tailgating (piggybacking)
What is tailgating (piggybacking)?
Tailgating, sometimes referred to as piggybacking, is a type of physical security breach in which an unauthorized person follows an authorized individual to enter secured premises.
Understanding tailgating
Tailgating is one of the simplest forms of a social engineering attack. It is an easy way for an unauthorized party to get around security mechanisms that are assumed to be secure. The security comes into question due to a combination of human carelessness (the followed party) and ingenuity (the following party).
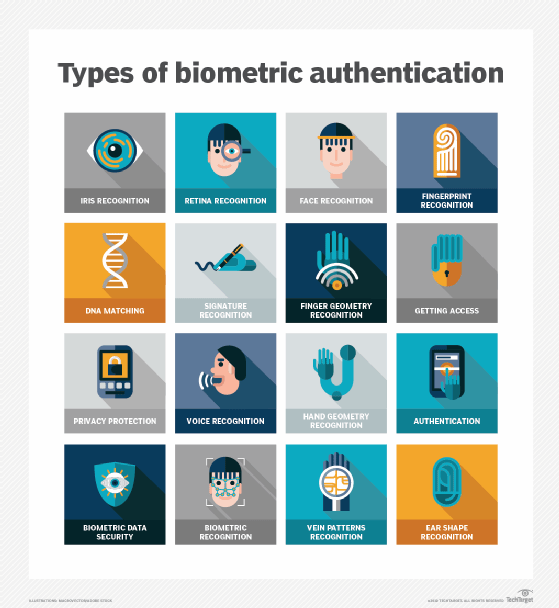
For example, a retina scanner is meant to limit entry to a physical area by scanning the retinas of authorized personnel. While retina scanning authentication works, unauthorized parties can gain access to a secured area if an employee holds the door for an unknown person behind them out of a misguided sense of courtesy or habit.
Such a polite gesture may be exploited by individuals to gain access to a location they might not have been able to access otherwise. If the individual is malicious, their entry can negatively impact the organization. For example, they may cause a data breach, steal money or destroy or damage the firm's property.
How tailgating works
One of the most common tailgating methods is someone simply following someone else through a door -- usually because an employee holds open a door for the person behind them. A more sophisticated type of tailgating attack occurs when a threat actor disguises themselves as someone else -- typically an authorized person with access to a particular area -- to trick people to gain access to that area.
Another instance of tailgating is when an authorized party enters an area and lets the door slowly close behind them. This leaves a small window of time when an unauthorized party can enter the premises.
Tailgating can also happen when a third party keeps a door propped open for some reason. For instance, a painter may be working in the office lobby, so they leave the door open to get rid of paint fumes. Or an IT vendor may be troubleshooting a server or router in the server room while leaving the door to the room open. In another scenario, someone can pretend to be a delivery person and enter a building by asking an employee to "hold the door" as they bring in a package, purportedly for someone in the building or office.
Tailgating in buildings is dangerous and a serious cybersecurity concern for enterprises.
Why tailgating happens
As mentioned earlier, one common reason an individual may tailgate is because they know that people have a tendency to be courteous and their default tendency is to leave the door open to allow the person behind them access to a building or office.
Threat actors take advantage of cognitive biases that affect human decision-making. One such "human bug" is the tendency to be courteous. Another is the tendency to trust other people. A person holding the door open doesn't typically assume that a tailgating person is not supposed to be there, or worse, intends to harm the organization.
Tailgating is a common problem in multi-tenanted buildings where many people access the building, making it difficult to track unauthorized personnel and keep them out. Tailgating also happens more often in companies where employees don't follow cybersecurity best practices. This may be due to carelessness or inadequate training. Finally, tailgating can happen in firms lacking a combination of biometric access control systems and employees with good cybersecurity hygiene.
Dangers of tailgating
People who might tailgate include disgruntled former employees, thieves, vandals, mischief makers and anyone who has an issue with an employee or the company. Thus, tailgating personnel may be innocent or malicious, but either can potentially disrupt the business, cause damage, create unexpected costs, and lead to further safety issues because they didn't follow proper security protocols when entering an area.
Tailgating is a significant security risk for organizations and their property, equipment, data and personnel. Malicious actors who tailgate might want to gain access to the company's premises to steal valuable equipment such as unattended laptops or exfiltrate sensitive information. They may want to insert spyware into enterprise devices or install malware or ransomware on specific computers.
Some attackers tailgate to access the server room and create a backdoor to the entire enterprise network. This provides access to the network allowing them to control devices and steal data, company secrets or funds.
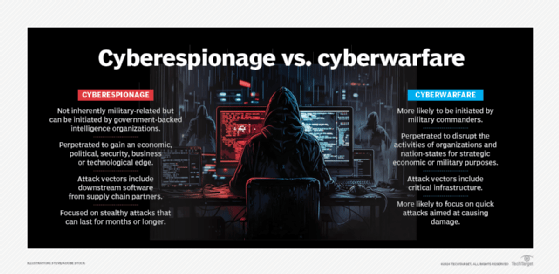
Tailgating can also result in physical violence or vandalism. Determined tailgaters can also surreptitiously install cameras to remotely keep an eye on company operations and engage in corporate or cyberespionage.
How to prevent tailgating
Organizations must implement effective security to protect the premises from unauthorized personnel and prevent tailgating. These are the most effective methods:
Ensuring that doors close swiftly and securely
Installing access controls for entrances and restricted areas with swiftly closing doors is vital. Additionally, security revolving doors provide tailgating detection and ensure that an individual is alone, meaning someone else cannot enter behind them without going through a proper access mechanism.
Biometric scanners
Biometric scanners and turnstiles allow only one person to enter an area at a time. They prevent tailgaters from walking with or behind an authorized person inside a building or office. Electronically controlled access controls and smart cards for entrances and restricted areas are also critical to prevent tailgating.
Photo ID
Employees must be required to wear photo IDs and visitors must be required to wear badges. All IDs must be clearly visible. With these ID methods in place, anyone not wearing them become conspicuous, making it easier to recognize and detain them, and prevent them from entering secure premises.
Video surveillance
Surveillance devices such as CCTVs provide a means to keep an eye on the premises 24/7. If the devices are clearly visible, they act as a deterrent to those looking to tailgate their way into an office or server room.
Multifactor authentication (MFA)
MFA on access doors can prevent unauthorized persons from accessing secure areas. One example is a server room door that requires both an access card and a thumb print. Another example is a file room where entrants must show a smart card and provide a retina print.
Security guards
Security guards provide a physical means to safeguard premises. These guards should be trained to ask unfamiliar personnel or personnel not wearing ID cards who they are and why they are on the premises.
Laser sensors or mantraps
Photosensors, laser sensors and mantraps can limit entry to a single person at a time, preventing someone from following them and entering an area they are not authorized to enter.
Employee education
The presence of security measures can create a false sense of security and result in people ignoring simple methods of subverting security. That's why it is vital to educate employees on how to recognize and resist tailgating. Educating employees on the dangers of tailgating can significantly reduce the threat.
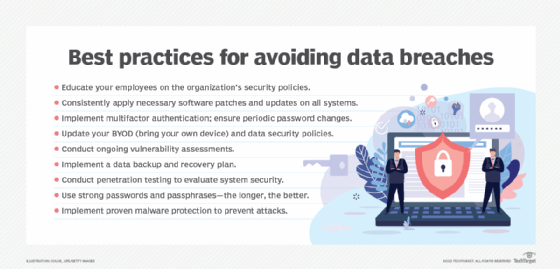
Creating a strong cyber awareness culture throughout the organization and making employees aware of their responsibilities to protect the company's assets from unauthorized parties is essential. Employees should be taught these security best practices:
- Never hold the line for anyone.
- Stop people from following them into special access zones or restricted areas.
- Stop people who are not wearing employee or visitor badges and direct them to reception.
- Report suspicious activity to security guards.
- Always direct visitors or guests who appear "lost" or out of place to the reception desk.
- Inform security guards or the IT team if an electronic door is not functioning properly.
- Always close doors, especially to secure or restricted areas like server rooms.
- Ensure that any outsiders, such as repairmen or delivery persons, are legit and wearing appropriate badges.
- Never allow former employees -- even those who are familiar or friendly with a current employee -- to access the company premises if they don't have the permission of authorized personnel (e.g., IT team) or are not wearing proper ID badges.
See also: watering hole attack, dumpster diving, shoulder surfing
