system of record (SOR)
What is a system of record (SOR)?
A system of record (SOR) is an information storage and retrieval system that stores valuable data on an organizational system or process. This record can contain multiple data sources and exist at a single location or multiple locations with remote access. However, to ensure data integrity and validity, there must be only one SOR for a given piece of information.
Subtle differences in data are common when it exists on multiple computers, due to editing or data processing. Discrepancies can occur because of bugs, file format conversion idiosyncrasies, multiple edits by humans or time frame changes, such as calendar updates. For information that does not change, such as historical data, a SOR provides a traceable source of the original data. A SOR offers the most current information for information that is subject to change, such as a bank account balance.
What is a system of record example?
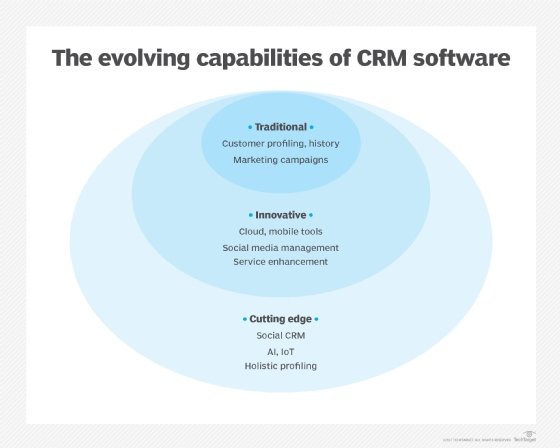
There are many types of SORs. One of the most common is a customer relationship management (CRM) system. Others include finance systems of record, like SAP; human resources systems of record; and customer systems of record.
What is the purpose of a records management system?
SOR management has many uses. It can help automate processes effectively and enhance organizational efficiency. A SOR can also be used to organize data in a centralized hub that is easily accessible. Finally, a SOR can be critical to ensuring regulatory compliance.
What is a system of record in Pega?
In Pega, the low-code platform, a SOR pattern is used when a case needs access to information stored in another application or system. The case does not own the reference data, but is referenced as required by the application to populate rules or for context.
What is a System of Records Notice?
A System of Records Notice is published by a federal agency in the Federal Register when it establishes or modifies a SOR containing information about an individual.
What are the types of record-keeping systems?
Records are kept up to date using two methods: a computerized (or automated) record-keeping system or thorough manual record-keeping.
See also: records information management, information governance, enterprise information management, systems of engagement, single source of truth, golden record and command query responsibility segregation.
