virtual CPU (vCPU)
What is a virtual CPU (vCPU)?
A virtual CPU (vCPU) is the processor of a virtual machine (VM). Each vCPU represents the ability to run one processing thread at a time. The VM hypervisor manages the scheduling of the vCPU time to the physical CPU.
How do virtual CPUs work?
Computers need three major resources to function: storage (disk space), memory (RAM) and compute (CPU). In a VM, the hypervisor manages the guest virtual machines (guest VMs) and tells or assigns them how much virtual resources they have access to. The hypervisor then schedules the demand from the guest VM to the physical hardware.
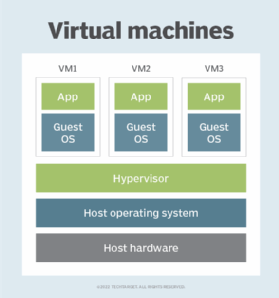
Each vCPU represents the ability to run one processor thread on a system's physical CPU simultaneously. So, for every vCPU, there's a processor thread running for each on the physical CPU. For example, if a VM is assigned four vCPUs, the operating system (OS) would expect that it can run four threads at a time. The hypervisor will then be responsible for scheduling the incoming threads from the guest VM to the physical CPU for execution.
Modern virtualized systems do not permanently assign one single vCPU to a single physical CPU. Instead, they take the incoming threads from the VMs and assign them as needed in a time sharing fashion to the physical CPU cores as they are available. This allows for better utilization of the CPU resources.
Complicating matters, most modern server CPUs can run two threads per CPU core using simultaneous multithreading or hyperthreading. Each vCPU represents about half of a physical core of processing ability or one CPU thread.
VCPU oversubscription
Assigning more vCPUs than available physical cores is called oversubscription. A moderate amount of oversubscribing is usually acceptable because most VMs rarely use all their available CPU. Instead, they often sit mostly idle for long stretches of time and then use a lot of resources for a short burst of activity.
If many vCPUs are used at the same time in an oversubscribed system, there may be resource contention, and performance will suffer. To limit the possibility of this, it is best to plan out how many vCPUs are used by taking into account the total physical CPUs and the expected workload. For example, an end-user client VM will have erratic performance ups and downs depending on the user activity, while a server will be more predictable. Some VMs may always run at high CPU utilization and should not be oversubscribed.
Cloud providers may or may not oversubscribe vCPUs depending on the VM type, cost and terms of service. For instance, most high-end AWS tiers dedicate one vCPU per physical CPU thread. Some smaller AWS T2 instances are instead classified as Burstable Performance Instances, which are limited to not using an entire physical CPU core all the time.
For dedicated VM hypervisors, admins can set rules to determine how they will handle resource contention. For instance, VMware ESXi will assign all VMs equal priority by default. If administrators want to make sure one VM always has a certain amount of capacity, they can set a reservation to dedicate a certain amount of the physical CPU power to it. A share can also be specified to give one VM higher or lower priority than others in the case of resource constraints.

How many vCPUs are in a CPU?
Generally, it can be said that there is one vCPU at a time per physical CPU thread. Most physical server CPUs have two threads per core, so two vCPUs per CPU core. To calculate the number of vCPUs for Intel Xeon and AMD processors, take the number of physical CPU cores and multiply by two.
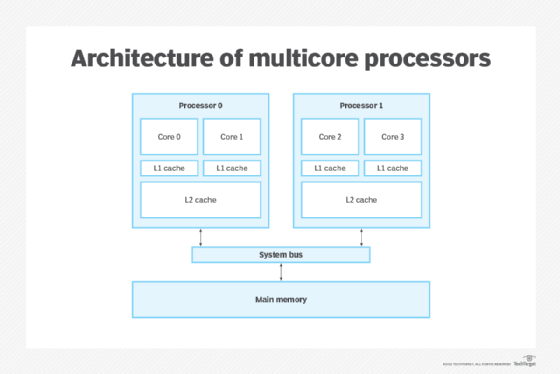
For CPUs without multithreading, such as with Arm processors, it is one vCPU per physical CPU core.
Practically, admins can assign as many vCPUs per physical CPU core as utilization will allow.
Learn how to choose the best CPU for virtualization and check out our ultimate guide to server virtualization.
