help desk
What is a help desk?
A help desk is the individual, group, organizational function or external service that an IT user calls to get help with a problem. A help desk can be as simple as a physical desk where a support person takes calls. It also can be a global organization that accepts support requests submitted online or in person from around the world. The help desk function is often outsourced to support specialists.
Typically, the term refers to centralized help provided to users within an enterprise. A related term is call center, a place that customers call to place orders, track shipments, get help with products and so forth.
Some common names for a help desk are the following:
- computer support center
- IT response center
- customer support center
- IT solutions center
- resource center
- information center
- technical support center
Most organizations of any size provide an IT help desk to support their employees and other internal users of computers, software and networks. These internal help desks generally provide IT support for all IT hardware, software and networking products in use in the organization.
Technology vendors also provide help desk support to their customer base through customer support help desks. These services are an important part of technology vendors' customer satisfaction efforts. They are often integrated with customer relationship management, or CRM, systems.
What does a help desk do?
In its simplest form, a help desk consists of a phone number and one person who can solve customer problems in Real Time. This approach does not scale well, so more mature help desks incorporate support teams of customer support professionals who perform some or all the following functions:
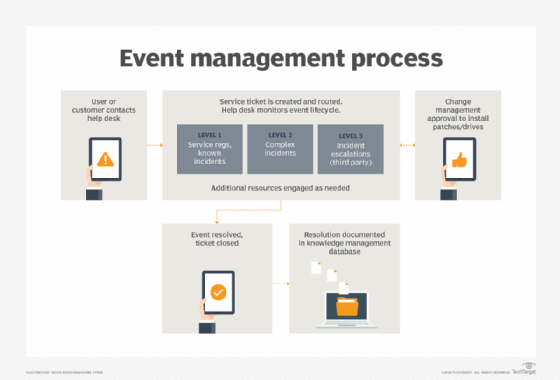
- Help request acceptance. Help desk teams handle requests in real time that customers or other authorized users submit by email, phone or messaging apps.
- Ticket creation. Staff use help desk software to create help desk tickets that track customer support When an initial call can't be resolved immediately, help desk staff use the ticketing system to make sure customer requests are resolved in a timely fashion.
- Ticket management. Either a person or software routes help tickets to the right help desk Help desk ticketing software is designed to ensure that service requests are routed to the right service teams.
- Response. Staff respond to customer questions submitted in help desk tickets and resolve problems.
- Escalation. When the customer support professional can't resolve a request, the next step is to route the ticket to another team member or escalate it to a next tier level. Escalation of a ticket should only occur after initially responding service desk staffers exhaust their own resources for solving a customer problem.
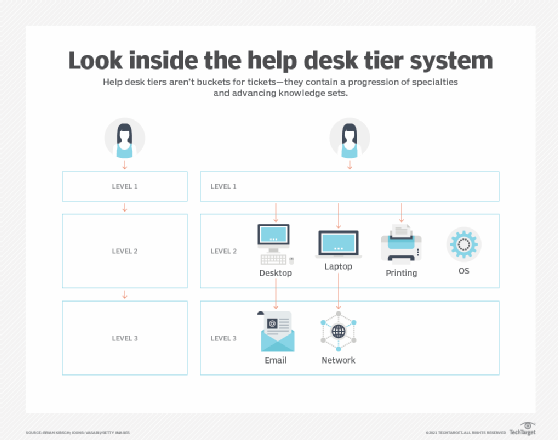
![diagram of help desk tier system levels]()
The help desk tier system enables rapid escalation of more complex issues, while also resolving simpler tickets faster. - Knowledge base. Help desk staff use a help desk knowledge base to discover whether a customer issue has already been identified and, if so, what the resolution was. Staff should be able to add and update content in the knowledge base as they uncover novel customer requests.
In larger companies, a help desk may consist of a customer service team. This is a group of experts that uses help desk software to track the status of problems. They also use other special software to analyze problems and monitor issues such as the status of a company's telecommunications network.
Help desk software is also used to track customer satisfaction and customer experience (CX).
Why are help desks important?
Technology vendors' help desks are critical for customer satisfaction. Many vendors view the help desk as the primary point of contact for end users. The quality of customer interaction can determine how satisfied the customer is.
Help desks that provide internal technical support are critical for organizational effectiveness. A good help desk can boost productivity by resolving basic issues quickly, while escalating unusual and unique issues to the team or individual best qualified to resolve them.
Some functions of a good help desk are the following:
- Centralized support channels. Good help desks provide an inbound channel for support requests. They often have a centralized gateway for support through a help desk hotline or website and keep help desk workflows transparent for users.
- Prioritization of response to customer issues. Good help desks optimize response time. They do this by monitoring key metrics, such as how fast help desk staff respond to new tickets and how quickly tickets are resolved.
- Identification of product issues. Properly functioning help desks use metrics to track issues that are causing a lot of calls for help.
- Customer interaction. A help desk may be the primary way customers interact with a technology vendor. The best help desks provide a communication channel between the organization and users or customers.
Modern help desks can be expensive to set up and maintain, but externally facing, customer service help desks are often an important part of an organization's marketing effort. Internally facing help desks can also contribute to the organization's bottom line by improving operating efficiency for all employees.
Types of help desks
While every help desk is different, most fall into one of the following four categories:
- Web or cloud help desks operate entirely online. This enables organizations to distribute their staff and computing resources and still be able to respond to customer requests, no matter where they are.
- On-premises help desks operate in a physical location.
- Enterprise help desks operate in enterprises and other large organizations.
- Open source help desks are ones that either use Open Source software or are designed to be open and accessible to anyone, as opposed to help desks with paywalls or other limitations on who can access them.
To optimize help desk functions, especially for improved CX, large organizations build out their help desk function in ways that combine these different types of help desk. This enables customers to have access to help functions over their preferred communication channels.
For example, some enterprises provide cloud-based help desks for global support. At the same time, they also incorporate on-premises help centers in branch offices to provide immediate access to expertise, as well as commonly requested hardware and software.
Some help desks use automation to provide free or low-cost self-service support. This type of help desk typically provides a self-service portal through which internal or external customers can submit requests for common support tasks. Incoming requests are entered into the system, and automated ticket routing in the help desk system routes requests to the appropriate destination. Help desk systems often use automation for responses to common questions and to facilitate workflows and asset management.
Characteristics of a good help desk
No matter the type of help desk, the best help desk software products share the following characteristics:
- support help desk management functions;
- provide a framework for entering new tickets at the initial point of contact with the customer;
- offer service management tools to monitor and manage allocation and completion of customer requests; and
- provide routing capabilities for assigning issues to the team or person best suited to respond to them.
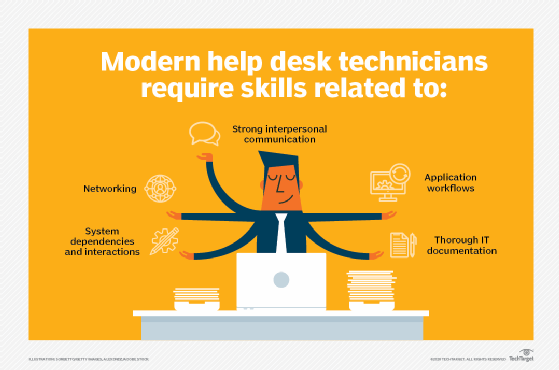
Help desks ultimately depend on the people who provide help to customers. While technical knowledge of supported products is important, a lack of knowledge can easily be supplanted with training and a good knowledge base for the product line.
More important qualities for help desk staff include the following:
- Active listening. Help desk staff communicating with customers or end users do best when they are good listeners, capable of staying quiet while customers are speaking and asking the right questions.
- Empathy. In most cases, customers only use the help desk when they are under the stress of not being able to do their jobs; no matter how trivial the solution, help desk staff with an empathetic style are most effective.
- Curiosity. While it is not necessary -- or possible -- for a help desk agent to know everything about all supported products, agents must have a good sense of curiosity about how their support products work.
- Patience. This skill can be more important than product knowledge for good CX.
These soft skills are more important than technical knowledge and technical skills. Gaps in knowledge can be easily remedied, but learning social interaction and other soft skills isn't as easy.
How to choose a help desk platform
It is difficult to imagine a modern help desk being run without software. Using help desk software enables organizations to implement their IT service management (ITSM) processes. ITSM is an important component of any help desk and should be based on the ITIL -- originally known as the IT Infrastructure Library -- best practice framework.
Organizations use third-party software designed to support key help desk features, such as the following:
- Ticket management. The fundamental data unit in help desk software is the support ticket or trouble ticket. Ticket management is a help desk software feature that handles creation, modification and completion of these tickets.
- Point of contact. Good help desk software can connect customers with the right person who can resolve their issue, while also maintaining an open channel for teams.
- Knowledge base. Help desk agents are encouraged to document their tickets. Good help desk software provides a mechanism for creating and accessing this information through a knowledge base.
- Automation. Help desk automation can improve use of human resources, especially for growing help desks where team performance is important. Basic tasks can be automated through a help desk front end that automates the ticket creation process or can be implemented to automate workflows and notifications, as well as accommodate staff availability.
- Escalation. For most help desks, the first point of contact for the customer is a generalist support staffer who can answer simple or basic questions. Help desk software should support escalation of more complex issues to staffers with expertise in different areas.
- Dashboards. Help desk software should provide dashboards, both for help desk agents and managers. Dashboards give staff and managers a tool for tracking tickets and assessing performance of individual contributors.
A good help desk can be a competitive advantage, but help desks are only as good as the people working in them. Learn the keys to building an efficient help desk staffing model for your organization.