-6 seconds -- but they can cause hardware to malfunction in that time. The worst type of transient occurs when lightning strikes in the vicinity and it does not need to strike a power line directly. Such a spike can peak at thousands of volts and cause permanent damage to equipment.

What is a surge in a conductor?
A surge suppressor prevents the peak AC voltage from going above a certain threshold, such as plus or minus 200 V. Conductor and semiconductor devices are used for this purpose. The power line is effectively short-circuited to the electrical ground for transient pulses exceeding the threshold, while the flow of standard 60 Hz current is unaffected.
For the suppressor to work, a three-wire AC power connection is needed. Cheater adapters, which enable three-wire appliances to be used with two-wire outlets or extension cords, defeat the purpose of having an electrical ground connection and render most surge suppressors ineffective.
Surge suppressors should be used as a matter of habit with all semiconductor-based electronic and computer hardware, including peripherals such as printers, monitors, external disk drives and modems. But the suppressor should not be relied upon to protect against lightning-induced transients.
The safest procedure, inconvenient though it may be, is to ensure that susceptible hardware is plugged into the suppressor box and to unplug the suppressor's main power cord when the equipment is not in use if you live in a thunderstorm-prone area.
What is a surge suppressor power strip?
A surge suppressor power strip is a type of power strip designed to withstand a power surge. Electronic devices plugged into a surge suppressor power strip remain safe during significant power fluctuations.
What is a surge suppressor outlet?
Like a surge protector power strip, a surge suppressor outlet can protect a connected device from a power surge.
What is a surge protector joule rating?
A surge protector joule rating describes how much energy it dissipates. The joule rating refers not only to how much energy a device can withstand, but also how much energy it can absorb.
For example, a surge protector rated at 1,000 joules lasts twice as long as one rated at 500 J. As such, a surge protector rating above 1,000 J provides better protection against surges.
What joule rating is preferred for a surge suppressor?
Getting a surge protector with a rating of at least 200 to 400 J is preferred for basic surge protection. Those in need of better surge protection should consider a surge suppressor with a rating of 600 J or more.
What is a good surge suppressor?
If users are trying to protect cellphones and laptops, a surge protector with a minimum rating between 1,000 and 2,000 J is recommended. This rating is also large enough for building appliances and even power tools.
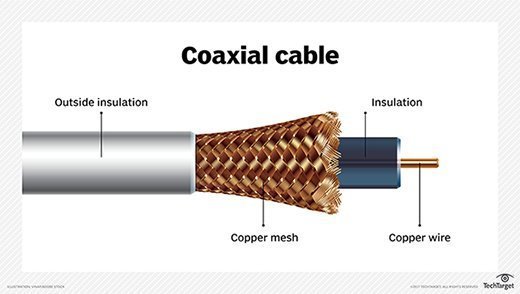
What is a surge suppressor for a coaxial cable?
If users have a coaxial cable line connected to expensive equipment, they should consider purchasing a surge protector. This is because surge suppressors protect their equipment against surges caused by lightning strikes, electrical storms and other sources of voltage spikes. Surges over coax cable lines can do just as much damage as power line surges.
See tips for making a power outage business continuity plan.
