timestamp
What is a timestamp?
A timestamp is the current time of an event that a computer records. Through mechanisms, such as the Network Time Protocol, a computer maintains accurate current time, calibrated to minute fractions of a second. Such precision makes it possible for networked computers and applications to communicate effectively.
The timestamp mechanism is used for a variety of synchronization purposes, such as assigning a sequence order for a multievent transaction so the transaction can be voided if a failure occurs. Another way that a timestamp is used is to record time in relation to a particular starting point in time.
In IP telephony, for example, Real-time Transport Protocol assigns sequential timestamps to voice packets so that they can be buffered by the receiver, reassembled and delivered without error. When writing a program, the programmer is usually provided an application programming interface for a timestamp that the operating system (OS) can provide during program execution.
What are timestamps used for?
Timestamps are used for keeping records of information online or on a computer. A timestamp displays when certain information was created, exchanged, modified or deleted.
The following are examples of how timestamps are used:
- Computer files may contain a timestamp that shows when the file was last changed.
- Digital cameras attach timestamps to photographs that show the date and time of day a picture was taken.
- Social media posts include the date and time the post was made.
- Online chat and instant messages use timestamps to record the date and time when a message was sent, received or viewed.
- Blockchain blocks use timestamps to ensure the validity of transactions, such as with cryptocurrencies.
- Data management relies on timestamps to ensure the integrity and quality of data.
- Digital contracts and digital signatures use timestamps to show when a document was signed.
Some timestamp uses, such as digital signatures, require a high level of reliability for legal reasons. A trusted third party may generate a timestamp for the document instead of using the time from the machine on which the document is stored. These third parties are known as Time Stamping Authorities. TSAs use public key infrastructure -- the processes and technologies that enable encryption and data signing -- to ensure their timestamps are valid and secure from manipulation.
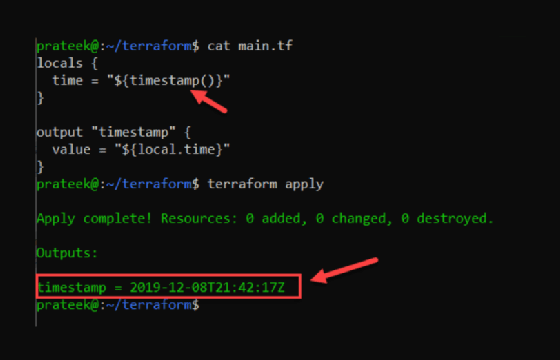
Different timestamp formats
Timestamps vary depending on the medium in which they're used. Timestamp formats are different across OSes, programming languages, databases and data types.
Some timestamp formats are shown in the following examples, where y stands for year, d for day, h for hour, m for minute and s for second:
- dd hh mm ss
- yyyy mm dd hh
- mm hh
Here are examples of what a timestamp might look like with those values filled in:
- Fri 01-01-2010 6:00
- 2015-10-28 T 10:45 UTC
- Sun Jul 16 02:15:58 2006
- 2019-10-31T03:58:22Z (International Organization for Standardization 8601)
All clocks and time zones worldwide are set based on Coordinated Universal Time (UTC).
A timestamp's format can also be as simple as the read receipts on a text message. The format is something like "Seen 9:18 a.m." This indicates when the recipient saw the message.
Timestamps also differ in the way they are calculated. A computer's internal clock and timestamp values are determined based on an epoch. A computer's date and time are determined based on the number of seconds that have passed since that computer's defined epoch. The epoch's time corresponds to 0 hours, 0 minutes and 0 seconds UTC, and the epoch date depends on the OS used.
For example, the Unix epoch date is Jan. 1, 1970, so Unix systems calculate timestamps relative to this date. On Windows computers, the epoch date is Jan. 1, 1601, and on older Macintosh computers, the epoch date is Jan. 1, 1904.
How do I convert a timestamp?
Web users can easily convert a Unix epoch timestamp to a human-readable date and vice versa using a free online conversion tool. For example, if the Unix epoch time is 1639172876 seconds, then the human date would be Friday, Dec. 10, 2021, at 9:47:56 p.m. This timestamp written in a dd mm yyyy hh mm ss format would be 10-12-2021 9:47:56.
If a user has a list of Unix timestamps in Excel, they can convert the timestamps into human-readable dates using the following formula: (A1-DATE(1970,1,1))*86400, where the Unix timestamps are in column A. Users can enter that formula in a blank cell in Excel to convert the timestamp into a date and then press the enter key.
Various programming languages have different ways of converting a Unix timestamp. A timestamp's default format in Java might be different than a timestamp's default format in Python, and each language has different ways of calling those timestamps.
Timestamps in blockchain
Timestamps play an important role in blockchain, particularly in its use with cryptocurrencies. Each block in the blockchain has a header, which contains the Unix time that the block was hashed. The timestamp gives each block a unique mark and prevents double spending.
Blockchain is also used in other applications, such as content timestamping. In this context, blockchain-based timestamps prove the content on a page was published at the timestamped date. Blockchain can also be used in elections to prove the validity of a vote and help eliminate fraud.
Blockchain mining
Unix timestamps are used to show how long it took to mine a block, which determines how much revenue the miner gets. Miners gain revenue by producing blocks quickly.
It's possible for a bitcoin miner to change a timestamp while hashing it to make it appear as though the block was created faster than it actually was. However, the following two rules prevent miners from doing this:
- The median past time rule requires the timestamp be higher than the median of the timestamps of the past 11 blocks. In other words, they would need to calculate the hashes of six of the past 11 blocks.
- The future block time rule requires the timestamp cannot be more than two hours in the future from the miner's computer's local time.
Rule No. 1 ensures that the chain moves forward at a steady rate. Rule No. 2 ensures that the chain doesn't move too far forward. Both rules allow block generation to happen at a steady rate. They make it difficult for miners and other blockchain users to manipulate their timestamps.
Blockchain technology isn't foolproof. Learn about some blockchain security threats businesses should prepare for.
