e-learning (online learning)
What is e-learning?
E-learning -- also called electronic learning or web-based training -- is anywhere, anytime instruction delivered over the internet or a corporate intranet to students and other learners via a browser. Contrary to traditional learning methods, e-learning lets students, employees in training and casual learners participate in an organized learning experience regardless of their physical location.
In its formative years, e-learning tools primarily enabled the delivery of learning material directly from a teacher to a learner. Now, the e-learning experience has evolved to enable more multidirectional communication using increasingly interactive tools. Learners have greater freedom in choosing how they receive and respond to e-learning content, and any number of peers can be involved.
Why is e-learning important?
E-learning methods and technology are important both for educating students and for the professional development of employees in the workforce.
The rapid evolution of technology has made it increasingly important for employees to have the right skills and training. For example, it's expected that the emergence of quantum computing capabilities will create a massive shift in the way modern businesses operate that will affect coders, hardware developers and online security professionals. Learning environments, such as e-learning, will play a key role in retraining and reskilling many of these people.
In addition, companies are increasingly turning to online learning for ongoing training and upskilling employees. Learning management systems (LMSes) are particularly popular in corporate settings. Higher education institutions also use online learning methods along with internet-capable electronic devices, both inside and outside of traditional classrooms. According to McKinsey & Company's 2022 survey of 7,000 students in 17 countries, 65% of higher education students want schools to retain aspects of online learning in the post-pandemic world.
How e-learning works
Online education is delivered using a combination of static and interactive methods. Static approaches include learning portals, hyperlinked pages, screen cam tutorials, streamed audio and video and live web broadcasts. Interactive methods are approaches such as discussion forums, chats and desktop video conferencing.
There are three main criteria an enterprise should follow to ensure an effective e-learning program:
- Mobile-friendly. People live on their devices, and e-learning must take advantage of that. Training prompts, other reminders and congratulations on training achievements should be sent to smartphones and other mobile devices through mobile apps.
- Social features. Social media, or a platform that emulates social media's basic features, can give learners a way to receive updates, respond to training requirements and communicate with peers and managers.
- Instructional design. E-learning experiences should use a wide range of offerings to suit diverse learning styles, including quizzes, infographics, podcasts, demonstrations and narrative-based training materials. E-learning course development apps use authoring tools that allow even those without coding experience to create these different offerings.
Types of e-learning
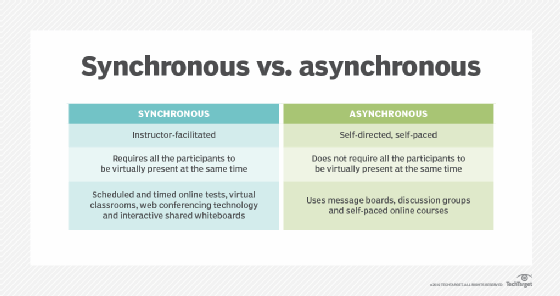
There are two primary models of web-based learning systems: synchronous, also known as instructor-led, and asynchronous or self-directed and self-paced. Basically, synchronous e-learning requires participants to be present, albeit virtually, at the same time, whereas asynchronous e-learning does not.
Examples of synchronous e-learning methods include the use of scheduled and timed online tests, virtual classrooms, web conferencing technology and interactive shared whiteboards that learners can use to collaborate. Examples of asynchronous e-learning methods include the use of discussion boards, discussion groups and self-paced learning courses.
Advantages of e-learning
There are many benefits of e-learning, which proponents believe outweigh the disadvantages. They include the following:
- On-demand availability. E-learning tools and services meet the needs of those with busy schedules because they're commonly always available on demand. Learners can access material delivered online as long as they have access to the e-learning application.
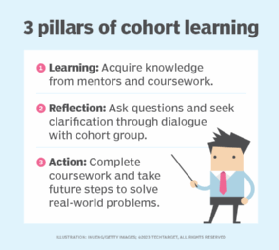
- Not requiring travel. E-learning is especially conducive to cohort learning where groups of people who live in different locations work on obtaining a new skill or knowledge set
- Cost efficiency. In a traditional, in-person classroom setting, the cost of the space, infrastructure, maintenance and materials adds up. Most of these costs go away when learners online.
- Flexibility. Web-based training and e-learning enable flexibility, letting learners consume information at their own pace.
Disadvantages of e-learning
Critics point out the following disadvantages related to e-learning:
- Need for human contact. Web-based training is a good alternative for independent, self-motivated students, but the need for human contact limits its usefulness for students with other learning styles. For example, a learner using an asynchronous e-learning method might not be able to successfully complete an e-learning course without the structure of a deadline. They might also need instant responses to questions that an asynchronous system doesn't provide.
- Technical issues. Students connecting virtually often must use their own devices to attend online classes and complete assignments. Connecting and staying connected requires the right devices and network access that all students might not have.
- Lack of transparency. Sometimes the quality and credibility of the content or the teacher isn't always clear and transparent on every e-learning platform. This is especially an issue on free and easily accessible resources.
E-learning platforms
There are a variety of e-learning platforms, both synchronous and asynchronous, that users can use in education, business and independent environments. These powerful software suites enable digital learning and online training, providing courses, presentation capabilities like PowerPoint, online examinations and analyzing student performance data. A few examples of these platforms are Anthology for Business, Canvas, Moodle, Sakai and Schoology.
Learning management systems are also prevalent in the enterprise for onboarding and employee training programs. The best types of corporate LMSes are scalable, customizable, goal-oriented and user-friendly. Some enterprise-level LMSes, all with varying pricing plans, include Adobe Learning Manager, Docebo, eFront, iSpring Learn, Looop by 360Learning, Northpass and TalentLMS.
Social media
Social media provides useful tools for e-learning. These platforms bring communities of learners together and let them share e-learning content. The following are examples of how they can be useful:
- Facebook users can create groups to share information and ideas, and members of such groups can communicate freely about the shared material.
- LinkedIn enables similar groups that might be perceived as having an added level of credibility because users display their career credentials on their profiles. LinkedIn also has a paid platform for e-learning called LinkedIn Learning that features over 4,000 business courses. The topics of these courses vary from web development to digital marketing. Business professionals can pay a monthly fee to use these courses to keep their skills up to date.
- X (formerly known as Twitter) can connect learners by using a hashtag for a specific topic or event.
- YouTube users can post and access educational content for free, as well as comment on and rate the videos.
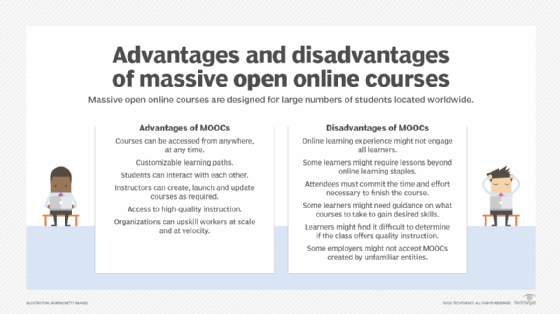
Massive open online courses
Independent learners can also take advantage of massive open online courses (MOOCs) on the web. MOOCs are made available through popular platforms like Coursera and edX to large groups of people over the internet, usually for free. Often, these courses are modeled on ones taught by top-tier universities, which is great for learners who want quality training content for free. Users can log into a MOOC's website and sign up for a given course. Certain MOOC programs, such as edX's certificate programs, charge a student looking to earn a specific certificate for the completion of their coursework.
Other platforms, such as Udemy and Skillshare, are similar to MOOCs in that they are available online and can accommodate large groups of learners. However, they are different in that they charge the user and focus on practical engagement with material as opposed to passive learning methods, such as the lectures that come with more university-centric MOOCs. No matter the platform, e-learning is a flexible, adaptable way for professionals and students alike to learn new skills and bolster existing ones.
History of e-learning
The idea of e-learning predates both the internet and the coining of the term e-learning. In 1983, Ron Gordon, former president of Atari and founder of TeleLearning Systems, launched an effort to create an Electronic University Network. EUN was an early online educational network aimed at helping universities and colleges provide and use online courses. EUN was bought by KnowledgeNet in 1987 and incorporated into its offerings.
When the World Wide Web was created in 1989, it was initially seen as a means of exchanging information among academic institutions more rapidly and easily, before it became what it is today.
The term e-learning was first coined in 1999. Around the same time, various online course implementations were launched, such as MIT's OpenCourseWare project in 2002. In the late 2000s, these types of courses and the technology they used advanced enough to accommodate large groups of learners, and MOOCs appeared. In recent years, most companies and higher education institutions have embraced e-learning after discovering its benefits, especially during the COVID-19 pandemic.
E-learning is now a market of its own with many different providers that cater to business training needs. Find out about e-learning providers that might be useful for your business.