synchronous/asynchronous API
What is synchronous/asynchronous API?
Synchronous/asynchronous APIs are application programming interfaces that return data for requests either immediately or at a later time, respectively. Synchronous/asynchronous APIs provide a way to make immediate or scheduled requests for resources, data or services when available.
Applications request data and wait until a value is returned. The synchronous or asynchronous nature of an API is a function of the time frame from the request to the return of data.
What is the difference between synchronous and asynchronous APIs?
Synchronous and asynchronous APIs differ in the following ways:
- Synchronous APIs. With synchronous APIs, the expectation is that data will be returned immediately. An API is usually synchronous when data or service availability, resources and connectivity are high and low latency is a requirement.
- Asynchronous APIs. Asynchronous APIs are also known as async APIs. With an asynchronous process, the availability of a resource, service or data store may not be immediate. The API may have to wait for a backend response. These APIs may provide a callback notification to the requester when the requested resource is ready. Asynchronous requests are useful in maintaining an application's functionality rather than tying up its resources waiting on a request. An API may be asynchronous where data or service availability and connectivity is low or oversaturated with demand.
How do synchronous and asynchronous APIs work?
One way to understand how synchronous and asynchronous functions work is to examine communications. With synchronous communications, the parties are connected in real time, such as with a telephone call. The two parties communicate back and forth in the same time frame.
Email is an example of asynchronous communications. The sender sends their message, but the recipient might not respond for some time.
In the first example, a telephone call, both parties are synchronized to enable real-time communications. In an asynchronous communication example, there is a presumed time delay or timeout while the message recipient prepares and sends a return message.
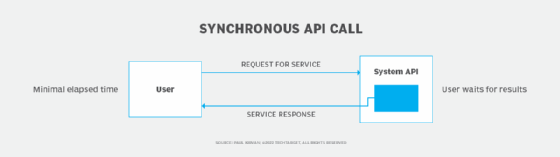
Figure 1 depicts a synchronous API request. The synchronous API call expects a time-sensitive response from the client application. Typically the requesting party waits until receiving an answer from the system.
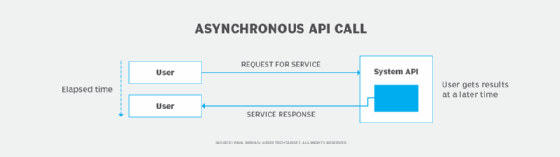
Conversely, in an asynchronous operation, the user presents a request for service and is prepared to receive the system's response later. A parameter in the app will establish a time frame for delivery of a scheduled response -- for example, within an hour -- or the app can use a flexible response time frame for the system to deliver the response.
Hybrid asynchronous and synchronous APIs
The nature of a system and the user experience are often based on synchronous or asynchronous delivery of information. With synchronous delivery, system resources may be tied up until the user request is delivered. With asynchronous delivery, fewer system resources are needed initially if responses can be delivered at a time when more system resources are available.
In either case, user requirements generally determine which approach is most appropriate.
It's possible to configure a system that blends both techniques into a hybrid arrangement that provides added flexibility and optimizes resource use. A hybrid system supports real-time HTTP and messaging protocols. Using both synchronous and asynchronous methods can result in an application environment in which system resources are most effectively used.
Find out more about how synchronous and asynchronous communication works.
