watt-hour (Wh)
What is a watt hour (Wh)?
The watt-hour, which is symbolized Wh, is a unit of energy equivalent to one watt of power expended for one hour of time. The watt-hour is not a standard unit in any formal system, but it is commonly used in electrical applications.
An energy expenditure of 1 Wh represents 3,600 joules or 3.600 x 103 J. To obtain joules when the watt-hours are known, multiply the number of watt-hours by 3.600 x 103. To obtain watt-hours when joules are known, multiply the number of joules by 2.778 x 10-4.
The watt-hour is most often used to express electrical energy in any form. A quantity of gasoline, oil or coal contains potential energy that is liberated when the fuel is burned.
The heat energy resulting from combustion of such fuels is usually expressed in joules according to the International System of Units or in British thermal units according to the foot-pound-second or English system. If this energy is used to operate an electricity generator, the output of the generator over a period of time can be expressed in watt-hours.
How are energy and watt-hours related?
Energy (E) is equivalent to power (P) multiplied by time (t). To determine energy in watt-hours, power must be expressed in watts, and time must be expressed in hours. Suppose a 60 watt light bulb burns for 3 hours. Then P = 60 and t = 3, so the total energy E in watt-hours is:
E = Pt = 60 x 3 = 180 Wh
If a unit of power and time are not specified in watts and number of hours, respectively, then they must be converted to those units before determining energy in watt-hours.
Importance of watt-hours
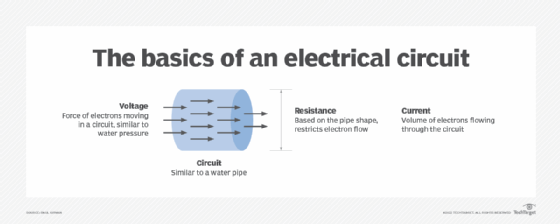
Watt-hours help people understand the amount of power available in various items, such as batteries. Watts represent the amount of energy flowing in a circuit and are computed using this formula:
Watts = Volts (V) x Amperes (A)
Watt-hours are useful in a different way. With a battery that displays its ratings as 10 amp hours (Ah) operating at 12 volts, multiplying the battery voltage by the amp hour rating provides the watt-hours of the battery as shown in the following equation:
12 V x 10 Ah = 120 Wh
Watt-hours are used to measure battery capacity and battery life, estimate number of times the battery can recharge a device and provide a metric for comparing battery performance. Watt-hours are also used as a measure of how much energy a solar panel can produce.
Watt-hours can be used to determine the energy usage of various electrical devices, such as standard light bulbs, over time. Knowing the potential electrical power use of a device also provides insight into when it might need to be replaced. This information is also useful for determining if a device would benefit from being replaced with a more energy efficient version that will help users cut energy consumption and electricity bills and increase energy efficiency.
Difference between watts and watt-hours
Watts describe the level of power at a moment in time, whereas watt-hours describe the amount of power consumption over a period of time.
Speed and distance are also useful analogies to wattage and watt-hours. For example, an automobile may run at 60 miles per hour. That's analogous to watts, in that the car's speed at any moment is 60 mph. If the car travels at 60 mph for one hour, it travels 60 miles in distance. This is analogous to watt-hours.
What about kilowatt hours (kWh)?
A kilowatt-hour is another important energy metric that assumes the generation of 1,000 watts for one hour. Dividing the number of watt-hours by 1,000 results in the equivalent kilowatt-hours as shown in the following equation:
Wh / 1,000 = kWh
Kilowatt-hour is an important metric for measuring performance of high-capacity power systems, such as uninterruptible power systems and diesel generators.
Power supplies and energy use are important parts of designing a data center. Learn more about how to design and build a data center.
