What is Twitter?
Twitter is a free social networking site where users broadcast short posts known as tweets. These tweets can contain text, videos, photos or links. To access Twitter, users need an internet connection or smart phone to use the app or website, Twitter.com.
It is a microblogging service -- a combination of blogging and instant messaging -- for registered users to post, share, like and reply to tweets with short messages. Nonregistered users can only read tweets.
People use Twitter to get the latest updates and promotions from brands; communicate with friends; and follow business leaders, politicians and celebrities. They also use it to stay current on news and events. Twitter was the first source to break the news of the water landing of US Airways Flight 549 in New York City's Hudson River.
Twitter is used to share information quickly. Because tweets can be delivered to followers in real time, they might seem like instant messages (IM) to the novice user. But unlike IMs that disappear when the user closes the application, tweets are also posted on the Twitter website. They are permanent, searchable and public. There is also an option to protect tweets so only followers can read tweets.
History of Twitter
In March 2006, Jack Dorsey, Noah Glass, Biz Stone and Evan Williams created Twitter. The idea for Twitter came from wanting to use a short messaging system for a small group. It was available to the public in July 2006.
The definition of twitter is a short burst of inconsequential information and chirps from birds, which describes the purpose of social networking on Twitter -- to share short and quick information.
Other Twitter notables:
2012: More than 100 million users post 340 million tweets daily.
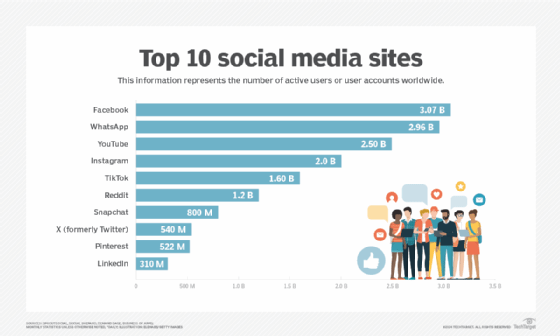
2013: Twitter is in the top 10 of the most visited websites.
2013: Twitter files for IPO in September.
2019: Twitter has more than 330 million active users.
2022: Elon Musk, CEO of SpaceX and Tesla, reaches an agreement to acquire Twitter for $44 billion to make it a private company in April. Acquisition was finalized in October.
2023: Twitter partners with investing platform eToro in April to let users access and trade stocks, cryptocurrencies and other assets from links to eToro. Musk appoints Linda Yaccarino as the new CEO of Twitter in May.
How Twitter works
Users choose what they want to see on Twitter by following other users and companies and searching topics. Generally, the timeline reflects the users' preferences, but they may see retweets from people they follow and promoted Tweets, which are paid advertisements.
Searching on Twitter
In the search bar, users can type in a person, topic or keyword to search. There is also an #Explore function to search for keywords and trending topics.
Twitter determines what is trending based on an algorithm and users' preferences, locations and interests. This algorithm also determines what is popular now and highlights emerging discussions and topics.
To help limit fake accounts, Twitter created the verified account symbol, which indicates the account is legitimate and belongs to the person or company. To get verified, Twitter confirms the identity of the individual or company. This helps maintain trust with users. The account must be associated with a popular brand or person and follow Twitter's criteria using an official website, ID or email address to be verified.
Following users
On Facebook or LinkedIn, members need to approve social connections. But that is not the case with Twitter. Anyone can follow anyone. After finding a contact on Twitter, users can hit "Follow" on their profile page.
Posting a tweet
When users post a tweet, the messages are posted on their profile and then appear in followers' feeds. These tweets can also be searched on Twitter. Tweets include jokes, news, random thoughts and sharing articles; however, there is a restriction on length. Originally, Twitter limited tweet characters to 140. The limit is now 280 characters, which includes spaces and punctuation.
To weave tweets into a conversation thread or connect them to a general topic, members can add hashtags to a keyword in their post. The hashtag, which acts like a meta tag, is expressed as #keyword. This makes the tweet searchable under that keyword.
Twitter also offers TweetDeck to manage multiple accounts, schedule future tweets and more.
Interacting on Twitter
Users can choose to retweet someone else's post, which forwards it to followers' timelines. They can also comment on or reply to posts. To show agreement, registered members can like a tweet.
In addition to posting tweets, users can send links and messages to each other through direct messaging. These direct messages are private between the parties sending the messages. There is a setting to receive direct messages from anyone, meaning users do not have to follow each other to start a conversation.
Business uses for Twitter
Businesses use Twitter for brand awareness and public relations -- part of their social media marketing strategy. Using Twitter helps businesses:
- interact with customers;
- provide timely customer service;
- monitor the competition; and
- announce new products, sales and events.
Businesses can also purchase promoted tweets -- or ads -- to help marketers reach more users or engage with followers. These tweets appear just like other posts but are labeled "promoted."
Twitter risks
Because information spreads quickly on Twitter, there are risks. Some of these include the following:
- Spreading of fake news or disinformation. Information is posted in real time, so it is hard to stop or slow down the spread when it comes to fake news. Twitter launched the Birdwatch program in 2021 to help limit tweets from spreading disinformation. Users should learn to spot disinformation and report these tweets if needed. Twitter will review and then suspend accounts if necessary.
- Twitter bots. These computer programs tweet, retweet and follow other accounts. These fake accounts can build large follower bases for advertisers when users respond. They mimic human communication and can also spread disinformation or propaganda quickly.
- Harassment and negative comments. This can affect both individuals and businesses.
- Data security and privacy. Twitter was hacked in July 2020 by cryptocurrency fraudsters. The scam included posting tweets from hacked accounts asking people for bitcoin currency with the promise that Twitter would double the money for a charitable donation. It scammed people out of nearly $100,000. Hackers also get into accounts to post information from that person, typically a public figure.
Changes to Twitter since Musk takeover
Since Musk took control of Twitter in October 2022, he made some changes to the organization, including an official legal name change to X Corp. revealed in an April 2023 court filing. Other changes include:
- X Premium. X Premium is a paid subscription that offers additional features in three tier levels: Basic, Premium and Premium+. Basic features include editing posts, longer posts, longer video uploads and custom app icons. The Basic price is $32/year. Premium includes all the Basic features plus a checkmark, reduced ads, ID verification and access to Grok -- Twitter’s conversational AI. The Premium price is $84/year. Premium+ includes all Premium features plus no ads in the For You and Following timelines and Articles. The Premium+ price is $168/year.
- Company layoffs. Since October 2022, Musk has reduced Twitter staff by about 80%, which is around 6,000 employees. Before the takeover, Twitter had approximately 8,000 employees, and as of April 2023, there are around 1,500 employees after layoffs.
- Twitter feed views. Users can now select which tweets they want to see in their timeline between tweets recommended by Twitter or latest tweets from people users follow.
- Reinstatement of controversial accounts. Musk reinstated some high-profile accounts after his takeover, including former U.S. President Donald Trump, rapper Ye (Kanye West) and influencer Andrew Tate, who is imprisoned in Romania for human trafficking charges. All these accounts were previously banned for controversial content.
- Account identification and verification. The blue checkmarks were previously used in Twitter’s verification process. Now the ticks are gold or silver for brands and government figures. There is also an explainer added saying “official business.” For celebrities and other public figures, they can only keep their blue checkmark if they are members of Twitter Blue to prove authenticity of the account.
- Encrypted direct messages. Verified users can send encrypted messages to other verified users or organizations. The encrypted messages are protected by an algorithm to scramble information so only the sender and intended recipient can read it. To send an encrypted message, eligible users will use the toggle to enable “encrypted mode.” Encrypted messages have a lock icon.
- Video and voice calling features. Twitter will launch video and voice calling features to allow users to call others directly from the platform, according to Musk. There is no timeline or date when this feature will be available.
Controversy after the takeover has also been in the news. In April 2023, NPR and PBS announced they would no longer use Twitter after being labeled “government-funded media.” NPR announced this label undermined its credibility as an editorially independent organization. BBC was also branded as “government funded media,” causing BBC to request a swift resolution.
In April 2023, New York’s Metropolitan Transportation Authority (MTA) – the nation’s largest mass-transit provider-- halted using Twitter after the platform was going to charge $500,000 a year to use their services. In May 2023, Twitter reversed its decision to charge government entities to use their services. Twitter now offers free API access for public service.
Twitter changes to X
In July 2023, Musk announced he is officially rebranding Twitter to X. The iconic blue bird logo has been replaced with an X, and X.com redirects to Twitter.
Musk plans to make X a super app, which includes payment services, messaging and social media much like China’s WeChat app. As of July 2023, the move remains a name change.
Musk may face a legal battle to change the name to X as other companies – such as Meta and Microsoft -- have intellectual property rights to the letter X.
