search engine optimization (SEO)
What is search engine optimization?
Search engine optimization is the science of improving a website to increase its visibility when people search for products or services. The more visibility a website has on search engines, the more likely it is that brand captures business.
Website visibility is commonly measured by the placement -- or ranking -- of the site on search engine results pages (SERPs). And companies always vie for the first page, where they are most likely to garner the most attention.
Using Google as an example, SERPs often feature ads at the top of the page. These are positions that businesses are willing to pay for to ensure placement on that first page. Following ads are the regular search listings, which marketers and search engines refer to as organic search results. The SEO process aims to increase a business's organic search results, driving organic search traffic to the site. This enables data marketers to distinguish between traffic that comes to a website from other channels -- such as paid search, social media, referrals and direct -- and the organic search traffic.
Organic search traffic is usually higher-quality traffic because users are actively searching for a specific topic, product or service for which a site might rank. If a user finds that site through the search engine, it can lead to better brand engagement.
How does SEO work?
While there is a way to maximize results, it is almost impossible to fully manipulate search algorithms. Businesses often look to the shortest path toward ideal results with the least amount of effort, but SEO requires a lot of action and time. There is no SEO strategy where something can be changed today with the expectation of clear results tomorrow. SEO is a long-term project, with daily action and constant activity.
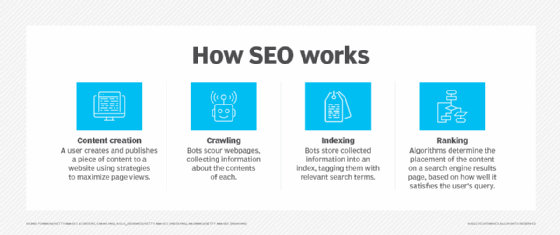
Search engines use bots to crawl all website pages, downloading and storing that information into a collection known as an index. This index is like a library and when someone searches for something in it, the search engine acts as the librarian. The search engine pulls and displays relevant information from the search query and shows users content related to what they were looking for. Search engine algorithms analyze webpages in the index to determine the order those pages should be displayed on the SERP.
What algorithms evaluate for search engine optimization?
There are hundreds of factors that go into what content from the index gets displayed into a SERP. However, they bubble up into five key factors that help determine which results are returned for a search query.
- Meaning of the query. To return relevant results, the algorithm needs to first establish what information the user is searching for. This is known as intent. To understand intent, the algorithm is looking to understand language. Interpreting spelling mistakes, synonyms and that some words mean different things in different contexts all play into the algorithm understanding searcher intent. For example, search engines would need to be able to distinguish between "bass" as a fish and "bass" as an instrument. Intent would be based on additional search terms, historical search, location search and more to display the correct information.
- Relevance of webpages. The algorithm analyzes webpage content to assess whether the sites contain information relevant to what a user is looking for. This comes after intent is established. A basic signal for relevance would be if the webpage includes the keywords used in the search. This includes showing up in the body copy or page headings. But beyond keyword matching, search engines use aggregated interaction data to determine if the page is relevant to the search query. This looks at anonymized data from previous searches to match the page with the query.
- Quality of the content. Search engines' aim is to prioritize the most reliable sources available. The intelligence built into the algorithms can identify which pages demonstrate expertise, authoritativeness and trustworthiness in relation to the intent.
- Usability of webpages. Web design and accessibility play a big part in search rankings. The algorithm looks for how the site appears in different browsers, if it's designed for different device types -- such as desktops, tablets and phones -- and if the page loading times work well for users with slower internet connections.
- Context and settings. Search engines and their algorithms use information from past search history and search settings to help determine which results are most useful to a user at that moment. Country and location can be used to deliver content relevant to the area from which someone is searching. For example, someone searching for "football" in New England would get different results than someone entering for the same query in England.
SEO benefits
Search engine optimization is an essential marketing activity to make a website or business visible on the web. But it also provides several other benefits to companies.
Builds trust and credibility
Sites that rank high on SERPs are considered to be of the highest quality and most trustworthy. Results shown on the first page are the most relevant, resulting in more credibility for the business or website. Having the right content on the site and a good user experience will help the website rank higher.
Provides a competitive advantage
When good SEO is deployed consistently, those that do it more and better will outrank the competition. Many businesses feel they cannot afford to not be on the first page of a search result. But if a team works toward that goal and shows ahead of the competition, they will have a competitive edge.
Reaches more people
SEO helps attract any user with intent at any time, regardless of phase of the customer journey that user is in. It relies on keywords and phrases to attract audiences to specific products and services. Businesses can create a list of keywords for which they would like to rank, then build content around those keywords.
Supports content marketing
By having a list of keywords to rank for and building content around those keywords, users are more likely to find the information they seek. Content and SEO work in harmony with each other. A site will rank better by creating useful, high-quality content that is optimized for those keywords. Ensuring the keywords are present in headings, meta descriptions and the body of the content will improve rankings for those terms.
Here are some tips for creating a content marketing SEO strategy.
Ranks better in local searches
The use of local searches are becoming more common, with users looking for products or services "near me." To improve listings in these searches, a company can create a Google My Business account and optimize the listing for local searches. Along with that and the localized content on the website, a user will be more likely to see local search results in their queries.
Understand web environment
Users that stay up to date on the everchanging internet will be better able to execute the ongoing SEO needs for a website. By staying up to date, businesses can better understand how search works and make more informed decisions on how to change and adapt their strategies.
Relatively inexpensive
To have an effective SEO strategy, companies need to invest in the time and resources to be effective. There are companies that can be hired as SEO experts to manage the strategies, but companies with the right team in place can do it themselves.
Get quantifiable results
There are tools and analytics data that can be tapped into to measure the effectiveness of SEO efforts. Google Analytics can provide comprehensive data around organic traffic. Data includes pages that customers engaged with and keywords used in search. That data can then be cross-referenced with intended actions taken to see how SEO played a role in customer engagement or acquisition.
SEO techniques
There are three main components -- or pillars -- to SEO that go into building effective SEO strategies:
- Technical optimization. This is the process of completing activities when building or maintaining a website to improve SEO. It often has nothing to do with the content that is on the page itself. Some ways to manipulate technical optimization include having an XML sitemap, structuring content in a way that is intuitive to user experience and improving site performance -- such as page load times, correct image sizing and hosting environment.
- On-page optimization. This is the process for ensuring the content on a website is relevant to the users. This content includes the right keywords or phrases in the headings and body of the copy; and ensuring that each page includes meta descriptions, internal links within the site and external links to other reputable sites, and a good URL with the focus keyword. Website administrators use content management systems (CMS) to maintain on-page content.
- Off-page optimization. This technique is deployed to enhance a site's rankings through activities outside of the website. This type of activity is driven largely by backlinks. Businesses can generate these from partnerships, social media marketing and guest blogging on other sites.
These three components help marketers focus on the activities and techniques to build strong rankings for their websites.
Here are some additional techniques to use within each of the three pillars:
- Keyword research and selection. Perform keyword research on the terms for which are most desirable to rank. Businesses should focus on keywords that receive high search volume to be relevant for search engines. Looking at competitors' top performing keywords also gives an opportunity to build a strategy to compete with them.
- Create quality content. When the keyword strategy is in place, the content strategy follows. Pages are more likely to appear higher on SERPs by creating quality content that is relevant to the readers and their search queries.
- Develop unique page titles and meta descriptions. Page titles should include the page's focus keyword. And meta descriptions should be brief summaries of what a user should expect to learn on the page. These elements are displayed in SERPs and will likely be what people use to inform their clicks.
- Use pay per click to supplement organic traffic. Paid advertising can help improve organic click-through rates by giving marketers an outlet to test title tags and meta descriptions that are shown in SERPs. Ensuring a first-page placement, these ads mimic organic search results to see what copy entices users to click. That can be used to adjust page titles and meta descriptions with organic results.
- Use alt text with images. Alt text is used to describe an image on a webpage. This is critical for bots crawling the site to understand what the image represents. It also verbally describes what the image is to people who are visually impaired. This is also another opportunity to input keywords.
- URL slug. A URL slug is the portion of the URL that is unique to a specific page. This is also an area where it is important to put the focus keyword as it relates to what is on the page.
SEO tools
There are hundreds of tools to improve, manage and report on the effectiveness of SEO. Some are free and some aren't. But they all help marketers research keywords, develop strategies and measure the results of ranking higher on SERPs. Here are some common SEO tools used by marketers today:
- Semrush. This platform is used for keyword research and online ranking data. It gives marketers insight into developing and maintaining keyword strategies. Semrush also can be used to measure SEO performance over time.
- Google Analytics and Search Console. This platform provides real-time data on the effectiveness of SEO. Combined with Google's Search Console, marketers can monitor website traffic, optimize rankings and make informed decisions about the appearance of a site's search results.
- Yoast SEO. For websites using WordPress as their CMS, Yoast SEO is a plugin used to improve on-page optimization. Users can define the URL slug, meta description and page title. They can also see how the content on their page may perform in searches. A checklist of items is available so users can ensure their page is as optimized as possible.
- Ahrefs. This tool is used to audit websites and provide keyword, link and ranking profiles. It can also identify which pages perform the best and which ones need improvement.
- SpyFu. This is a competitor keyword research tool for Google Ads. In addition to the keyword research and data it can produce, it gives detailed insight into competitor SEO and pay per click data.
- HubSpot Website Grader. This is a free tool that delivers report cards with actionable insights about SEO performance. It can show if a website is optimized for mobile, measures website performance and gives security recommendations.
- Google Trends. This tool looks for content trends in countries or regions of the world. It finds popular topics and long-tail keywords related to them. It also compares those trends over time.
Learn how long-tail keywords can improve marketing efforts. - Bing Webmaster. This tool enables marketers to see backlink profiles and keyword research. It also has a built-in site scanning feature.
- Consultants. While not exactly a tool to purchase or use for free, consultants have the SEO expertise that some teams lack internally. Good consultants can help develop the right strategies, execute or recommend the long-term plan. They can also report on the metrics to determine success.
Read more here about some other free keyword research tools.
