wall time
What is wall time?
Wall time, also called real-world time, clock time, wall-clock time or -- more accurately -- elapsed real time, is the amount of time that a program or process takes to run from start to finish as measured by a person. Wall time is important because how a computer measures time and how it is perceived by the user may be different.
Computers measure time based on the CPU clock speed. Any given task will take a certain number of cycles to complete. Most computers run many different tasks each second. The CPU's time is split depending on the needs of the program.
In Linux and Unix, the amount of time that the program is running on the CPU is measured. This is called CPU time. Even though a program may be running for several real seconds, it may only show less than one second of CPU time because the computer was switching between other processes.
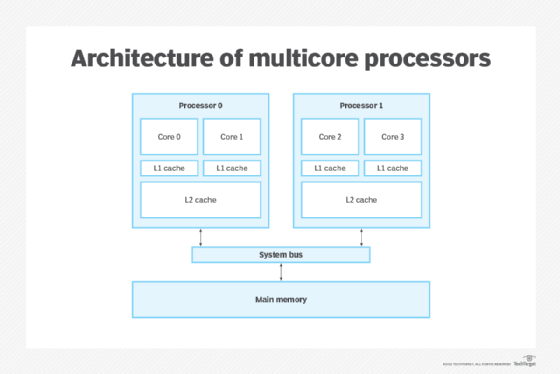
Additionally, modern multicore/multiprocessor CPUs can run several threads at once. This may mean that if a process can run on several threads at once it may use more CPU time than real time.
What influences wall time?
Many factors can influence how much real time a process takes to complete on a computer:

- CPU clock speed and instruction set.
- How many other processes are running.
- Waiting for disk I/O.
- Waiting for network I/O.
If a process takes too much wall time to complete, the user may get impatient. They may think it has hung, frozen or timed out and shut down the process. For the best user experience, it is important to keep programs responsive and to prioritize the amount of wall time it takes over CPU time.
How is wall time minimized?
To illustrate, modern CPUs can operate at rates of about 5 GHz, or 5 billion operations in a second. For most end user computers, CPUs spend more time doing nothing than doing useful work. The CPU can usually process data faster than it can be read off a hard disk or from a network.
To minimize the wall time, some programs keep the data on the disk compressed and spend extra CPU time decompressing the data to keep the much slower process of reading the data off the disk to a minimum.
Some program monitoring and profiling tools give the option to show CPU time or wall time that a process takes. This can help users to optimize for one or the other depending on their needs.
Web page rendering wall time is an important factor for website development. If a website takes too long to load, the user may leave the site. Developers may minify the code, use optimized javascript, and minimize the amount of server calls needed.
Wall time and modern workloads
New workloads also require new methods to minimize the wall time taken for processes.
Video processing may uses dedicated video coprocessors to speed up certain codec encryption, such as Intel QuickSync, Nvidia NVENC, or the Apple silicon media engine.
Artificial intelligence (AI) and machine learning process may employ GPU processing or dedicated circuitry to run in seconds a process that may take minutes or hours on a traditional CPU.
For some life safety processes, such as in medical equipment or transportation safety equipment, having a deterministic and exact amount of wall time is important. In these cases, a real time operating system may be needed.
Explore CPUs vs. GPUs for AI workloads and see how improvements in CPU features help shape selection. Learn about real time operating systems and how they work in internet of things edge computing. Compare Red Hat vs. Ubuntu Linux distributions.
