Top 30 IoT interview questions and answers for 2024
Do you or a job candidate have what it takes to meet the demands of IoT? Find out with our 30 questions and answers on planning, deploying and maintaining the internet of things.
The internet of things can benefit a wide range of organizations. But IoT systems require professionals who know their way around the technology and understand what it takes to plan, deploy and maintain an IoT system.
When interviewing individuals for these positions, IT leaders and other decision-makers must assess a candidate's skill levels and ability to comprehend fundamental IoT concepts. They must ask the right IoT interview questions of prospective employees and know what to look for in the answers.
Here are the 30 top interview questions and answers to help with this assessment. These questions can help organizations in need of IoT talent determine whether an individual has the knowledge necessary to meet the demands of the internet of things.
Top IoT interview questions and answers
1. What is IoT?
IoT refers to the internet of things. It is a system of interrelated physical devices that are each assigned a unique identifier. IoT extends internet connectivity beyond traditional platforms, such as PCs, laptops and mobile phones.
This article is part of
Ultimate IoT implementation guide for businesses
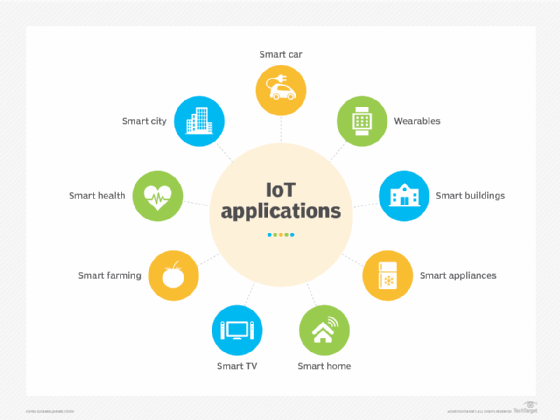
IoT devices can transfer data over a network without requiring human interaction. The devices contain embedded systems that can perform different types of operations, such as collecting information about the surrounding environment, transmitting data over a network, responding to remote commands or carrying out actions based on the collected data. IoT devices can include wearables, implants, vehicles, machinery, smartphones, appliances, computing systems or any other device that can be uniquely identified, transfer data and participate in a network.
2. What industries can benefit from IoT?
A wide range of industries can benefit from IoT, including healthcare, agriculture, manufacturing, automotive, public transportation, utilities and energy, environmental, smart cities, smart homes and consumer devices.
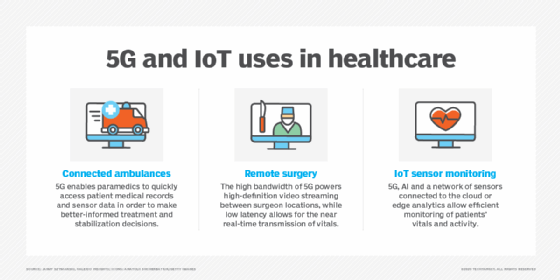
3. How can IoT benefit the healthcare industry?
IoT benefits the healthcare industry -- often through what is called the internet of medical things -- in multiple ways, including the following:
- Wearable devices that can monitor a patient's vitals or health condition and automatically send status updates back to the medical facility.
- Implanted IoT devices that can help maintain a patient's health and automatically provide medical facilities with data about implants and their operations. Some implants can also be adjusted without requiring additional surgery.
- Medical facilities can provide patients with wearables that make it easier to monitor and track them, especially patients who get easily confused or are young. Wearables can also track patient flow to optimize processes, such as admitting or discharging.
- Medical facilities can provide wearables to staff to help improve productivity by tracking their movements and then analyzing the collected data to determine better ways to manage workflow and optimize daily tasks.
- Medical facilities and patients can better manage medications throughout all phases of the medication cycle -- from writing and filling a prescription to tracking usage and reminding patients when it's time to take specific doses.
- Medical facilities can improve how they manage their physical environments and assets, as well as internal operations, while making it easier to automate certain processes, such as tracking and ordering supplies. IoT can potentially also facilitate robotics for carrying out routine tasks.
- Medical facilities can use IoT to connect medical equipment in different locations so they can more effectively share data and coordinate patient efforts, while eliminating extra paperwork and manual processes.
- Medical equipment can use IoT devices to monitor procedures to ensure no errors occur that could jeopardize human health.
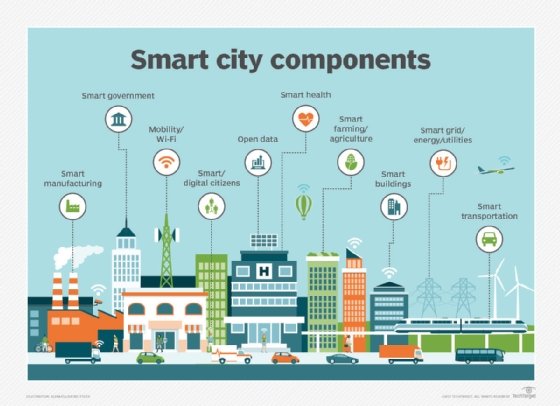
4. What is meant by a smart city in IoT?
A smart city is an urban area that uses IoT technologies to connect city services and enhance their delivery. Smart cities can help reduce crime, optimize public transportation, improve air quality, streamline traffic flow, lower energy use, manage infrastructure, reduce health risks, simplify parking, manage utilities and improve a variety of other processes. Using sensor-driven data collection, the smart city can orchestrate and automate a wide range of services, while reducing costs and making those services easier to access for more people.
Implementing a smart city takes more than just spreading IoT devices around. The city needs a comprehensive infrastructure for deploying and maintaining those devices, as well as for processing, analyzing and storing the data. The system requires sophisticated applications that incorporate advanced technologies, such as artificial intelligence (AI) and predictive analytics. The system must also address security and privacy concerns, as well as interoperability issues that might arise. Not surprisingly, such an effort can take significant time and money, yet the benefits of a smart city could be well worth the effort for the municipality that can make it work.
5. What are the main components of the IoT architecture?
The IoT architecture consists of the following components:
- Smart devices. Include embedded systems for carrying out tasks such as collecting and transmitting data or responding to commands from external control and management systems.
- Data processing platforms. Include the hardware and software necessary to process and analyze the data coming in over the network from the IoT devices.
- Storage platforms. Manage and store the data and interface with the data processing platform to support its operations.
- Network infrastructure. Facilitates communications between the devices and the data processing and storage platforms.
- UI. Enables individuals to connect directly to IoT devices to configure and manage them, as well as verify their status and troubleshoot them. The UI might also provide a way to view the device's collected data or generated logs. This interface is separate from those used to view data collected on the data processing or storage platforms.
There are other ways to categorize IoT architecture. For example, treat data processing and storage platforms as a single component, or the break the data processing platform into multiple components, such as hardware and software.
6. What is an embedded system on an IoT device?
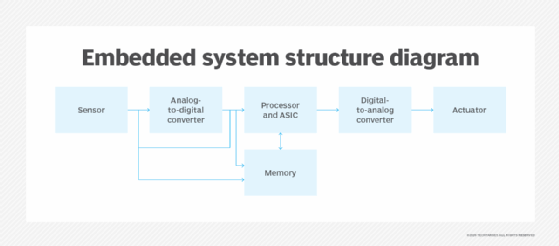
An embedded system is a combination of hardware, software and firmware that's configured for a specific purpose. It's essentially a small computer that can be embedded in mechanical or electrical systems, such as automobiles, industrial equipment, medical devices, smart speakers or digital watches. An embedded system might be programmable or have fixed functionality.
It's generally made up of a processor, memory, power supply and communication ports and includes the software necessary to carry out operations. Some embedded systems might also run a lightweight OS, such as a stripped-down version of Linux.
An embedded system uses communication ports to transmit data from its processor to a peripheral device, which might be a gateway, central data processing platform or another embedded system. The processor might be a microprocessor or a microcontroller, which is a microprocessor that includes integrated memory and peripheral interfaces. To interpret the collected data, the processor uses specialized software stored in memory.
Embedded systems can vary significantly between IoT devices in terms of complexity and function, but they all provide the capacity to process and transmit data.
7. What are the primary hardware components that make up an embedded system?
An embedded system can include any of the following types of hardware components:
- Sensor or other input device. Gathers information from the observable world and converts it to an electrical signal. The type of data gathered depends on the input device.
- Analog-to-digital converter. Changes an electrical signal from analog to digital.
- Processor. Processes the digital data the sensor or other input device collects.
- Memory. Stores specialized software and the digital data the sensor or other input device collects.
- Digital-to-analog converter. Changes the digital data from the processor into analog data.
- Actuator. Takes action based on the data collected from a sensor or other input device.
An embedded system might comprise multiple sensors and actuators. For example, a system might include several sensors that gather environmental information, which is converted and sent to the processor. Once processed, the data is converted again and sent on to several actuators, which carry out prescribed actions.
8. What is a sensor in an IoT device?
A sensor is a physical object that detects and responds to input from its surrounding environment, essentially reading the environment for information. For example, a sensor that measures temperatures within a piece of heavy machinery detects and responds to the temperature within that machinery, as opposed to registering the outside temperature. The information that a sensor gathers is typically transmitted electronically to other components in an embedded system, where it is converted and processed as necessary.
The IoT industry supports many types of sensors, including those that can measure light, heat, motion, moisture, temperature, pressure, proximity, smoke, chemicals, air quality or other environmental conditions. Some IoT devices contain multiple sensors to capture a mix of data. For example, an office building might include smart thermostats that track both temperature and motion. That way, if no one is in the room, the thermostat automatically lowers the heat.
A sensor is different from an actuator, which responds to the data the sensor generates.
9. What are some examples of sensors that can be used in agriculture?
Many sensors are available for agriculture, including the following:
- Airflow. Measures soil's air permeability.
- Acoustic. Measures the level of noise from pests.
- Chemical. Measures levels of a specific chemical, such as ammonium, potassium or nitrate, or measures such conditions as pH levels or presence of a specific ion.
- Electromagnetic. Measures the soil's ability to conduct electrical charge, which can be used to determine characteristics such as water content, organic matter or degree of saturation.
- Electrochemical. Measures the nutrients within the soil.
- Humidity. Measures the moisture within the air, such as in a greenhouse.
- Soil moisture. Measures the wetness of the soil.
10. What is a thermocouple sensor?
A thermocouple sensor is a common type of sensor that measures temperature. The sensor includes two dissimilar electrical metal conductors joined at one end to form an electrical junction, which is where the temperature is measured. The two metal conductors produce a small voltage that can be interpreted to calculate the temperature. Thermocouples come in multiple types and sizes, are inexpensive to build and are highly versatile. They can also measure a wide range of temperatures, making them well suited for a variety of applications, including scientific research, industrial settings, home appliances and other environments.
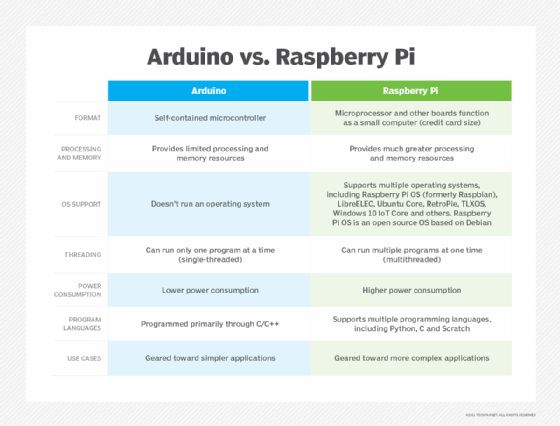
11. What are some of the main differences between Arduino and Raspberry Pi?
Arduino and Raspberry Pi are electronic prototyping platforms used extensively in IoT devices. Table 1 describes some of the differences between the two platforms.
12. What are GPIO pins in Raspberry Pi platforms?
General-purpose I/O (GPIO) is a standard interface that Raspberry Pi and other microcontrollers use to connect to external electronic components. Recent Raspberry Pi models are configured with 40 GPIO pins, which are used for multiple purposes. For example, GPIO pins supply 3.3 volt or 5 volt direct current power, provide a ground for devices, serve as a serial peripheral interface bus, act as a universal asynchronous receiver/transmitter or deliver other functionality. One of the biggest advantages of Raspberry Pi GPIO pins is that IoT developers can control them through software, making them especially flexible and able to serve specific IoT purposes.
13. What role does a gateway play in IoT?
An IoT gateway is a physical device or software program that facilitates communications between IoT devices and the network that carries device data to a centralized platform, such as the public cloud, where data is processed and stored. Smart device gateways and cloud endpoint protection products can move data in both directions, while helping to protect data from being compromised, often employing such techniques as tamper detection, encryption, crypto engines or hardware random number generators. Gateways might also include features that enhance IoT communications, such as caching, buffering, filtering, data cleansing or even data aggregation.
14. What is the OSI model and what communication layers does it define?
The Open Systems Interconnection (OSI) model provides a foundation for internet communication, including IoT systems. The OSI model defines a standard for how devices transfer data and communicate with each other over a network and is divided into seven layers that build on top of each other:
- Layer 1: Physical layer. Transports data using electrical, mechanical or procedural interfaces, sending bits from one device to another along the network.
- Layer 2: Data link layer. A protocol layer that handles how data is moved into and out of a physical link in a network. It also addresses bit transmission errors.
- Layer 3: Network layer. Packages data with the network address information and selects the appropriate network routes. It then forwards the packaged data up the stack to the transport layer.
- Layer 4: Transport layer. Transfers data across a network, while providing error-checking mechanisms and data flow controls.
- Layer 5: Session layer. Establishes, authenticates, coordinates and terminates conversations between applications. It also reestablishes connections after interruptions.
- Layer 6: Presentation layer. Translates and formats the data for the application layer using semantics accepted by the application. It also carries out required encryption and decryption operations.
- Layer 7: Application layer. Enables an end user, whether software or human, to interact with the data through the necessary interfaces.
15. What are some of the protocols used for IoT communication?
The following list includes many of the protocols being used for IoT:
- Advanced Message Queuing Protocol.
- Bluetooth and Bluetooth Low Energy (Bluetooth LE).
- Cellular.
- Constrained Application Protocol.
- Data Distribution Service.
- Extensible Messaging and Presence Protocol.
- Lightweight machine-to-machine.
- Long range and LoRaWAN.
- MQTT.
- Wi-Fi.
- Zigbee.
- Z-Wave.
Cellular IoT protocols, such as LTE-M, narrowband IoT and 5G can also facilitate IoT communications. In fact, 5G promises to play a significant role in the coming onslaught of IoT devices.
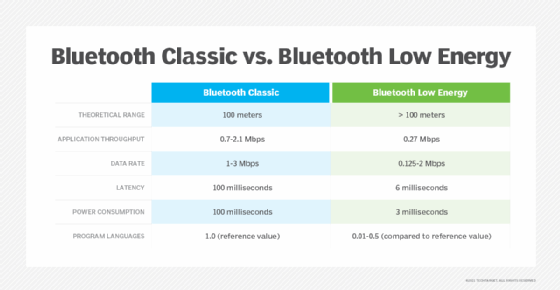
16. What are the main differences between Bluetooth and Bluetooth LE?
Bluetooth, sometimes referred to as Bluetooth Classic, is typically used for different purposes than Bluetooth Low Energy. Bluetooth Classic can handle much more data but consumes a lot more power. Bluetooth LE requires less power but can't exchange nearly as much data. Table 2 provides an overview of some of the specific differences between the two technologies.
17. What impact could IPv6 have on IoT?
Internet Protocol Version 6, commonly referred to as IPv6, is an upgrade from IPv4. One of the most significant changes is IPv6 increases the size of IP addresses from 32 bits to 128 bits. Because of its 32-bit limitation, IPv4 can support only about 4.2 billion addresses, which has already proved insufficient. The mounting number of IoT devices and other platforms that use IP addresses requires a system that can handle future addressing needs. The industry designed IPv6 to accommodate trillions of devices, making it well suited for IoT. IPv6 also promises improvements in security and connectivity. It's the additional IP addresses that take center stage, however, which is why many believe that IPv6 will play a pivotal role in the future success of IoT.
18. What is the Zigbee Alliance?
The Zigbee Alliance is a group of organizations working together to create, evolve and promote open standards for IoT platforms and devices. It's developing global standards for wireless device-to-device IoT communication and certifies products to help ensure interoperability. One of its most well-known efforts is Zigbee, an open standard for implementing low-power, self-organizing mesh networks. Zigbee-certified products can use the same IoT language to connect and communicate with each other, reducing interoperability issues. Zigbee is based on the IEEE 802.15 specification but adds network and security layers in addition to an application framework.
19. What are some use cases for IoT data analytics?
The following use cases represent ways IoT data analytics can benefit organizations:
- Forecasting customer requirements and desires to better plan product features and release cycles, as well as deliver new value-added services.
- Optimizing HVAC equipment in office buildings, shopping malls, medical centers, data centers and other enclosed environments.
- Improving the level of care given to patients with similar conditions, while being able to better understand those conditions and target the needs of specific individuals.
- Optimizing delivery operations, such as scheduling, routing and vehicle maintenance, as well as reducing fuel costs and emissions.
- Acquiring in-depth knowledge of how consumers use their products so a company can develop more strategic marketing campaigns.
- Predicting and identifying potential security threats to better protect data and meet compliance requirements.
- Tracking how utilities are delivered to customers across regions and better understanding their usage patterns.
- Improving agricultural practices to achieve more abundant yet sustainable yields.
- Optimizing manufacturing operations to make better use of equipment and improve workflows.
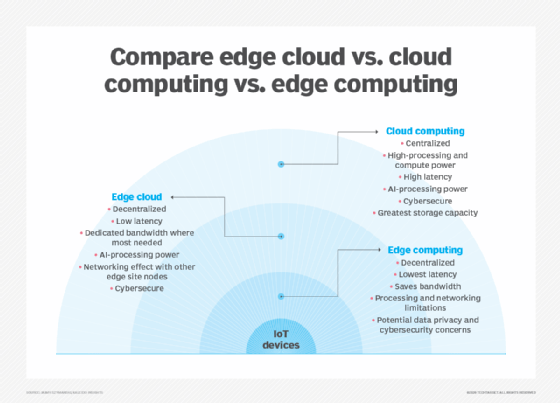
20. How can edge computing benefit IoT?
Edge computing can benefit IoT in a number of ways, including the following:
- Supporting IoT devices in environments with limited network connectivity, such as cruise ships, agricultural settings, offshore oil rigs or other remote locations.
- Reducing network congestion by preprocessing data in an edge environment and then transmitting only the aggregated data to a central repository.
- Reducing latency by processing the data closer to the IoT devices generating that data, resulting in quicker response times.
- Reducing potential security and compliance risks by transmitting less data across the internet or by creating smaller network segments that are easier to manage and troubleshoot.
- Decentralizing massive cloud centers to better serve specific environments and reduce the costs and complexities that come with transmitting, managing, storing and processing large data sets on a centralized platform.
21. How could 5G cellular networks impact IoT?
The coming wave of 5G networks could impact IoT in a variety of ways:
- Higher bandwidth and faster throughputs make it possible to support more advanced use cases, especially those that require quicker response times, such as traffic control systems or automated public transportation.
- Organizations can distribute more sensors to capture a wider range of information about environmental factors or equipment behavior, resulting in more comprehensive analytics and a greater capacity of automating operations both at the industrial level and consumer level.
- 5G could enable IoT on a more comprehensive scale in areas where it might be otherwise difficult to achieve, helping industries such as healthcare and agriculture.
- The faster throughput and ability to handle data from more sensors makes it easier to establish smart cities, which require a higher saturation of IoT devices.
- Manufacturers could use 5G to better track inventory throughout its lifecycle, as well as better control workflows and optimize operations.
- 5G enables organizations and governments to respond more quickly and efficiently to different types of incidents, such as medical emergencies, pipeline leaks, fires, traffic accidents, weather events or natural disasters.
- Automobiles can benefit from 5G as cars become more connected, helping to keep them safer, better maintained and more fuel efficient, while also making the autonomous car more of a reality.
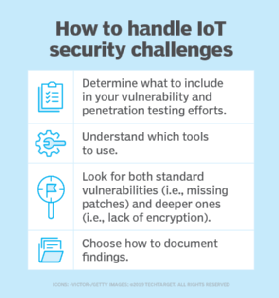
22. What are some of the biggest security vulnerabilities that come with IoT?
Security remains a huge part of IoT. The Open Web Application Security Project has identified the top 10 IoT security vulnerabilities, which include the following:
- Weak, guessable or hardcoded passwords.
- Insecure network services.
- Insecure ecosystem interfaces.
- Lack of secure update mechanisms.
- Use of insecure or outdated components.
- Insufficient privacy protection.
- Insecure data transfer and storage.
- Lack of device management.
- Insecure default settings.
- Lack of physical hardening.
23. What steps can an organization take to protect IoT systems and devices?
An organization can take several steps to protect its IoT systems, including the following:
- Incorporate security at the design phase, with security enabled by default.
- Use public key infrastructures and X.509 certificate to secure IoT devices.
- Use application performance indicators to safeguard data integrity.
- Ensure each device has a unique identifier, and implement endpoint hardening, such as making devices tamper-proof or tamper-evident.
- Use advanced cryptographic algorithms to encrypt data in transit and at rest.
- Protect networks by disabling port forwarding, closing unused ports, blocking unauthorized IP addresses and keeping network software and firmware up to date. Also, implement antimalware, firewalls, intrusion detection systems, intrusion prevention systems and any other necessary protections.
- Use network access control mechanisms to identify and inventory IoT devices connecting to the network.
- Use separate networks for IoT devices that connect directly to the internet.
- Use security gateways to serve as intermediaries between the IoT devices and the network.
- Continuously update and patch any software that participates in the IoT system or is used to manage IoT components.
- Provide security training and education for individuals who participate in the IoT system at any level -- whether planning, deploying, developing or managing.
24. What are the top challenges of implementing an IoT system?
Organizations that want to implement an effective IoT system face a variety of challenges, including the following:
- IoT can generate massive volumes of data, and organizations must be able to effectively manage, store, process and analyze that data to realize the fullest potential from their IoT systems.
- In some circumstances, managing power supplies for IoT devices can be difficult, especially devices in hard-to-reach locations or those that rely on battery power.
- Managing IoT devices can be an overwhelming undertaking even for the most seasoned IT administrators, who must often take extra steps to monitor and manage those devices.
- Maintaining network connectivity for multiple IoT device types can be a significant challenge, especially when those devices are highly distributed or in remote locations, or if bandwidth is severely limited.
- The lack of common IoT standards can make it difficult to deploy and manage large numbers of IoT devices that come from different vendors and are based on proprietary technologies that differ significantly from one another.
- Ensuring the reliability of an IoT system can be difficult because IoT devices are highly distributed and must often contend with other internet traffic. Natural disasters, disruptions in cloud services, power failures, system failures or other conditions can affect the components that make up an IoT system.
- Complying with government regulations represents another significant challenge with IoT, especially if operating in multiple regions or in regions with conflicting or frequently changing regulations.
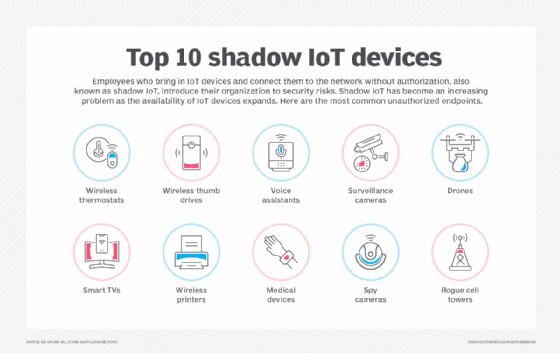
- IoT systems face security threats on many fronts -- botnets, ransomware, domain name server threats, shadow IT, physical vulnerabilities and other sources -- and organizations must be able to protect their IoT devices, network infrastructure, on-premises compute and storage resources, and all the data that comes with IoT.
25. What are the differences between IoT and IIoT?
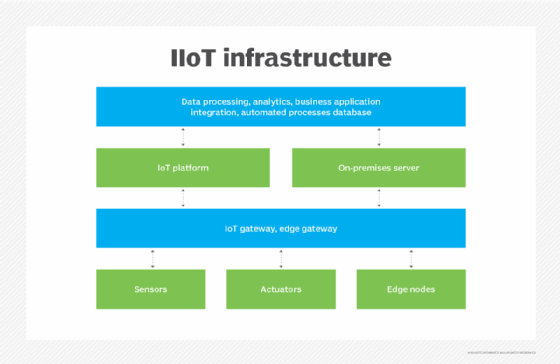
Industrial internet of things (IIoT) is often defined as a subset of IoT that focuses specifically on industrial settings, such as manufacturing, agriculture or oil and gas. However, some people in the industry define IoT and IIoT as two separate efforts, with IoT focused on the consumer side of device connectivity. In either case, IIoT falls squarely on the industrial side of the equation and is concerned primarily with the use of smart sensors and actuators to enhance and automate industrial operations.
Also known as Industry 4.0, IIoT uses smart machines that support machine-to-machine (M2M) technologies or cognitive computing technologies, such as AI, machine learning or deep learning. Some machines even incorporate both types of technologies. Smart machines capture and analyze data in real time and communicate information that can be used to drive business decisions. When compared to IoT in general, IIoT tends to have stricter requirements in such areas as compatibility, security, resilience and precision. Ultimately, IIoT aims to streamline operations, improve workflows, increase productivity and maximize automation.
26. What are the main differences between IoT and M2M?
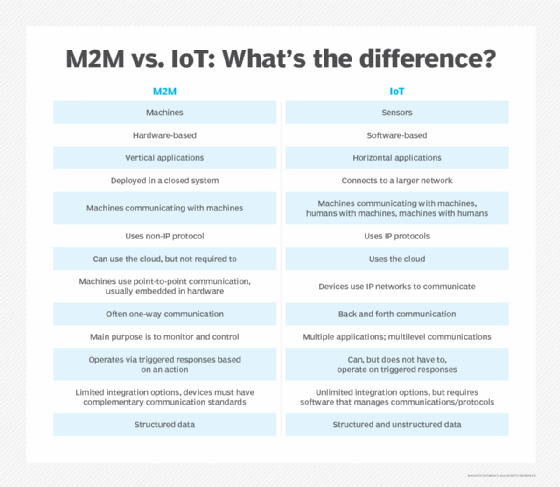
The terms IoT and M2M are sometimes used interchangeably, but they aren’t the same. M2M enables networked devices to interact with each other and carry out operations without human interaction. For example, M2M is often used to enable ATMs to communicate with a central platform. M2M devices use point-to-point communication mechanisms to exchange information using a wired or wireless network. An M2M system typically relies on standard network technologies, such as Ethernet or Wi-Fi, making it cost-effective for establishing M2M communication.
IoT is often considered an evolution of M2M that increases connectivity capabilities to create a much larger network of communicating devices, relying on IP-based technologies to facilitate that communication. Standard M2M systems have limited scalability options and tend to be isolated systems that are best suited for simple device-to-device communication, typically with one machine at a time. IoT has a much broader range that can integrate multiple device architectures into a single ecosystem, with support for simultaneous communications across devices. However, IoT and M2M are similar in that both systems provide a structure for exchanging data between devices without human intervention.
27. What is IoE?
The internet of everything (IoE) is a conceptual leap that reaches beyond IoT -- which focuses on things -- into an expanded realm of connectivity that incorporates people, process and data, along with things. The concept of IoE originated with Cisco, which stated that the "benefit of IoE is derived from the compound impact of connecting people, process, data and things, and the value this increased connectedness creates as 'everything' comes online."
By comparison, IoT refers only to the networked connection of physical objects, while IoE expands this network to include people-to-people and people-to-machine connections. Cisco and other proponents believe that those who harness IoE will be able to capture new value by "connecting the unconnected."
28. Which types of testing should be performed on an IoT system?
Enterprises implementing an IoT system should conduct a variety of testing, including the following types:
- Usability. Ensures IoT device offers optimal UX, based on the environment in which the device will typically be used.
- Functionality. Ensures all features on the IoT device work as designed.
- Security. Ensures that IoT devices, software and infrastructure -- network, compute and storage -- meet all applicable security requirements and regulatory standards.
- Data integrity. Ensures the integrity of the data across communication channels, throughout processing operations and within storage platforms.
- Performance. Ensures that IoT devices, software and infrastructure provide the performance necessary to deliver uninterrupted services within the expected time frame.
- Scalability. Ensures the IoT system can scale as necessary to meet evolving requirements without impacting performance or disrupting services.
- Reliability. Ensures the IoT devices and systems can deliver the expected level of services without incurring unnecessary or prolonged downtimes.
- Connectivity. Ensures IoT devices and system components can properly communicate without disruptions in connectivity or data transfer operations and can automatically recover from any disruptions without incurring any data loss.
- Compatibility. Ensures compatibility issues between IoT devices and other system components are identified and addressed and that devices can be added, moved or removed without disruptions to services.
- Exploratory. Ensures the IoT system works as expected under real-world conditions, while detecting issues that might not be caught by other types of testing.
29. What is IoT asset tracking?
IoT asset tracking refers to the process of using IoT to monitor the location of an organization’s physical assets, no matter where they’re located or how they’re being used. Assets can include anything from delivery vans to medical equipment to construction tools. Rather than try to track these assets manually, a company can use IoT asset tracking to automatically identify the location and movement of each tracked device, helping save time and ensure greater accuracy. At the same time, organizations can use asset tracking to simplify inventory maintenance, improve asset use, and optimize workflows and daily operations.
30. What is Thingful?
Thingful is an IoT search engine that provides a geographical index of real-time data from connected devices around the world, using data from millions of existing public IoT data resources. The devices that generate the data can span a variety of use cases, such as energy, weather, aviation, shipping, air quality or animal tracking. The search engine enables users to find devices, data sets and real-time data sources through geolocation and presents them using a proprietary IoT device search ranking methodology. With Thingful, users can interoperate with millions of connected objects and sensors across the planet that generate real-time open data.
IoT managers can use Thingful to analyze trends, discover patterns and identify anomalies, as well as solve problems using existing data. The search engine can also help them kick-start IoT innovation in a community and help residents of that community learn about the IoT data and environment around them. Thingful is well suited to community engagement initiatives built around data and data education. Users can create accounts, set up time-series experiments, and generate statistical and analytical visualizations. They can also integrate local IoT data repositories.
Robert Sheldon is a technical consultant and freelance technology writer. He has written numerous books, articles and training materials related to Windows, databases, business intelligence and other areas of technology.







