What is DOS (Disk Operating System)?
A DOS, or disk operating system, is an operating system (OS) that runs from a disk drive. The term can also refer to a particular family of disk operating systems, most commonly MS-DOS (Microsoft DOS). MS-DOS was the main operating system for personal computers (PCs) until 1995, when its popularity waned due to the introduction of the more user-friendly, graphical user interface (GUI)-based Windows 95 operating system.
History of DOS
Early computers of the 1940s and 1950s did not have disk drives. Instead, they were hard-wired to carry out specific computations. Later computers were able to store instructions loaded into the computer's memory using paper-based media like punch cards and still later, using magnetic tapes. Computer memory space was limited, and when the instructions to control a computer were moved onto a disk drive, such as a floppy disk or internal hard disk drive (HDD), it was considered cutting-edge technology.
An operating system is the software that provides the instructions that control a computer's hardware components (memory, processor, etc.) and peripheral devices, as well as allows other software programs to function. The instructions might be stored in the HDD or other storage medium. A DOS is a specific type of OS that runs from the computer's HDD and provides a command-line interface (CLI) to allow users to access and control the system and its various components by typing commands using a keyboard. The use of a CLI is the chief difference between disk operating systems and modern GUI-based operating systems.
The term DOS is also used to describe several similar command-line disk operating systems. Early computers, such as the Commodore 64, Atari 800 and Apple II, all featured a disk operating system: Commodore Business Machines DOS, Atari DOS and Apple DOS, respectively. DOS/360 was an OS for IBM mainframes, which first appeared in 1966, but it is unrelated to the 8086-based DOS of the 1980s used on personal computers.
How does a disk operating system work?
When a computer is powered on, it goes through various steps called the boot process. When running a disk operating system, these six booting steps are standard:
- The read-only memory (ROM) bootstrap loader reads the Master Boot Record and passes control over to it.
- The boot record loads the disk operating system into memory, which takes control of the machine.
- The computer transfers data stored on a magnetic disk to its main memory, the random access memory (RAM).
- It also transfers data to external devices attached to the computer, such as a computer screen or printer.
- The computer provides various application programming interfaces for programs like character input/output (I/O), memory management, program loading and termination, as well as handling user input via a keyboard.
- The OS also provides file system management that organizes, reads and writes files on storage. The management system uses a hierarchical structure of directories, subdirectories and files.
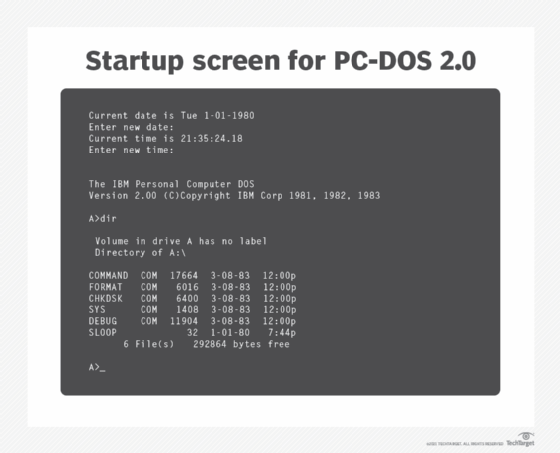
DOS and command-line interface
Because DOS has a character-based interface rather than a GUI, its users must type textual commands in its command line to indicate the actions they want the OS to perform, such as finding a file or running a specific program. The command line process can be complex and tedious, which is why nongraphical OSes are becoming obsolete.
That said, nongraphical OSes use minimal system resources; they can be lightweight, fast and flexible. Also, users who know the operating system's standard commands might find it easier to use than a GUI-based OS, particularly if they want to do the following:
- Troubleshoot hardware or software issues.
- Recover data from a corrupted HDD.
- Create HDD partitions.
- Run antivirus software.
- Run legacy software.
- Set up and configure the system BIOS.
- Set up file/data backup.
- Update system date/clock settings.
DOS features
The main features of all disk operating systems are as follows:
- CLI. There is no GUI in any DOS, so mouse inputs are not accepted. It is a character-based interface system where all commands are entered in text at the command-line prompt.
- Prompt. Disk operating systems provide a visual message, known as a prompt, that provides the location of the current directory or folder and enables users to enter various commands from the keyboard.
- Management. A DOS is useful to manage a computer's files, I/O system and memory.
- Batch files. Disk operating systems support batch files that are macros that can be used to automate groups of commands to simplify tasks, and save time and effort.
- Kernel. The DOS kernel functions as the brain of the OS; it manages the computer's fundamental operations (memory allocation, file access, etc.) and provides an interface for the computer and its programs to interact with each other.
- Data recovery capabilities. Booting a computer from the DOS can help recover data in the event of an expected event, such as a crash or hard drive corruption.
DOS limitations
Although it was a ubiquitous operating system, DOS does have some limitations:
- No built-in security. It does not have built-in security, such as file ownership and permissions.
- No multiusers or multitasking. As single-task operating systems, disk operating systems do not support multiusers or multitasking. Thus, only one program can run at a time (even though it provides direct access to the basic I/O system and underlying hardware).
- Challenging interface. The CLI, in which a user must type in commands, requires the user to remember commands to run programs and do other OS tasks.
- Unexpected output. A small mistake in typing the command can result in unexpected or unwanted consequences. For example, a user might want to list the files in the current directory by typing cd \directory_name. However, that command changes the current working directory to the named directory. To list the contents of a folder, the command dir should be used.
- Slow updating of disk directory information. Some disk operating systems like MS-DOS do not update the disk directory information until a file is closed by the application, which can keep the file in an unsafe state and result in programming issues.
Common DOS commands
MS-DOS is not case-sensitive, so commands can be typed in either uppercase or lowercase. However, other disk operating systems have case-sensitive CLIs. DOS commands include the following:
Common DOS commands
MS-DOS is not case-sensitive, so commands can be typed in either uppercase or lowercase. However, other disk operating systems have case-sensitive CLIs. DOS commands include the following.
| Command | What it does | Example |
| cd | Changes directory | Type cd c:\techtarget in the command line to change the working directory to c:\techtarget. |
| cls | Clears all the contents on the screen, leaving only the command prompt | Type cls in the command line. |
| copy | Copies one or more files to another location | Type copy c:\techtarget\file.txt c:\techtarget\file2.txt to copy c:\techtarget\file.txt to c:\techtarget\file2.txt. |
| del | Deletes one or more files | Type del c:\techtarget\file2.txt to delete the file file.txt from the directory c:\techtarget. |
| deltree | Deletes all files and subdirectories from a computer | Type deltree c:\techtarget\drafts to delete the directory drafts, including all files and subdirectories contained in it. |
| dir | Displays a list of files and directories in a directory | Type dir c:\techtarget to display a list of files and directories in the directory c:\techtarget. |
| format | Formats a disk for DOS files | Type format e: to format the disk in drive e: for use with DOS. |
| help | Lists the available commands or more information about a specific command | Type help del to display information about the del command and how to use it. Most commands have optional switches that are explained in the help information. |
| mkdir or md | Creates a new subdirectory | Type mkdir c:\techtarget\drafts to create the subdirectory drafts in the c:\techtarget directory. |
| move | Moves files or directories from one directory to another or from one drive to another | Type move c:\techtarget\file.txt c:\techtarget\drafts\file.txt to move c:\techtarget\file.txt to c:\techtarget\drafts\file.txt. |
| ren or rename | Changes the name of a file or directory | Type ren c:\techtarget\file.txt c:\techtarget\file2.txt to rename the file c:\techtarget\file.txt to c:\techtarget\file2.txt. |
| type | Displays the contents of a file on the screen | Type type c:\myfile.txt to show the contents of the myfile.txt file. |
| * | A wildcard character that represents one or more characters a group of files has in common | Type copy c:\techtarget\*.txt c:\techtarget\drafts to copy all files with the extension of .txt to c:\techtarget\drafts. |
| ? | A wildcard character that represents a single character a group of files has in common | Type copy c:\techtarget\document?.txt c:\techtarget\drafts to copy files named document1.txt, document2.txt and so on to c:\techtarget\drafts. |
More history and future of DOS
The arrival of the microprocessor in the 1970s started a computing revolution, and the market for personal computers (PCs) began to boom. IBM released the IBM 5150 Personal Computer in August 1981. To speed up the development of this new computer, IBM decided to license various components from other companies.
IBM's first choice for an OS was the CP/M-86 software from Digital Research, but disagreements over nondisclosure agreements and licensing led IBM to choose a CP/M-like OS from Microsoft that was originally called QDOS 86-DOS.
Microsoft bought the rights to market QDOS 86-DOS in 1980. This OS was created by Tim Paterson at Seattle Computer Products (SCP) and was originally called QDOS, an acronym of Quick and Dirty OS. The number "86" refers to the fact that the OS was originally designed to be used with the Intel 8086 processor. After leaving SCP for Microsoft in 1981, Paterson worked on the PC-DOS version of 86-DOS for IBM's PC. PC-DOS was the first widely installed DOS used in PCs running on Intel 8086.
Microsoft produced its own almost identical version of PC-DOS called MS-DOS, which was first released in 1981. As PC sales grew, the ubiquity of MS-DOS grew as well. Subsequent versions of the OS provided improved performance and included additional functionalities, such as support for foreign and extended characters and larger HDDs. Later versions of MS-DOS also enhanced memory management, featured an improved text editor, and provided network support.
When Microsoft first introduced Windows as a GUI for MS-DOS, early users had to type "WIN" at the DOS prompt to launch the Windows program. Windows has since evolved from being a GUI program running under MS-DOS to a full OS taking over as the default OS, though it was not until Windows XP that consumer versions of Windows stopped relying on the DOS program win.com to bootstrap the Windows kernel.
The last retail version of MS-DOS was MS-DOS 6.22; PC-DOS 2000 was the last retail release of PC-DOS. MS-DOS was still bundled as part of Windows but no longer required a separate software license. It can still be run under Windows using a command processor that emulates the MS-DOS interface. There is also an open source version of DOS called FreeDOS that is based on and compatible with MS-DOS. Other versions of these OSes include DR-DOS, ROM-DOS and PTS-DOS (PhysTechSoft DOS).
Because of the many legacy applications that they support, disk operating systems will likely continue to be used for the foreseeable future. Today, they can be used for simple embedded systems or other use cases because they provide machine independence and because the licensing costs are zero for free or open source OSes.
That said, these legacy OSes present critical security problems that make it hard to safeguard them against modern cyberattacks such as SQL injections, man-in-the-middle (MitM) attacks, zero-day vulnerabilities, and more familiar attacks from viruses, worms, ransomware and Trojans.
Disk operating systems played a significant role in the early development of personal computing. Today, some 55 years after their initial development, they hold a place as one of the most important types of OSes in the history of computing.
The latest Microsoft OS is Windows 11. Check out this Windows 11 crash course for desktop admins and Microsoft users, and explore what you need to know when planning to upgrade to Windows 11.
Note: For disk operating system, the acronym used is always DOS (all three letters in uppercase). The acronym DoS with a lowercase "o" is short for denial of service, a method of attacking a networked computer by sending it an abnormally high number of requests in order to exhaust its resources so that genuine users cannot gain access.






