virtualization architecture
What is virtualization architecture?
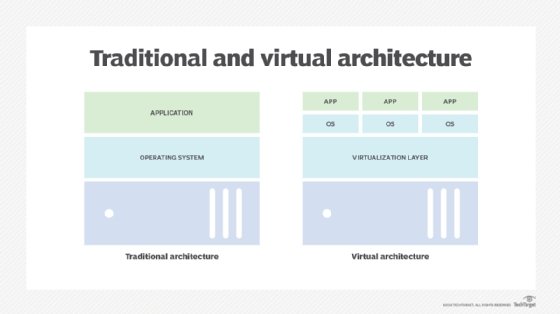
A virtualization architecture is a conceptual model of a virtual infrastructure that is most frequently applied in cloud computing. Virtualization itself is the process of creating and delivering a virtual rather than a physical version of something. This could be a desktop, an operating system (OS), a server, a storage device or network resources.
The architecture clearly specifies the arrangement and interrelationships among the particular components in the virtual environment.
In cloud computing, virtualization facilitates the creation of virtual versions of hardware such as desktops, as well as virtual ecosystems for OS, storage, memory and networking resources. A virtualization architecture runs multiple OSes on the same machine using the same hardware and also ensures their smooth functioning.
In a virtualization architecture, specialized software is used to create a virtual version of a computing resource. This eliminates the need to re-create an actual version of that resource. A logical name is assigned to the resource and a pointer is provided to that resource on demand. As a result, multiple OSes and applications can run on the same machine and multiple users (or organizations) can share a single physical instance of a resource or application at the same time.
The virtualization architecture is a visual depiction or model of virtualization. It maps out and describes the various virtual elements in the ecosystem, including the following:
- application virtual services
- infrastructure virtual services
- virtual OS
- hypervisor
The application and infrastructure virtual services are embedded into a virtual data center or OS. The hypervisor separates the OS from the underlying hardware and enables a host machine to simultaneously run multiple VMs which will share the same physical resources.
Cloud computing and virtualization architecture
Virtualization and virtualization architecture are important ideas in cloud computing. In fact, the terms are often used interchangeably because cloud computing by definition involves virtual ecosystems. Regardless of whether the ecosystem is private (private cloud) or public (public cloud), virtualization reduces the need for organizations to maintain a physical (on-premises) infrastructure for their computing requirements.
With cloud computing and a virtualization architecture, applications can be shared across multiple active users. In the case of public clouds like Amazon Web Services (AWS) or Microsoft Azure, they can also be shared across multiple enterprises (also known as customers or tenants).
Types of virtualization architecture
There are two major types of virtualization architecture: hosted and bare-metal. It's important to determine the type that will be used before implementing virtualized systems.
Hosted architecture
In this type of setup, a host OS is first installed on the hardware, followed by the software. The software, which is a hypervisor or virtual machine (VM) monitor, is required to install multiple guest OS or VMs on the hardware in order to set up the virtualization architecture. Once the hypervisor is in place, applications can be installed and run on the VMs just like they are installed on physical machines.
A hosted architecture is best suited for the following:
- software development
- running legacy applications
- supporting multiple OSes
- simplifying system configuration
Bare-metal architecture
In this architecture, a hypervisor is installed directly on the hardware instead of on top of an OS. The installation for the hypervisor and VMs happens in the same way as with hosted architecture. A bare-metal virtualization architecture is suitable for applications that provide real-time access or perform some type of data processing.
Benefits of bare-metal virtualization include the following:
- effective resource management
- high resource availability
- higher scalability
- better system performance and stability
More about hypervisors in virtualization architecture
Virtualization is hypervisor-based. The hypervisor isolates the OS and applications from the underlying computer hardware so the host machine can run multiple VMs as guests that share the system's physical compute resources, such as processor cycles, memory space and network bandwidth. Simply put, the hypervisor separates the available power, memory or storage resources and assigns some of these resources to each VM as needed in the virtualization architecture.
Type 1 hypervisors, sometimes called bare-metal hypervisors, run directly on top of the host system hardware. Bare-metal hypervisors offer high availability and resource management. Their direct access to system hardware enables better Performance, scalability and stability. Examples include the following:
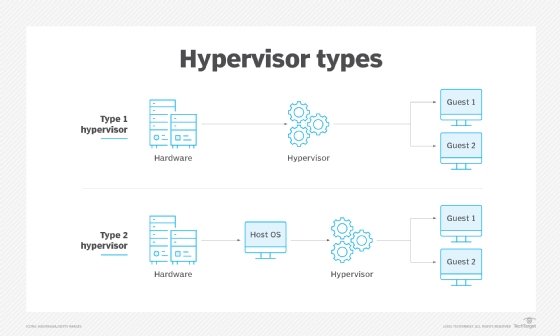
A type 2 hypervisor, also known as a hosted hypervisor, is installed on top of the host OS, rather than sitting directly on top of the hardware as the type 1 hypervisor does. Each guest OS or VM runs above the hypervisor. The convenience of a known host OS can ease system configuration and management tasks. However, the addition of a host OS layer potentially can limit performance and expose possible OS security flaws. Examples include the following:
- VMware Workstation Pro
- VMware Fusion
- Oracle VirtualBox
- Oracle Solaris Zones
- Oracle VM Server for x86
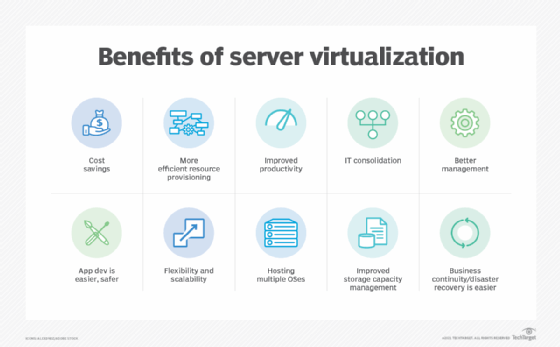
Benefits of a virtualization architecture
A virtualization architecture provides cloud-native organizations with a flexible, cost-effective, highly available way to run multiple virtual OSes or machines using one dedicated resource or host machine. It thus ensures more efficient and affordable resource allocation and also lowers IT infrastructure costs. Also, since the host user can restrict the number of users for the virtual resources, the environment provides better resource control while also reducing unnecessary power and resource consumption.
Virtualization also supports remote, anytime-anywhere access, which is critical for remote or geographically dispersed teams. It also reduces the need for physical resources such as servers, which ensures higher uptime and fewer disruptions, better fault-tolerance, efficient load balancing and more available resources. In addition, resources can be spun up or removed on demand, providing greater scalability and agility for enterprise teams.
All major public cloud providers provide virtualized architectures based on a pay-per-use pricing model. This ensures that organizations only pay for what they actually use instead of having to pay for unused or idle resources or capacity. Consequently, they get better control over their cloud budgets and spends.
Virtualization is also useful from a security standpoint. Each VM can have many guest users that can be OSes, devices, applications, etc. Additionally, the various VMs can be isolated so each guest user gets an isolated virtual environment. Such isolation helps to protect sensitive or business-critical information.
Finally, a virtualization architecture supports aggregation through cluster management software. This software helps to connect homogenous sets of machines or networks that can then act as one unified, aggregated resource.
Virtualization and containerization
In cloud computing, one alternative to hypervisor-based virtualization is containerization. Operating system virtualization, for example, is a container-based kernel virtualization method. In this architecture, an OS is adapted so it functions as multiple discrete systems, making it possible to deploy and run distributed applications without launching an entire VM for each one. Instead, multiple isolated systems, called containers, run on a single control host and all access a single kernel.
Like a VM, a container is a way to create self-contained virtual packages. Essentially, a container is a lightweight VM that is a subset of the same OS instance or the hypervisor. However, where virtualization is a way to run multiple OSes on the hardware of a single physical server, containerization is a way to deploy multiple applications using the same OS on a single VM.
A VM is best suited for applications where an operating system's full functionality is required. Containers are a better choice for tasks with shorter lifecycles and where there is a need to reduce the number of servers being used for multiple applications.
Explore benefits of server virtualization to business, ways to create a server consolidation project plan and considerations for creating a VM for a development environment.