transparency
What is transparency?
Transparency is the quality of being easily seen through, while transparency in a business or governance context refers to being open and honest.
As part of corporate governance best practices, this requires disclosure of all relevant information so that others can make informed decisions.
In a computer science context, the meaning of transparent signifies invisible or undetectable.

What are the implications of transparency for businesses?
The implication of transparency is that all of an organization's actions should be scrupulous enough to bear public scrutiny.
Increasingly, the nature of social media and other communications means that even actions intended to be secret may be brought into the public's awareness, despite an organization's best efforts to keep them hidden. This puts pressure on businesses to change the way they operate to be more transparent.
There are several benefits that can come from transparency for both businesses and consumers. The following are some of these benefits:
- improved customer relationships
- increased trust
- greater employee engagement
- enhanced reputation
- better decision-making
Conversely, there are also some risks associated with transparency, such as exposing trade secrets, damaging relationships with customers or employees and succumbing to customer data privacy breaches.
How can businesses be transparent while also keeping data safe?
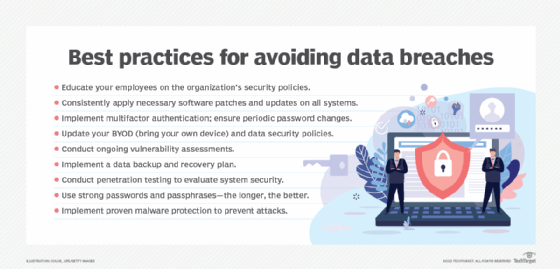
The number of data breaches in recent years has raised public concern about how much data is collected and whether it is shared with third parties.
This has led to calls for more transparency from businesses about what data they collect, how they use it and who it is shared with.
The European Union's General Data Protection Regulation is one response to these concerns and requires businesses to be more transparent about the data they hold on EU citizens.
Transparency is also a key element of ethical business practices. Businesses that are transparent in their dealings are more likely to gain the trust of their employees, customers and other stakeholders.
A lack of transparency can erode trust and lead to suspicions of unethical or illegal activity. In some cases, this can result in boycotts or other forms of protest against the business.
Thus, while total transparency is not always possible or desirable, being open and honest in business dealings is essential to maintaining good relationships with stakeholders.
Are there circumstances in which transparency is bad?
There are some circumstances in which transparency is not possible or desirable. For example, transparency is often not possible in negotiations, where revealing too much information about one's position could weaken bargaining power.
Similarly, transparency is not always desirable in law enforcement or national security contexts, where disclosing information could jeopardize ongoing investigations or endanger lives.
In these cases, it is important to balance the need for transparency and other considerations, such as public safety or, as discussed in a previous section, data privacy.
Learn why AI transparency mandates are essential to protect private data, and explore how the future of trust will be built on data transparency.