systems development life cycle (SDLC)
The systems development life cycle (SDLC) is a conceptual model used in project management that describes the stages involved in an information system development project, from an initial feasibility study through maintenance of the completed application. SDLC can apply to technical and non-technical systems. In most use cases, a system is an IT technology such as hardware and software. Project and program managers typically take part in SDLC, along with system and software engineers, development teams and end-users.
Every hardware or software system will go through a development process which can be thought as an iterative process with multiple steps. SDLC is used to give a rigid structure and framework to define the phases and steps involved in the development of a system.
SDLC is also an abbreviation for Synchronous Data Link Control and software development life cycle. Software development life cycle is a very similar process to systems development life cycle, but it focuses exclusively on the development life cycle of software.
SDLC models
Various SDLC methodologies have been developed to guide the processes involved, including the original SDLC method, the Waterfall model. Other SDLC models include rapid application development (RAD), joint application development (JAD), the fountain model, the spiral model, build and fix, and synchronize-and-stabilize. Another common model today is called Agile software development.
Frequently, several models are combined into a hybrid methodology. Many of these models are shared with the development of software, such as waterfall or agile. Numerous model frameworks can be adapted to fit into the development of software.
In SDLC, documentation is crucial, regardless of the type of model chosen for any application, and is usually done in parallel with the development process. Some methods work better for specific kinds of projects, but in the final analysis, the most crucial factor for the success of a project may be how closely the particular plan was followed.
Steps in SDLC
SDLC can be made up of multiple steps. There is no concrete set number of steps involved. Around seven or eight steps appear commonly; however, there can be anywhere from five upwards to 12. Typically, the more steps defined in an SDLC model, the more granular the stages are.
In general, an SDLC methodology follows these following steps:
- Analysis: The existing system is evaluated. Deficiencies are identified. This can be done by interviewing users of the system and consulting with support personnel.
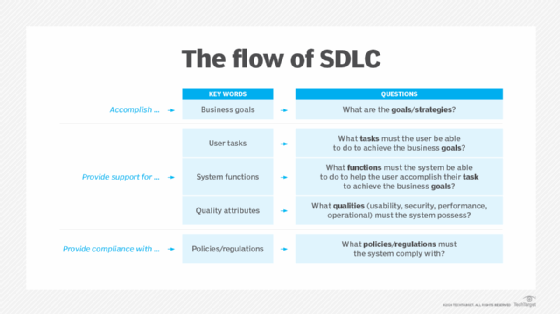
- Plan and requirements: The new system requirements are defined. In particular, the deficiencies in the existing system must be addressed with specific proposals for improvement. Other factors defined include needed features, functions and capabilities.
- Design: The proposed system is designed. Plans are laid out concerning the physical construction, hardware, operating systems, programming, communications and security issues.
- Development: The new system is developed. The new components and programs must be obtained and installed. Users of the system must be trained in its use.
- Testing: All aspects of performance must be tested. If necessary, adjustments must be made at this stage. Tests performed by quality assurance (QA) teams may include systems integration and system testing.
- Deployment: The system is incorporated in a production environment. This can be done in various ways. The new system can be phased in, according to application or location, and the old system gradually replaced. In some cases, it may be more cost-effective to shut down the old system and implement the new system all at once.
- Upkeep and maintenance: This step involves changing and updating the system once it is in place. Hardware or software may need to be upgraded, replaced or changed in some way to better fit the needs of the end-users continuously. Users of the system should be kept up-to-date concerning the latest modifications and procedures.
Other steps which may appear include project initiation, functional specifications, detailed specifications, evaluation, end-of-life and other steps that can be created by splitting previous steps apart further.
Advantages and disadvantages of SDLC
Benefits of abiding by a clearly defined SDLC model include:
- Having a clear view of an entire project, workers involved, estimated costs and timelines.
- Gives project managers a projected base cost of the project.
- Goals and standards are clearly defined.
- Developers can move back a step if something does not go as expected.
Disadvantages, however, can include:
- Due to assumptions made at the beginning of a project, if an unexpected circumstance complicates the development of a system, then it may stockpile into more complications down the road. As an example, if newly installed hardware does not work correctly, then it may increase the time a system is in development, increasing the cost.
- Some methods are not flexible.
- It can be complicated to estimate the overall cost at the beginning of a project.
- Testing at the end of development may slow down some development teams.