white paper
What is a white paper?
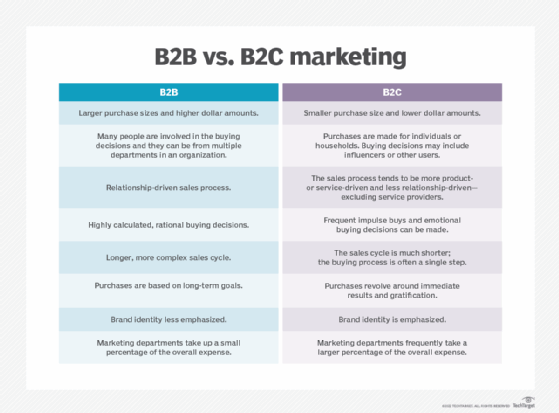
A white paper is an authoritative, research-based document that presents information, expert analysis and an organization or author's insight into a topic or solution to a problem. Companies or vendors use these papers in business-to-business (B2B) marketing models as part of a content marketing strategy. In these contexts, white papers are written to persuade clients, stakeholders, customers and prospective customers to purchase a product or service offered by the organization. They're also used to establish an organization's authority and thought leadership in a field.
White papers are more technical and in-depth than other types of content, such as blogs and case studies. They use research, statistics, expert opinions and original analysis to promote a product, service or methodology. These products and services are often referred to as solutions by technology vendors, as they are claimed to solve a client's particular issue.
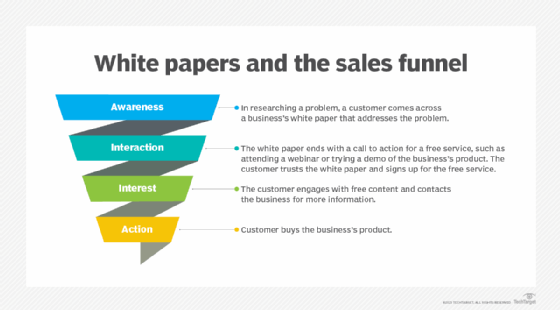
White papers can be effective tools at multiple stages of the sales funnel. They generate sales leads at the top of the funnel, and they're good for nurturing leads already inside it. For instance, a company's blog post may include a call to action linking to a white paper to get a potential customer to make a purchase or to continue fostering a strong customer experience (CX).
Other organizations, such as research institutes, universities, nonprofit groups and government agencies, use white papers to present findings and guidance, and to propose policies and initiative. The term white paper most likely arose in England in the 19th century to distinguish shorter government reports from lengthy ones known as blue books.
Key characteristics of a white paper
White papers in business and technology are characterized by their extensive length and in-depth technical information. The following key characteristics are common in white papers:
- They have an authoritative and objective style that differentiates them from sales pitches and promotional content.
- They're written for a well-defined target audience with CX in mind.
- They're used before a sale for lead generation.
- They're generally at least 2,500 words long.
- They present educational information and facts before offering an expert analysis and proposed solution.
- They include references, citations and footnotes.
- They cite case studies and data, and use data visualization design elements, such as graphs and infographics to support analysis.
- They include numbered lists and bullet points with headings such as "10 Things You Need to Know."
- They use a narrative structure that feels like a factual story about an industry problem and its solution.
- They end with a call to action.
Main purpose of a white paper
Sales and content marketing professionals frequently create and use white papers. Information technology and other companies with complicated products tend to rely on white papers to explain in detail the benefits of their offerings and how they work.
White papers provide these other benefits that make them ideal sales and marketing tools:
- Build trust. White papers speak to readers with authority, using an educational approach, expert analyses and data-backed research.
- Generate leads. They offer valuable insights and data to potential customers who then look to the brand for more of this input.
- Nurture leads. When offered as free content, white papers help educate potential customers about a brand and its offerings.
- Propose solutions. They're a platform for companies to make the case for how their product and services solve specific issues. They let government agencies and nonprofit organizations propose new policies.
- Create brand visibility. White papers build brand awareness both for startups and established companies.
- Increase sales. White papers inform customers and potential customers, and move them closer to buying decisions.

Types of white papers
There are several types of white papers, including the following:
Problem-solution. This is a standard type of white paper that identifies a particular problem of the target audience and proposes a data-driven solution.
Thought leadership. These white papers are written to make an organization appear authoritative and visionary. Thought leadership white papers focus on a current issue or debate, explaining it in a way that informs the audience.
Backgrounder. These papers provide the technical evaluations, key takeaways and promotions of an organization's product or service.
Numbered lists. These are structured with headings and bullet points that highlight the key features of a product or service. For example, a white paper on load balancing , might be "3 Things You Need to Know About Load Balancers."
Technical paper. These white papers provide in-depth technical analyses of a product, service or technology. They are informational documents, written for people who use the product, service or technology on a daily basis.
Market research. The market research white paper is based on new or relevant original research findings that an organization thinks its customers and potential customers should be aware of. It's intended to educate readers about a specific subject matter and demonstrate authority.
Visionary. Visionary white papers reveal an organization's insightful thinking to readers. Similar to the thought leadership white paper, the goal of visionary white papers is to look beyond the scope of current issues toward where the writer thinks a debate or technology is headed.
Examples of white papers
Many professionals in the tech industry rely on white papers to stay educated and knowledgeable about current topics and evolving technology.
White papers often require a reader to fill out a registration form for access. These forms let organizations collect information about the people reading their content, such as a reader's company and role, so they have a better understanding of who their audience is.
Successful white paper examples include the following:
- Gartner's "Reinvent Strategic Workforce Planning."
- McKinsey & Company's "Developer Velocity: How software excellence fuels business performance."
- Satoshi Nakamoto's "Bitcoin: A Peer-to-Peer Electronic Cash System."
- TechTarget's "2022-2023 Media Consumption and Vendor Engagement Study."

How to create a white paper
Writing white papers involves the following steps:
- Define the target audience. Before writing, the author or organization should be aware of sectors the paper is targeting. Organizations often define their audience through customer segmentation.
- Select a topic. The writer selects a topic that is relevant to the target audience. For most companies, topics often center around the field or issue their product addresses. For instance, if a company is selling a network detection and response technology, and has a target audience of executives and IT professionals, a relevant topic would be cybersecurity, its risks and prevention.
- Research the topic. The author conducts extensive research to determine what the target audience wants to know about the topic and how to answer those questions. This research covers both the technical aspects of the topic and search engine optimization research if it's going to be posted online.
- Write a compelling introduction. White papers must have a compelling introduction and a concise, early declaration of the problem statement. A compelling introduction attracts a reader's attention, and a concise problem statement lets the reader know the purpose of the paper.
- Present data and analysis. The white paper should be filled with the most important information, data and original analyses. White papers rely on original research as well as other pieces of market, scientific and technical research available to the general public or hidden behind paywalls or membership requirements. A diversity of sources lends authority to a white paper and can strengthen an author's analysis. This research data should also be provided through engaging visuals such as graphs.
- Present a solution. After analyzing a topic, an author must offer a unique solution to the problem and recommendations for next steps. If a white paper is authoritative and educational enough, the reader will be prepared to learn how they might solve their own version of the problem statement.
- End with a call to action. White papers should end with a clear next step or call to action. This should be an action the reader can take immediately, such as requesting a free demo for a product or service, talking directly to a product expert or signing up for a newsletter. Getting the reader to take this step is the essential purpose behind a white paper.
White papers vs. e-books
White papers and e-books are two distinct, long-form content marketing tools that are often confused.
White papers
These in-depth reports typically aren't more than 20-30 pages and are usually shorter than e-books. White papers are more singularly focused on a topic and used in B2B business models to target specific audiences.
E-books
E-books are longer and broader in scope than white papers. For example, rather than focus on a specific problem within an industry, an e-book might focus on the industry itself. The target audience for e-books is also broader than the audience for white papers. For instance, e-books might offer how-tos and other kinds of guides for the general public. E-books are used more in business-to-consumer (B2C) contexts and tend to be more visually engaging than white papers.
White papers are an important part of generating leads for e-commerce companies. Learn how to create an e-commerce content strategy to improve sales.
